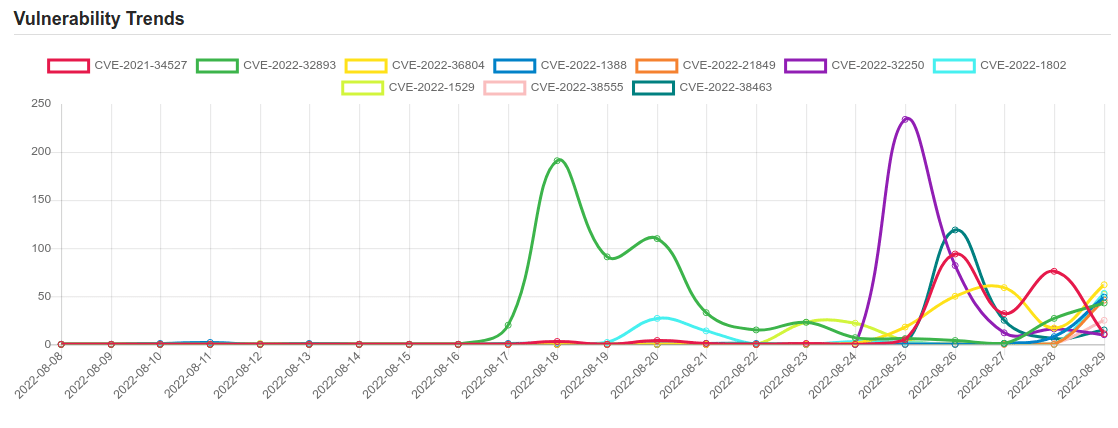
Daily Vulnerability Trends: Tue Aug 30 2022
| CVE NAME | CVE Description |
| CVE-2022-2200 | No description provided |
| CVE-2022-26134 | In affected versions of Confluence Server and Data Center, an OGNL injection vulnerability exists that would allow an unauthenticated attacker to execute arbitrary code on a Confluence Server or Data Center instance. The affected versions are from 1.3.0 before 7.4.17, from 7.13.0 before 7.13.7, from 7.14.0 before 7.14.3, from 7.15.0 before 7.15.2, from 7.16.0 before 7.16.4, from 7.17.0 before 7.17.4, and from 7.18.0 before 7.18.1. |
| CVE-2022-31790 | No description provided |
| CVE-2022-31789 | No description provided |
| CVE-2022-36708 | Library Management System v1.0 was discovered to contain a SQL injection vulnerability via the Id parameter at /student/bookdetails.php. |
| CVE-2021-38406 | Delta Electronic DOPSoft 2 (Version 2.00.07 and prior) lacks proper validation of user-supplied data when parsing specific project files. This could result in multiple out-of-bounds write instances. An attacker could leverage this vulnerability to execute code in the context of the current process. |
| CVE-2022-38557 | D-Link DIR845L v1.00-v1.03 contains a Static Default Credential vulnerability in /etc/init0.d/S80telnetd.sh. |
| CVE-2022-3016 | Use After Free in GitHub repository vim/vim prior to 9.0.0286. |
| CVE-2022-36705 | Ingredients Stock Management System v1.0 was discovered to contain a SQL injection vulnerability via the Id parameter at /stocks/manage_waste.php. |
| CVE-2022-36704 | Library Management System v1.0 was discovered to contain a SQL injection vulnerability via the Id parameter at /librarian/studentdetails.php. |
| CVE-2021-34527 | Windows Print Spooler Remote Code Execution Vulnerability |
| CVE-2022-32893 | An out-of-bounds write issue was addressed with improved bounds checking. This issue is fixed in iOS 15.6.1 and iPadOS 15.6.1, macOS Monterey 12.5.1, Safari 15.6.1. Processing maliciously crafted web content may lead to arbitrary code execution. Apple is aware of a report that this issue may have been actively exploited. |
| CVE-2022-36804 | Multiple API endpoints in Atlassian Bitbucket Server and Data Center 7.0.0 before version 7.6.17, from version 7.7.0 before version 7.17.10, from version 7.18.0 before version 7.21.4, from version 8.0.0 before version 8.0.3, from version 8.1.0 before version 8.1.3, and from version 8.2.0 before version 8.2.2, and from version 8.3.0 before 8.3.1 allows remote attackers with read permissions to a public or private Bitbucket repository to execute arbitrary code by sending a malicious HTTP request. This vulnerability was reported via our Bug Bounty Program by TheGrandPew. |
| CVE-2022-1388 | On F5 BIG-IP 16.1.x versions prior to 16.1.2.2, 15.1.x versions prior to 15.1.5.1, 14.1.x versions prior to 14.1.4.6, 13.1.x versions prior to 13.1.5, and all 12.1.x and 11.6.x versions, undisclosed requests may bypass iControl REST authentication. Note: Software versions which have reached End of Technical Support (EoTS) are not evaluated |
| CVE-2022-21849 | Windows IKE Extension Remote Code Execution Vulnerability. |
| CVE-2022-32250 | net/netfilter/nf_tables_api.c in the Linux kernel through 5.18.1 allows a local user (able to create user/net namespaces) to escalate privileges to root because an incorrect NFT_STATEFUL_EXPR check leads to a use-after-free. |
| CVE-2022-1802 | No description provided |
| CVE-2022-1529 | No description provided |
| CVE-2022-38555 | Linksys E1200 v1.0.04 is vulnerable to Buffer Overflow via ej_get_web_page_name. |
| CVE-2022-38463 | ServiceNow through San Diego Patch 4b and Patch 6 allows reflected XSS in the logout functionality. |
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on Patreon using the button below
To keep up to date follow us on the below channels.