Screenconnect Critical Bug Now Under Attack As Exploit Code Emerges

Both technical details and proof-of-concept exploits are available for the two vulnerabilities ConnectWise disclosed earlier this week for ScreenConnect, its remote desktop and access software.
A day after the vendor published the security issues, attackers started leveraging them in attacks.
CISA has assigned CVE-2024-1708 and CVE-2024-1709 identifiers to the the two security issues, which the vendor assessed as a maximum severity authentication bypass and a high-severity path traversal flaw that impact ScreenConnect servers 23.9.7 and earlier.
ConnectWise urged admins to update on-premise servers to version 23.9.8 immediately to mitigate the risk and clarified that those with instances on screenconnect.com cloud or hostedrmm.com have been secured.
Threat actors have compromised multiple ScreenConnect accounts, as confirmed by the company in an update to its advisory, based on incident response investigations.
Cybersecurity company Huntress has analyzed the vulnerabilities and is warning that developing an exploit is a trivial task.
The company also stated that on Monday the Censys platform was showing more than 8,800 vulnerable ScreenConnect servers exposed. An assessment from The ShadowServer Foundation noted that yesterday the number was around 3,800.
The first working exploits emerged quickly after ConnectWise announced the two vulnerabilities and more continue to be published. This prompted Huntress to share its detailed analysis and show how easy it is to create an exploit, in the hope that companies would move faster with remediation steps.
Easy to spot and exploit
Huntress located the two flaws by looking at the code changes the vendor introduced with the patch.
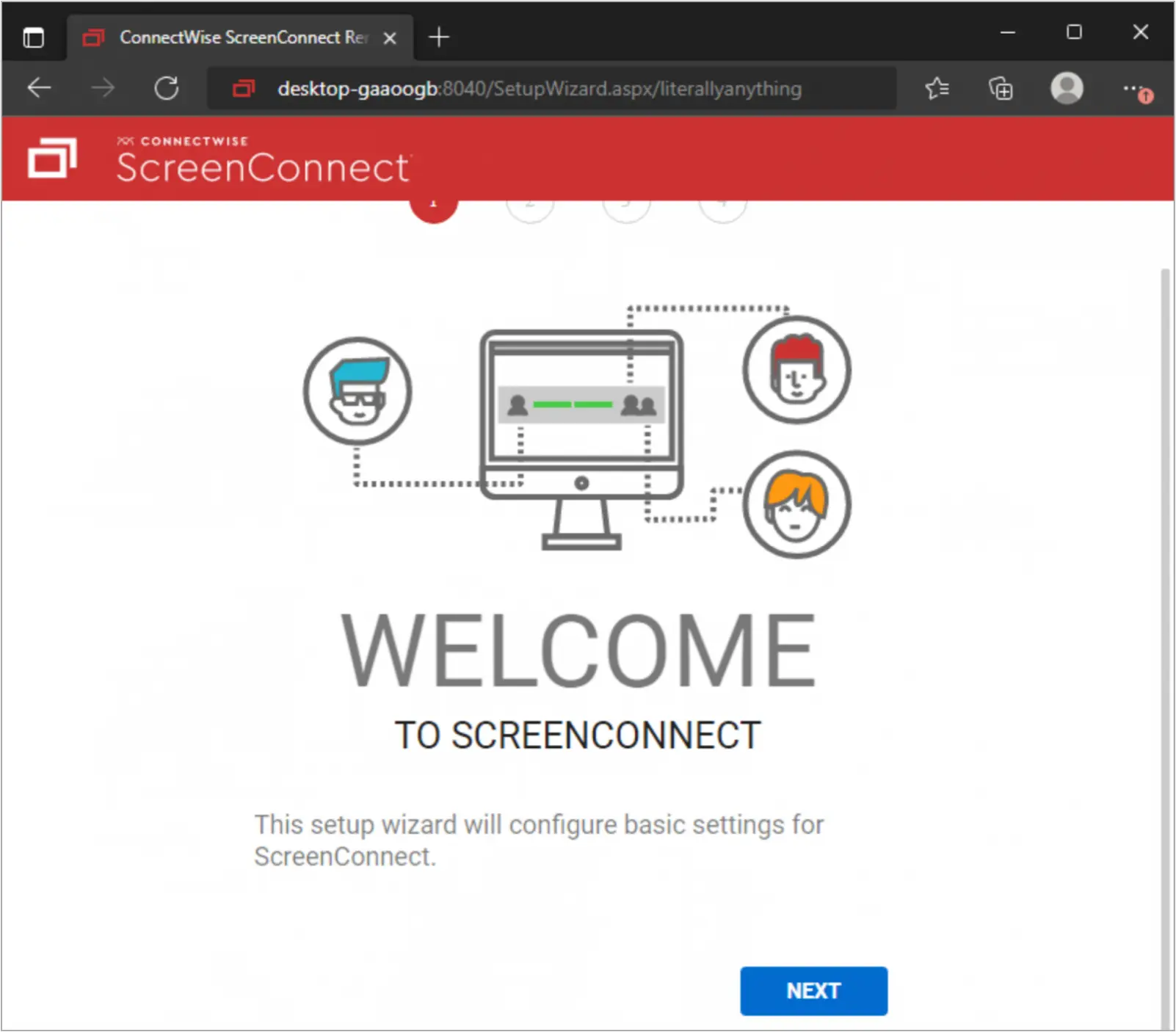
For the first flaw, they found a new check in a text file indicating that authentication process wasn’t secured against all access paths, including the setup wizard (‘SetupWizard.aspx’).
This pointed to the possibility that in the vulnerable versions a specially crafted request could let users use the setup wizard even when ScreenConnect had already been set up.
Because the setup wizard allowed it, a user could create a new administrator account and use it to take control of the ScreenConnect instance.
Leveraging the path traversal bug is possible with the help of another specially crafted request that allows accessing or modifying files outside the intended restricted directory.
The flaw was located by noticing code changes on the ‘ScreenConnect.Core.dll’ file, pointing to ZipSlip, a vulnerability that occurs when applications don’t properly sanitize the file extraction path, which could result in overwriting sensitive files.
The updates from ConnectWise introduce stricter path validation when extracting ZIP file contents, specifically to prevent file writing outside designated subdirectories within ScreenConnect’s folder.
With administrative access from the previous exploit, it is possible to access or manipulate the User.xml file and other sensitive files by crafting requests that include directory traversal sequences to navigate the file system beyond the intended limits.
Eventually, the attacker can upload a payload, such as a malicious script or executable, outside the ScreenConnect subdirectory.
Huntress shared indicators of compromise (IoCs) and analytical detection guidance based on the artifacts created when the above flaws are exploited.
Admins who haven’t applied the security updates are strongly recommended to use the detections to check for unauthorized access.
