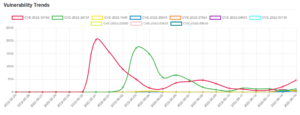
Cisco Secure Email and Web Manager security bypass | CVE-2022-20798
NAME Cisco Secure Email and Web Manager security bypass Platforms Affected:Cisco Email Security ApplianceRisk Level:9.8Exploitability:UnprovenConsequences:Bypass Security DESCRIPTION Cisco Secure Email...



![[PRESENTATION] TruffleHog: The Digital Detective 5 patreon presentation](https://www.redpacketsecurity.com/wp-content/uploads/2025/08/patreon-presentation.png)














![[updated]Unpatched Atlassian Confluence vulnerability is actively exploited 23 Confluence_logo-1-900x506-3](https://www.redpacketsecurity.com/wp-content/uploads/2022/06/Confluence_logo-1-900x506-3-300x169.png)