Citrix Bleed exploit lets hackers hijack NetScaler accounts

A proof-of-concept (PoC) exploit is released for the ‘Citrix Bleed’ vulnerability, tracked as CVE-2023-4966, that allows attackers to retrieve authentication session cookies from vulnerable Citrix NetScaler ADC and NetScaler Gateway appliances.
CVE-2023-4966 is a critical-severity remotely exploitable information disclosure flaw Citrix fixed on October 10 without providing many details.
On October 17, Mandiant revealed that the flaw was abused as a zero-day in limited attacks since late August 2023.
This Monday, Citrix issued a subsequent warning to administrators of NetScaler ADC and Gateway appliances, urging them to patch the flaw immediately, as the rate of exploitation has started to pick up.
Today, researchers at Assetnote shared more details about the exploitation method of CVE-2023-4966 and published a PoC exploit on GitHub to demonstrate their findings and help those who want to test for exposure.
The Citrix Bleed flaw
The CVE-2023-4966 Citrix Bleed flaw is an unauthenticated buffer-related vulnerability affecting Citrix NetScaler ADC and NetScaler Gateway, network devices used for load balancing, firewall implementation, traffic management, VPN, and user authentication.
By analyzing the unpatched (13.1-48.47) and patched versions (13.1-49.15) of NetScaler, Assetnote found 50 function changes.
Among these functions, the researchers found two (‘ns_aaa_oauth_send_openid_config’ and ‘ns_aaa_oauthrp_send_openid_config’) that featured additional bounds checks preceding the generation of a response.
These functions use ‘snprintf’ to insert the appropriate data into the generated JSON payload for the OpenID configuration. In the pre-patch version, the response is sent immediately without checks.
The vulnerability emerges from the return value of the snprintf function, which can lead to a buffer over-read if exploited.
The patched version ensures that a response will only be sent if snprintf returns a value lower than 0x20000.
Snatching session tokens
Armed with that knowledge, Assetnote’s analysts attempted to exploit vulnerable NetScaler endpoints.
During that process, they found that the hostname value used for generating the payload comes from the HTTP Host header, so one does not need administrator rights to access it.
Furthermore, the hostname is inserted into the payload six times. Hence, its exploitation makes it possible to exceed the buffer limit, forcing the endpoint to respond with the buffer’s contents and adjacent memory.
“We could clearly see a lot of leaked memory immediately following the JSON payload,” explains Assetnote in the report.
“While a lot of it was null bytes, there was some suspicious-looking information in the response.”
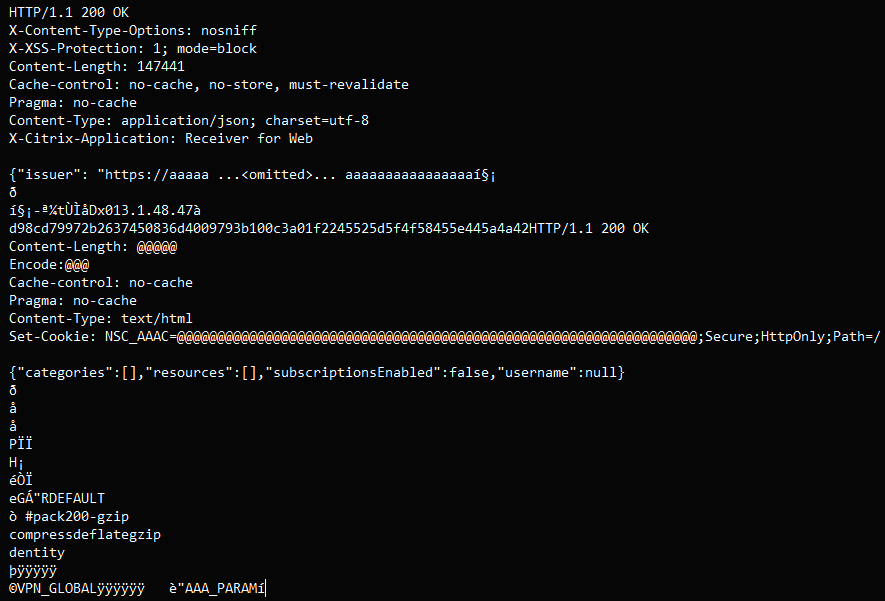
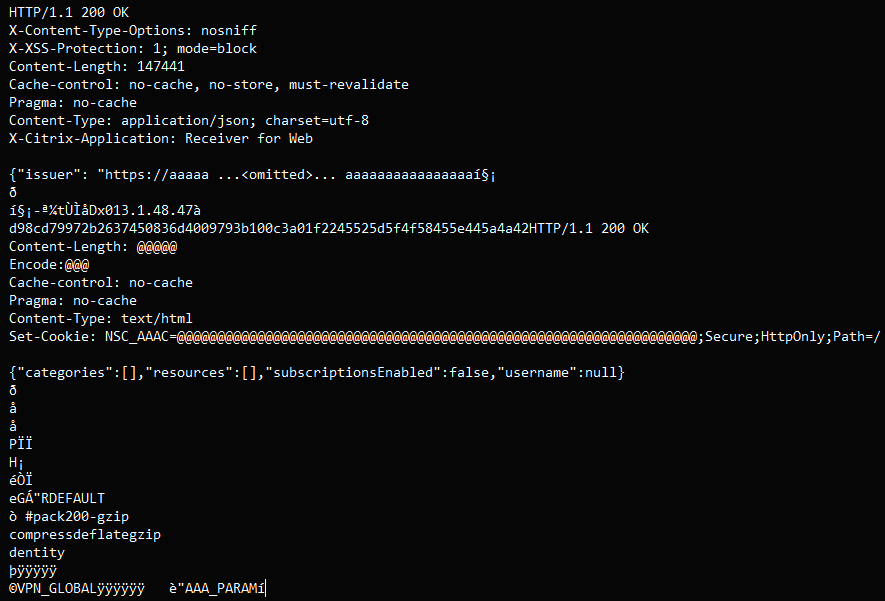
By exploiting the vulnerability thousands of times for testing, the analysts consistently located a 32-65 byte long hex string that is a session cookie.
Retrieving that cookie makes it possible for attackers to hijack accounts and gain unrestricted access to vulnerable appliances.
Now that a CVE-2023-4966 exploit is publicly available, it is expected that threat actors will increase their targeting of Citrix Netscaler devices to gain initial access to corporate networks.
Threat monitoring service Shadowserver reports spikes of exploitation attempts following the publication of Assetnote’s PoC, so the malicious activity has already started.
As these types of vulnerabilities are commonly used for ransomware and data theft attacks, it is strongly advised that system administrators immediately deploy patches to resolve the flaw.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.

![Brute Ratel C4 Detected - 31[.]27[.]187[.]236:9002 4 brute ratel c4](https://www.redpacketsecurity.com/wp-content/uploads/2022/07/brute_ratel_c4-300x300.jpg)

![GoPhish Login Page Detected - 34[.]49[.]82[.]229:443 12 gophish](https://www.redpacketsecurity.com/wp-content/uploads/2024/04/gophish-300x90.png)