Cisa Warns Of Microsoft Streaming Bug Exploited In Malware Attacks

CISA ordered U.S. Federal Civilian Executive Branch (FCEB) agencies to secure their Windows systems against a high-severity vulnerability in the Microsoft Streaming Service (MSKSSRV.SYS) that’s actively exploited in attacks.
The security flaw (tracked as CVE-2023-29360) is due to an untrusted pointer dereference weakness that enables local attackers to gain SYSTEM privileges in low-complexity attacks that don’t require user interaction.
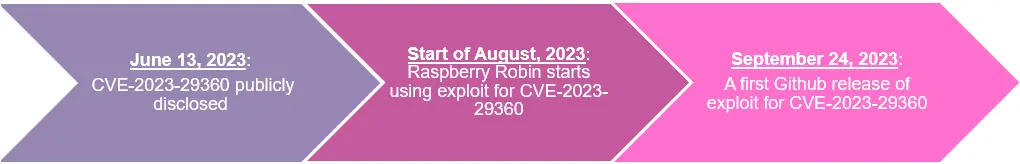
CVE-2023-29360 was found by Synactiv’s Thomas Imbert in the Microsoft Streaming Service Proxy (MSKSSRV.SYS) and reported to Microsoft through Trend Micro’s Zero Day Initiative. Redmond patched the bug during the June 2023 Patch Tuesday, with proof-of-concept exploit code dropping on GitHub three months later, on September 24.
The U.S. cybersecurity agency did not provide details regarding ongoing attacks, but it did confirm that no evidence was found that this vulnerability was used in ransomware attacks.
CISA also added the bug to its Known Exploited Vulnerabilities Catalog this week, warning that such security bugs are “frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise.” As mandated by a binding operational directive (BOD 22-01) issued in November 2021, federal agencies must patch their Windows systems against this security bug within three weeks, by March 21.
Although CISA’s KEV catalog primarily focuses on alerting federal agencies about security flaws that should be addressed as soon as possible, private organizations worldwide are also advised to prioritize patching this vulnerability to block ongoing attacks.
Exploited in malware attacks since August
American-Israeli cybersecurity company Check Point provided more information on this vulnerability last month, saying that Raspberry Robin malware attacks have been exploiting CVE-2023-29360 since August 2023.
“After looking at samples of Raspberry Robin prior to October, we found that it also used an exploit for CVE-2023-29360. This vulnerability was publicly disclosed in June and was used by Raspberry Robin in August,” Check Point said.
“Even though this is a pretty easy vulnerability to exploit, the fact that the exploit writer had a working sample before there was a known exploit in GitHub is impressive as is how quickly Raspberry Robin used it.”
Raspberry Robin is a malware with worm capabilities that surfaced in September 2021 and mainly spreads through USB drives. While its creators are unknown, it has been linked to multiple cybercriminal groups, including EvilCorp and the Clop ransomware gang.
Microsoft said in July 2022 that it spotted the Raspberry Robin malware on the networks of hundreds of organizations from various industry sectors.
Since its discovery, this worm has continuously evolved, adopting new delivery tactics and adding new features, including an evasion where it drops fake payloads to mislead researchers.
