Safety – Check Your Installed Dependencies For Known Security Vulnerabilities

Safety checks your installed dependencies for known security vulnerabilities.
By default it uses the open Python vulnerability database Safety DB, but can be upgraded to use pyup.io’s Safety API using the --key option.
Installation
Install safety with pip. Keep in mind that we support only Python 3.5 and up. Look at Python 2.7 section at the end of this document.
pip install safetyUsage
To check your currently selected virtual environment for dependencies with known security vulnerabilites, run:
safety checkYou should get a report similar to this:
+==============================================================================+
| |
| /$$$$$$ /$$ |
| /$$__ $$ | $$ |
| /$$$$$$$ /$$$$$$ | $$ __//$$$$$$ /$$$$$$ /$$ /$$ |
| /$$_____/ |____ $$| $$$$ /$$__ $$|_ $$_/ | $$ | $$ |
| | $$$$$$ /$$$$$$$| $$_/ | $$$$$$$$ | $$ | $$ | $$ |
| ____ $$ /$$__ $$| $$ | $$_____/ | $$ /$$| $$ | $$ |
| /$$$$$$$/| $$$$$$$| $$ | $$$$$$$ | $$$$/| $$$$$$$ |
| |_______/ _______/|__/ _______/ ___/ ____ $$ |
| /$$ | $$ |
| | $$$$$$/ |
| by pyup.io ______/ |
| |
+==============================================================================+
| REPORT |
+==============================================================================+
| No known security vulnerabilities found. |
+==============================================================================+Now, let’s install something insecure:
pip install insecure-packageYeah, you can really install that.
Run safety check again:
+==============================================================================+
| |
| /$$$$$$ /$$ |
| /$$__ $$ | $$ |
| /$$$$$$$ /$$$$$$ | $$ __//$$$$$$ /$$$$$$ /$$ /$$ |
| /$$_____/ |____ $$| $$$$ /$$__ $$|_ $$_/ | $$ | $$ |
| | $$$$$$ /$$$$$$$| $$_/ | $$$$$$$$ | $$ | $$ | $$ |
| ____ $$ /$$__ $$| $$ | $$_____/ | $$ /$$| $$ | $$ |
| /$$$$$$$/| $$$$$$$| $$ | $$$$$$$ | $$$$/| $$$$$$$ |
| |_______/ _______/|__/ _______/ ___/ ____ $$ |
| /$$ | $$ |
| | $$$$$$/ |
| by pyup.io ______/ |
| |
+==============================================================================+
| REPORT |
+==========================+===============+===================+===============+
| package | installed | affected | source |
+==========================+===============+===================+===============+
| insecure-package | 0.1.0 | <0.2.0 | changelog |
+==========================+===============+===================+===============+Examples
Read requirement files
Just like pip, Safety is able to read local requirement files:
safety check -r requirements.txtRead from stdin
Safety is also able to read from stdin with the --stdin flag set.
To check a local requirements file, run:
cat requirements.txt | safety check --stdinor the output of pip freeze:
pip freeze | safety check --stdinor to check a single package:
echo "insecure-package==0.1" | safety check --stdinFor more examples, take a look at the options section.
Using Safety in Docker
Safety can be easily executed as Docker container. It can be used just as described in the examples section.
echo "insecure-package==0.1" | docker run -i --rm pyupio/safety safety check --stdin
cat requirements.txt | docker run -i --rm pyupio/safety safety check --stdinUsing the Safety binaries
The Safety binaries provide some extra security.
After installation, they can be used just like the regular command line version of Safety.
Using Safety with a CI service
Safety works great in your CI pipeline. It returns a non-zero exit status if it finds a vulnerability.
Run it before or after your tests. If Safety finds something, your tests will fail.
Travis
install:
- pip install safety
script:
- safety checkGitlab CI
safety:
script:
- pip install safety
- safety checkTox
[tox]
envlist = py37
[testenv]
deps =
safety
pytest
commands =
safety check
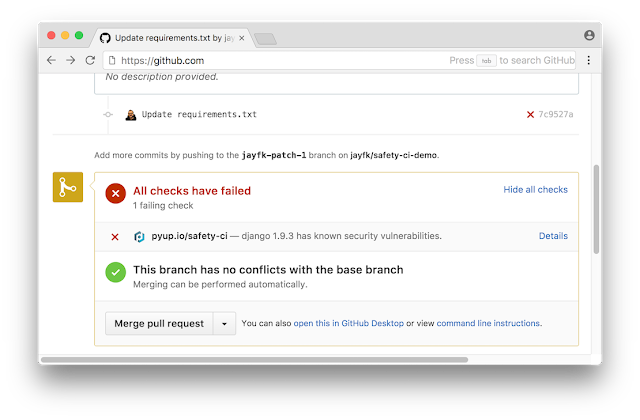
pytestDeep GitHub Integration
If you are looking for a deep integration with your GitHub repositories: Safety is available as a part of pyup.io, called Safety CI. Safety CI checks your commits and pull requests for dependencies with known security vulnerabilities and displays a status on GitHub.
Using Safety in production
Safety is free and open source (MIT Licensed). The underlying open vulnerability database is updated once per month.
To get access to all vulnerabilites as soon as they are added, you need a Safety API key that comes with a paid pyup.io account, starting at $99 for organizations.
Options
--key
API Key for pyup.io’s vulnerability database. Can be set as SAFETY_API_KEY environment variable.
Example
safety check --key=12345-ABCDEFGH--db
Path to a directory with a local vulnerability database including insecure.json and insecure_full.json
Example
safety check --db=/home/safety-db/data--proxy-host
Proxy host IP or DNS
--proxy-port
Proxy port number
--proxy-protocol
Proxy protocol (https or http)
--json
Output vulnerabilities in JSON format.
Example
safety check --json[
[
"django",
"<1.2.2",
"1.2",
"Cross-site scripting (XSS) vulnerability in Django 1.2.x before 1.2.2 allows remote attackers to inject arbitrary web script or HTML via a csrfmiddlewaretoken (aka csrf_token) cookie.",
"25701"
]
]--full-report
Full reports include a security advisory (if available).
Example
safety check --full-report+==============================================================================+
| |
| /$$$$$$ /$$ |
| /$$__ $$ | $$ |
| /$$$$$$$ /$$$$$$ | $$ __//$$$$$$ /$$$$$$ /$$ /$$ |
| /$$_____/ |____ $$| $$$$ /$$__ $$|_ $$_/ | $$ | $$ |
| | $$$$$$ /$$$$$$$| $$_/ | $$$$$$$$ | $$ | $$ | $$ |
| ____ $$ /$$__ $$| $$ | $$_____/ | $$ /$$| $$ | $$ |
| /$$$$$$$/| $$$$$$$| $$ | $$$$$$$ | $$$$/| $$$$$$$ |
| |_______/ _______/|__/ _______/ ___/ ____ $$ |
| /$$ | $$ |
| | $$$$$$/ |
| by pyup.io ______/ |
| |
+==============================================================================+
| REPORT |
+============================+===========+==========================+==========+
| package | installed | affected | ID |
+============================+===========+==========================+==========+
| django | 1.2 | <1.2.2 | 25701 |
+==============================================================================+
| Cross-site scripting (XSS) vulnerability in Django 1.2.x before 1.2.2 allows |
| remote attackers to inject arbitrary web script or HTML via a csrfmiddlewar |
| etoken (aka csrf_token) cookie. |
+==============================================================================+--bare
Output vulnerable packages only. Useful in combination with other tools.
Example
safety check --barecryptography django--cache
Cache requests to the vulnerability database locally for 2 hours.
Example
safety check --cache--stdin
Read input from stdin.
Example
cat requirements.txt | safety check --stdinpip freeze | safety check --stdinecho "insecure-package==0.1" | safety check --stdin--file, -r
Read input from one (or multiple) requirement files.
Example
safety check -r requirements.txtsafety check --file=requirements.txtsafety check -r req_dev.txt -r req_prod.txt--ignore, -i
Ignore one (or multiple) vulnerabilities by ID
Example
safety check -i 1234safety check --ignore=1234safety check -i 1234 -i 4567 -i 89101--output, -o
Save the report to a file
Example
safety check -o insecure_report.txtsafety check --output --json insecure_report.jsonReview
If you save the report in JSON format you can review in the report format again.
Options
--file, -f (REQUIRED)
Read an insecure report.
Example
safety check -f insecure.jsonsafety check --file=insecure.json--full-report
Full reports include a security advisory (if available).
Example
safety review -r insecure.json --full-report+==============================================================================+
| |
| /$$$$$$ /$$ |
| /$$__ $$ | $$ |
| /$$$$$$$ /$$$$$$ | $$ __//$$$$$$ /$$$$$$ /$$ /$$ |
| /$$_____/ |____ $$| $$$$ /$$__ $$|_ $$_/ | $$ | $$ |
| | $$$$$$ /$$$$$$$| $$_/ | $$$$$$$$ | $$ | $$ | $$ |
| ____ $$ /$$__ $$| $$ | $$_____/ | $$ /$$| $$ | $$ |
| /$$$$$$$/| $$$$$$$| $$ | $$$$$$$ | $$$$/| $$$$$$$ |
| |_______/ _______/|__/ _______/ ___/ ____ $$ |
| /$$ | $$ |
| | $$$$$$/ |
| by pyup.io ______/ |
| |
+==============================================================================+
| REPORT |
+============================+===========+==========================+==========+
| package | installed | affected | ID |
+============================+===========+==========================+==========+
| django | 1.2 | <1.2.2 | 25701 |
+==============================================================================+
| Cross-site scripting (XSS) vulnerability in Django 1.2.x before 1.2.2 allows |
| remote attackers to inject arbitrary web script or HTML via a csrfmiddlewar |
| etoken (aka csrf_token) cookie. |
+==============================================================================+--bare
Output vulnerable packages only.
Example
safety review --file report.json --baredjangoPython 2.7
This tool requires latest Python patch versions starting with version 3.5. We did support Python 2.7 in the past but, as for other Python 3.x minor versions, it reached its End-Of-Life and as such we are not able to support it anymore.
We understand you might still have Python 2.7 projects running. At the same time, Safety itself has a commitment to encourage developers to keep their software up-to-date, and it would not make sense for us to work with officially unsupported Python versions, or even those that reached their end of life.
If you still need to run Safety from a Python 2.7 environment, please use version 1.8.7 available at PyPi. Alternatively, you can run Safety from a Python 3 environment to check the requirements file for your Python 2.7 project.
If you like the site, please consider joining the telegram channel or supporting us on Patreon using the button below.




![Cobalt Strike Beacon Detected - 119[.]45[.]29[.]172:8089 7 Cobalt-Strike](https://www.redpacketsecurity.com/wp-content/uploads/2021/11/Cobalt-Strike-300x201.jpg)
