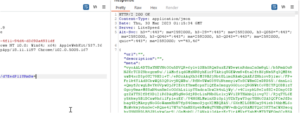
QNAP QTS, QNAP QuTS hero, QNAP QuTScloud, QNAP QVP (QVR Pro appliances), and QNAP QVR command execution | CVE-2023-23355
NAME__________QNAP QTS, QNAP QuTS hero, QNAP QuTScloud, QNAP QVP (QVR Pro appliances), and QNAP QVR command executionPlatforms Affected:Risk Level:6.5Exploitability:UnprovenConsequences:Gain Access...





![[TRYHACKME] - Void Execution Challenge 8 void_execution](https://www.redpacketsecurity.com/wp-content/uploads/2025/09/void_execution-150x150.png)





















![LockBit 3.0 Ransomware Victim: okcu[.]edu 35 image-11](https://www.redpacketsecurity.com/wp-content/uploads/2022/06/image-11-300x142.png)
![[AKIRA] - Ransomware Victim: Palacios Marine & Industrial 42 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)
