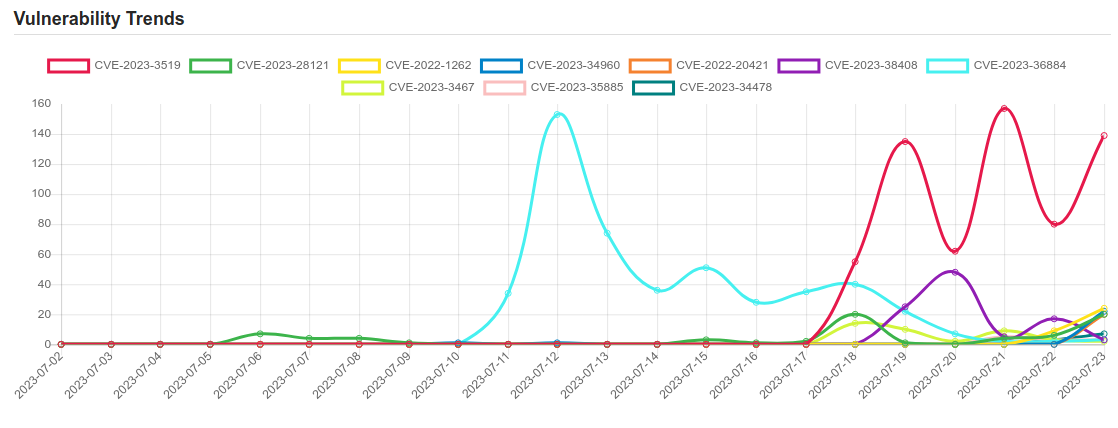
Daily Vulnerability Trends: Mon Jul 24 2023
| CVE NAME | CVE Description |
| CVE-2023-3519 | Unauthenticated remote code execution |
| CVE-2023-34960 | No description provided |
| CVE-2023-38408 | The PKCS#11 feature in ssh-agent in OpenSSH before 9.3p2 has an insufficiently trustworthy search path, leading to remote code execution if an agent is forwarded to an attacker-controlled system. (Code in /usr/lib is not necessarily safe for loading into ssh-agent.) NOTE: this issue exists because of an incomplete fix for CVE-2016-10009. |
| CVE-2023-36884 | Microsoft is investigating reports of a series of remote code execution vulnerabilities impacting Windows and Office products. Microsoft is aware of targeted attacks that attempt to exploit these vulnerabilities by using specially-crafted Microsoft Office documents. An attacker could create a specially crafted Microsoft Office document that enables them to perform remote code execution in the context of the victim. However, an attacker would have to convince the victim to open the malicious file. Upon completion of this investigation, Microsoft will take the appropriate action to help protect our customers. This might include providing a security update through our monthly release process or providing an out-of-cycle security update, depending on customer needs. Please see the Microsoft Threat Intelligence Blog https://aka.ms/Storm-0978 Entry for important information about steps you can take to protect your system from this vulnerability. This CVE will be updated with new information and links to security updates when they become available. |
| CVE-2023-34478 | No description provided |
| CVE-2022-29078 | The ejs (aka Embedded JavaScript templates) package 3.1.6 for Node.js allows server-side template injection in settings[view options][outputFunctionName]. This is parsed as an internal option, and overwrites the outputFunctionName option with an arbitrary OS command (which is executed upon template compilation). |
| CVE-2023-28771 | Improper error message handling in Zyxel ZyWALL/USG series firmware versions 4.60 through 4.73, VPN series firmware versions 4.60 through 5.35, USG FLEX series firmware versions 4.60 through 5.35, and ATP series firmware versions 4.60 through 5.35, which could allow an unauthenticated attacker to execute some OS commands remotely by sending crafted packets to an affected device. |
| CVE-2023-29298 | Adobe ColdFusion versions 2018u16 (and earlier), 2021u6 (and earlier) and 2023.0.0.330468 (and earlier) are affected by an Improper Access Control vulnerability that could result in a Security feature bypass. An attacker could leverage this vulnerability to access the administration CFM and CFC endpoints. Exploitation of this issue does not require user interaction. |
| CVE-2023-38205 | No description provided |
| CVE-2023-23397 | Microsoft Outlook Elevation of Privilege Vulnerability |
| CVE-2023-23536 | The issue was addressed with improved bounds checks. This issue is fixed in macOS Big Sur 11.7.5, iOS 15.7.4 and iPadOS 15.7.4, iOS 16.4 and iPadOS 16.4, macOS Ventura 13.3. An app may be able to execute arbitrary code with kernel privileges |
| CVE-2021-39297 | Potential vulnerabilities have been identified in UEFI firmware (BIOS) for some PC products which may allow escalation of privilege and arbitrary code execution. |
| CVE-2023-32434 | An integer overflow was addressed with improved input validation. This issue is fixed in watchOS 8.8.1, iOS 16.5.1 and iPadOS 16.5.1, iOS 15.7.7 and iPadOS 15.7.7, macOS Big Sur 11.7.8, macOS Monterey 12.6.7, macOS Ventura 13.4.1, watchOS 9.5.2. An app may be able to execute arbitrary code with kernel privileges. Apple is aware of a report that this issue may have been actively exploited against versions of iOS released before iOS 15.7. |
| CVE-2023-3765 | Absolute Path Traversal in GitHub repository mlflow/mlflow prior to 2.5.0. |
| CVE-2023-28121 | An issue in WooCommerce Payments plugin for WordPress (versions 5.6.1 and lower) allows an unauthenticated attacker to send requests on behalf of an elevated user, like administrator. This allows a remote, unauthenticated attacker to gain admin access on a site that has the affected version of the plugin activated. |
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.


