Problems I have found with Kippo Honeypot
Kippo! Great honeypot…..
But there are problems, i mean 2 seconds with metasploit and BAM! honeypot detected!
Then there are other ways to detect it, once logged in. Its a dead giveaway.
So i have been reading up about other ways to detect kippo, in an aim to make kippo better. So far here are my findings.
I came across a blog which wrote about how telnetting to a Kippo instance and sending a few carriage returns will cause Kippo to throw an error. From what i have read OpenSSH does throw a different error.
Having found the following on another blog I thought I would look into it.
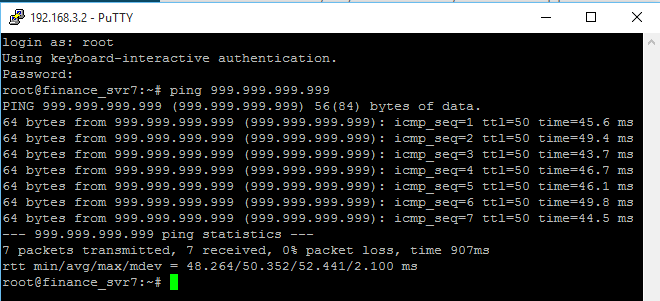
The following is a quick proof-of-concept using Fabrizio’s method:
OpenSSH
$ printf "\n\n\n\n\n\n\n\n" | nc -w3 2.2.2.2 22 SSH-2.0-OpenSSH_6.6.1p1 Ubuntu-2ubuntu2 Protocol mismatch. $
Kippo
$ printf "\n\n\n\n\n\n\n\n" | nc -w3 1.1.1.1 22 SSH-2.0-OpenSSH_5.5p1 Debian-4ubuntu5 bad packet length 168430090 $
As you can see they are different
OpenSSH throws a error as soon as it receives a carriage return, whereas Kippo responds slightly differently. I understand there has been a fix in place for this since reading about that.
The patched the code to mimic OpenSSH and return the same error.
$ printf "\n\n\n\n\n\n\n\n" | nc -w3 127.0.0.1 22 SSH-2.0-OpenSSH_5.1p1 Debian-5 Protocol mismatch
So far , looks like we have more to learn… anyone with suggestions about making kippo harder to detect would be welcomed.
The other issues I have found with Kippo, is the longer it is running the longer people / attackers stay away from it.
I heave read that replacing the pickle.fs file now and then helps with this but not for long.
Having this in mind, make me think about what other honeypots are there that dont get the same issues ?
Many others have also done research in this field, and I give nods to them 🙂