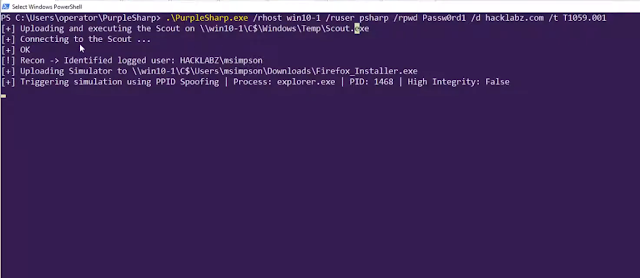
PurpleSharp – C# Adversary Simulation Tool That Executes Adversary Techniques With The Purpose Of Generating Attack Telemetry In Monitored Windows Environments
Defending enterprise networks against attackers continues to present a difficult challenge for blue teams. Prevention has fallen short; improving detection & response capabilities has proven to be a step in the right direction. However, without the telemetry produced by adversary behavior, building new and testing existing detection capabilities will be constrained.
PurpleSharp is an open source adversary simulation tool written in C# that executes adversary techniques within Windows Active Directory environments. The resulting telemetry can be leveraged to measure and improve the efficacy of a detection engineering program. PurpleSharp leverages the MITRE ATT&CK Framework and executes different techniques across the attack life cycle: execution, persistence, privilege escalation, credential access, lateral movement, etc. It currently supports 37 unique ATT&CK techniques.
PurpleSharp was first presented at Derbycon IX on September 2019.
An updated version was released on August 6th 2020 as part of BlackHat Arsenal 2020. If you want to jump straight to the demos:
Demo 1
Demo 2
Goals / Use Cases
The attack telemetry produced by simulating techniques with PurpleSharp aids detection teams in:
- Building new detecttion analytics
- Testing existing detection analytics
- Validating detection resiliency
- Identifying gaps in visibility
- Identifing issues with event logging pipeline
Quick Start Guide
PurpleSharp can be built with Visual Studio Community 2019 or 2020.
Documentation
https://purplesharp.readthedocs.io/
Authors
- Mauricio Velazco – @mvelazco
Acknowledgments
The community is a great source of ideas and feedback. Thank you all.
- Olaf Hartong
- Roberto Rodriguez
- Matt Graeber
- Jonny Johnson
- Keith McCammon
- Andrew Schwartz
If you like the site, please consider joining the telegram channel or supporting us on Patreon using the button below.