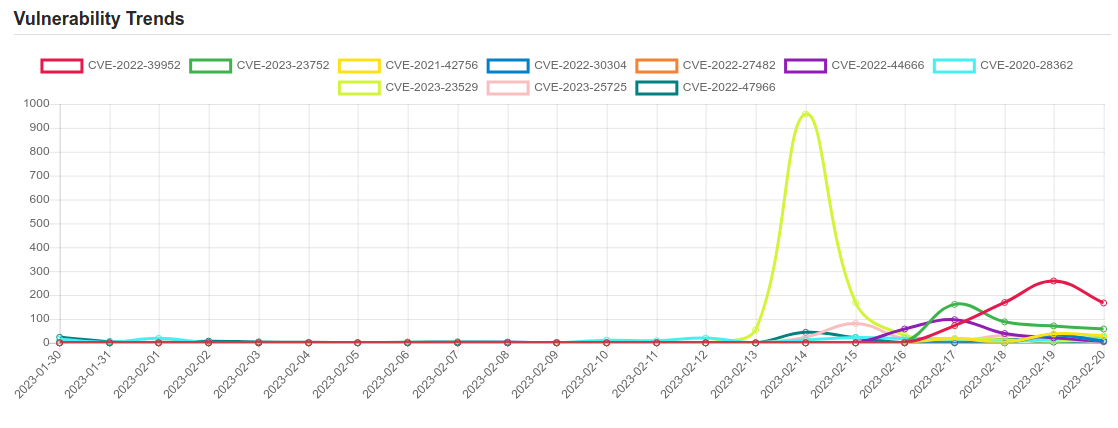
Daily Vulnerability Trends: Tue Feb 21 2023
| CVE NAME | CVE Description |
| CVE-2022-47966 | Multiple Zoho ManageEngine on-premise products, such as ServiceDesk Plus through 14003, allow remote code execution due to use of Apache xmlsec (aka XML Security for Java) 1.4.1, because the xmlsec XSLT features, by design in that version, make the application responsible for certain security protections, and the ManageEngine applications did not provide those protections. |
| CVE-2023-20032 | No description provided |
| CVE-2022-47986 | IBM Aspera Faspex 4.4.2 Patch Level 1 and earlier could allow a remote attacker to execute arbitrary code on the system, caused by a YAML deserialization flaw. By sending a specially crafted obsolete API call, an attacker could exploit this vulnerability to execute arbitrary code on the system. The obsolete API call was removed in Faspex 4.4.2 PL2. IBM X-Force ID: 243512. |
| CVE-2022-27677 | No description provided |
| CVE-2022-42475 | A heap-based buffer overflow vulnerability [CWE-122] in FortiOS SSL-VPN 7.2.0 through 7.2.2, 7.0.0 through 7.0.8, 6.4.0 through 6.4.10, 6.2.0 through 6.2.11, 6.0.15 and earlier and FortiProxy SSL-VPN 7.2.0 through 7.2.1, 7.0.7 and earlier may allow a remote unauthenticated attacker to execute arbitrary code or commands via specifically crafted requests. |
| CVE-2022-45788 | A CWE-754: Improper Check for Unusual or Exceptional Conditions vulnerability exists that could cause arbitrary code execution, denial of service and loss of confidentiality & integrity when a malicious project file is loaded onto the controller. Affected Products: EcoStruxure™ Control Expert (All Versions), EcoStruxure™ Process Expert (Versions prior to V2020), Modicon M340 CPU – part numbers BMXP34* (All Versions), Modicon M580 CPU – part numbers BMEP* and BMEH* (All Versions), Modicon M580 CPU Safety – part numbers BMEP58*S and BMEH58*S (All Versions), Modicon Momentum Unity M1E Processor – 171CBU* (All Versions), Modicon MC80 – BMKC80 (All Versions), Legacy Modicon Quantum – 140CPU65* and Premium CPUs – TSXP57* (All Versions) |
| CVE-2023-21823 | Windows Graphics Component Remote Code Execution Vulnerability |
| CVE-2019-0708 | A remote code execution vulnerability exists in Remote Desktop Services formerly known as Terminal Services when an unauthenticated attacker connects to the target system using RDP and sends specially crafted requests, aka ‘Remote Desktop Services Remote Code Execution Vulnerability’. |
| CVE-2023-0669 | Fortra (formerly, HelpSystems) GoAnywhere MFT suffers from a pre-authentication command injection vulnerability in the License Response Servlet due to deserializing an arbitrary attacker-controlled object. This issue was patched in version 7.1.2. |
| CVE-2021-21974 | OpenSLP as used in ESXi (7.0 before ESXi70U1c-17325551, 6.7 before ESXi670-202102401-SG, 6.5 before ESXi650-202102101-SG) has a heap-overflow vulnerability. A malicious actor residing within the same network segment as ESXi who has access to port 427 may be able to trigger the heap-overflow issue in OpenSLP service resulting in remote code execution. |
| CVE-2023-21715 | Microsoft Publisher Security Features Bypass Vulnerability |
| CVE-2022-39952 | A external control of file name or path in Fortinet FortiNAC versions 9.4.0, 9.2.0 through 9.2.5, 9.1.0 through 9.1.7, 8.8.0 through 8.8.11, 8.7.0 through 8.7.6, 8.6.0 through 8.6.5, 8.5.0 through 8.5.4, 8.3.7 may allow an unauthenticated attacker to execute unauthorized code or commands via specifically crafted HTTP request. |
| CVE-2023-23752 | An issue was discovered in Joomla! 4.0.0 through 4.2.7. An improper access check allows unauthorized access to webservice endpoints. |
| CVE-2021-42756 | Multiple stack-based buffer overflow vulnerabilities [CWE-121] in the proxy daemon of FortiWeb 5.x all versions, 6.0.7 and below, 6.1.2 and below, 6.2.6 and below, 6.3.16 and below, 6.4 all versions may allow an unauthenticated remote attacker to achieve arbitrary code execution via specifically crafted HTTP requests. |
| CVE-2022-30304 | An improper neutralization of input during web page generation vulnerability [CWE-79] in FortiAnalyzer versions prior to 7.2.1, 7.0.4 and 6.4.8 may allow a remote unauthenticated attacker to perform a stored cross site scripting (XSS) attack via the URL parameter observed in the FortiWeb attack event logview in FortiAnalyzer. |
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on Patreon using the button below
To keep up to date follow us on the below channels.







![CACTUS Ransomware Victim: https://www[.]ebir[.]com/ 10 image](https://www.redpacketsecurity.com/wp-content/uploads/2023/09/image-300x291.png)