Microsoft disclosed technical details of a vulnerability in Apple macOS that could be exploited by an attacker to bypass Gatekeeper
Microsoft disclosed technical details of a vulnerability in Apple macOS that could be exploited by an attacker to bypass Gatekeeper.
Microsoft has disclosed details of a now-fixed security vulnerability dubbed Achilles (CVE-2022-42821, CVSS score: 5.5) in Apple macOS that could be exploited by threat actors to bypass the Gatekeeper security feature.
The Apple Gatekeeper is designed to protect OS X users by performing a number of checks before allowing an App to run. In fact, you will not be able to execute code that wasn’t signed by an Apple developer, you will not be able to run apps that weren’t downloaded from Apple’s store if the device is not jailbreaked of course.
The flaw was discovered on July 27, 2022, by Jonathan Bar Or from Microsoft, it is a logic issue that was addressed with improved checks.
“On July 27, 2022, Microsoft discovered a vulnerability in macOS that can allow attackers to bypass application execution restrictions imposed by Apple’s Gatekeeper security mechanism, designed to ensure only trusted apps run on Mac devices. We developed a proof-of-concept exploit to demonstrate the vulnerability, which we call “Achilles”.” reads the post published by Microsoft.
Microsoft researchers explained that Gatekeeper bypasses can be used by threat actors to install malware on macOS systems.
The experts pointed out that Apple’s Lockdown Mode introduced in July does not prevent the exploitation of the Achilles bug.
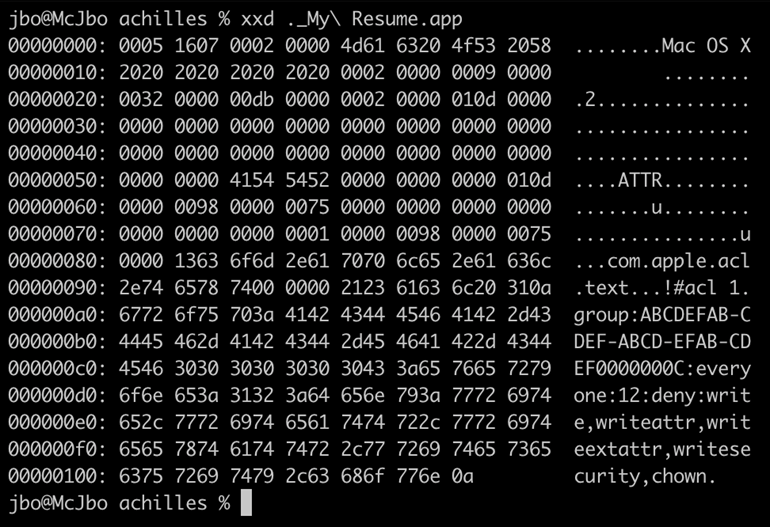
The Achilles vulnerability relies on the Access Control Lists (ACLs) permission model to add extremely restrictive permissions to a downloaded file (i.e., “everyone deny write, writeattr, writeextattr, writesecurity, chown”), to block the Safari browser from setting the quarantine extended attribute.
Below is the POC developed by Microsoft:
- Create a fake directory structure with an arbitrary icon and payload.
- Create an AppleDouble file with the com.apple.acl.text extended attribute key and a value that represents a restrictive ACL (we chose the equivalent of “everyone deny write,writeattr,writeextattr,writesecurity,chown”). Perform the correct AppleDouble patching if using ditto to generate the AppleDouble file.
- Create an archive with the application alongside its AppleDouble file and host it on a web server.
while video POC is available here.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on Patreon using the button below
To keep up to date follow us on the below channels.