Pegasus: The Case of the Infamous Spyware


The case of the infamous spyware Pegasus has taken the world by storm, with news revealing its unlawful use infringing on many people’s basic human rights. With such remote surveillance now accessible via an infected device, the issue of cybersecurity has grown more pressing than ever. According to sources from throughout the world, NSO Group’s software was used to spy on around 50,000 people, including politicians, businessmen, journalists, and activists.
Dmitry Galov, a security researcher at Kaspersky’s GReAT, describes the Pegasus spyware’s beginnings and how it differs from vulnerabilities. “Pegasus is a spyware with versions for both iOS and Android devices,” he explains. Even in 2017, the criminal had the ability to “read the victim’s SMS and emails, listen to calls, take screenshots, record keystrokes, and access contacts and browser history, among other things.” To clarify, Galov argues that Pegasus is a sophisticated and costly malware. It was created with the intent of spying on people of particular interest. As a result, the typical user is unlikely to be a target.
However, the spyware’s sophistication makes it one of the most powerful tools for spying on one’s smartphone. Pegasus has evolved over time to attack a number of zero-day vulnerabilities in Android and iOS. Although it tries to remove its own traces from an infected device, some of them can still be seen under forensic examination. According to Galov, many parties on the darknet can sell and buy malware as well as zero-day vulnerabilities. Vulnerabilities can cost up to $2.5 million – that’s how much the whole chain of Android vulnerabilities was offered for, in 2019.
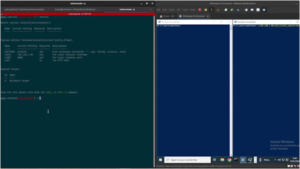
Amnesty International researchers have created a toolkit that can assist consumers to determine whether their phone has been infected with spyware. The open-source toolkit has been made accessible on GitHub by Amnesty International. Users must first download and install a python package from the MVT (Mobile Verification Toolkit) website’s documentation. It also contains advice on how to complete the procedure on both iOS and Android. Users must take a backup of their iOS device before launching MVT.
According to Amnesty International, the goal of MVT is to make it easier to conduct a “consensual forensic study” of devices belonging to people who may be the victims of sophisticated mobile spyware attacks. “We do not want MVT to enable privacy violations of non-consenting individuals,” Amnesty said. “Therefore, the goal of this license is to prohibit the use of MVT (and any other software licensed the same) for the purpose of adversarial forensics.”
If you like the site, please consider joining the telegram channel or supporting us on Patreon using the button below.



![Black Basta Ransomware Victim: thelawrencegroup[.]com_privat 10 Basta](https://www.redpacketsecurity.com/wp-content/uploads/2022/06/Basta-300x97.png)