Malware Analysis – evasion – 45246e312449d76f5bb6f09bf5625960
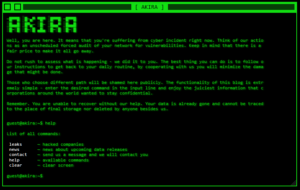
Score: 10 MALWARE FAMILY: evasionTAGS:evasion, persistence, ransomware, spyware, stealer, trojanMD5: 45246e312449d76f5bb6f09bf5625960SHA1: 0fdc80c2c6ccc7af2397b91cefaf4aea89c54c8fANALYSIS DATE: 2023-07-06T17:29:56ZTTPS: T1158, T1112, T1005, T1081, T1012, T1082,...





![[TRYHACKME] - Void Execution Challenge 8 void_execution](https://www.redpacketsecurity.com/wp-content/uploads/2025/09/void_execution-150x150.png)












![[NOVA] - Ransomware Victim: Castilla 42 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)


