CISA: Citrix Releases Security Updates for Application Delivery Management
Citrix Releases Security Updates for Application Delivery Management Citrix has released security updates to address vulnerabilities in Application Delivery Management....
Addressing Cyber Risk with a Unified Platform
Hear from guest speaker, Forrester analyst, Allie Mellen, as she shares insights and advice on the factors firms should consider...
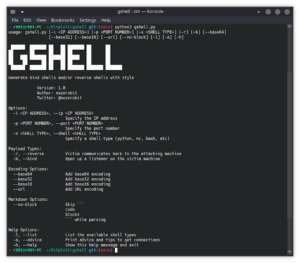
Gshell – A Flexible And Scalable Cross-Plaform Shell Generator Tool
A simple yet flexible cross-platform shell generator tool. Name: G(Great) Shell Description: A cross-platform shell generator tool that lets you...
CISA: Microsoft Releases June 2022 Security Updates
Microsoft Releases June 2022 Security Updates Microsoft has released updates to address multiple vulnerabilities in Microsoft software. An attacker can...


![[TRYHACKME] - Void Execution Challenge 1 void_execution](https://www.redpacketsecurity.com/wp-content/uploads/2025/09/void_execution.png)
![[TRYHACKME] - LondonBridge Full Walkthrough. 2 london-bridge](https://www.redpacketsecurity.com/wp-content/uploads/2025/09/london-bridge.png)



![[TRYHACKME] - Void Execution Challenge 8 void_execution](https://www.redpacketsecurity.com/wp-content/uploads/2025/09/void_execution-150x150.png)









![Cobalt Stike Beacon Detected - 101[.]201[.]65[.]35:9999 18 Cobalt-Strike](https://www.redpacketsecurity.com/wp-content/uploads/2021/11/Cobalt-Strike-300x201.jpg)