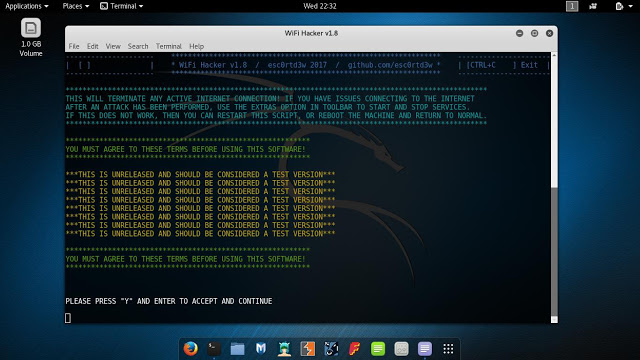
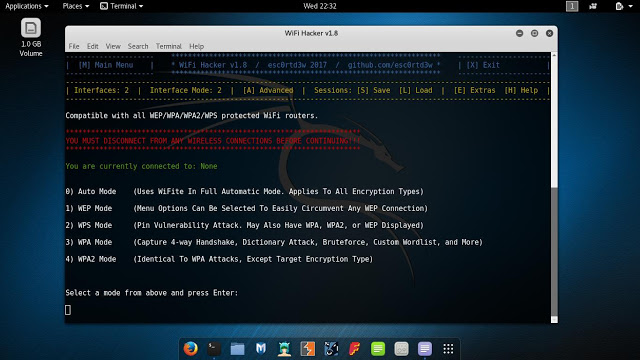
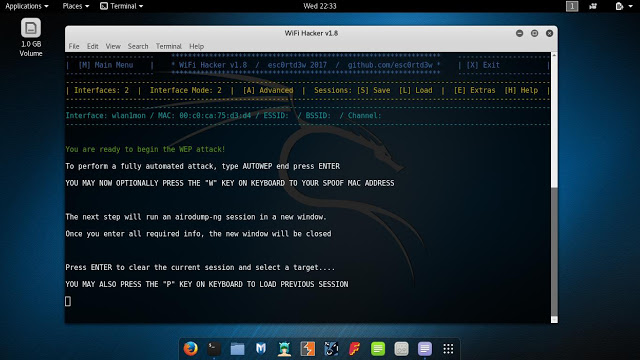
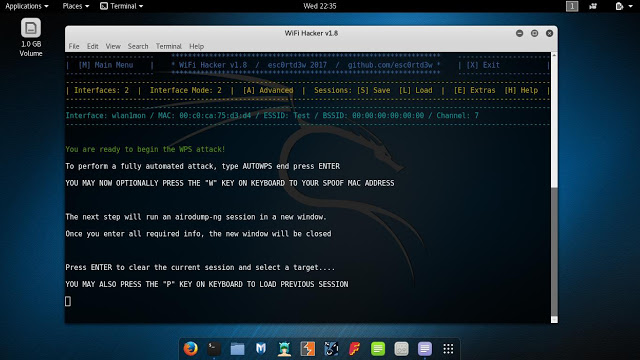
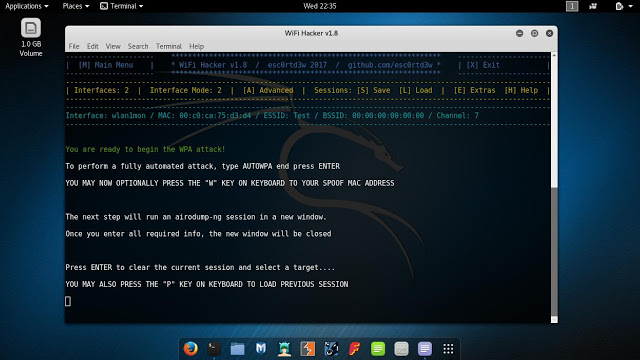
Wifi-Hacker – Shell Script For Attacking Wireless Connections Using Built-In Kali Tools
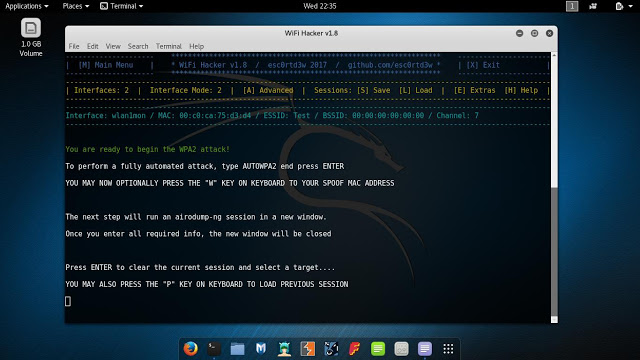
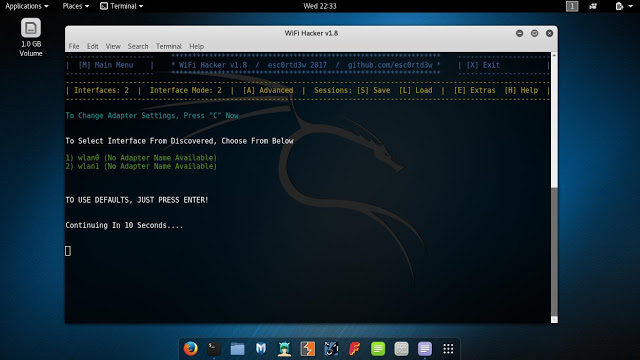
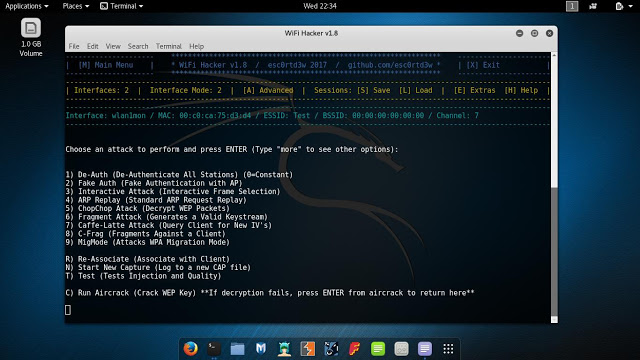
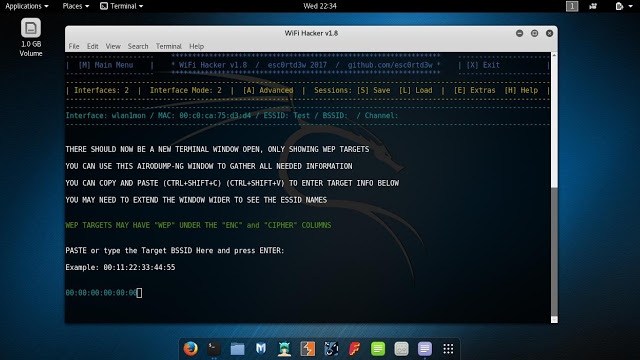
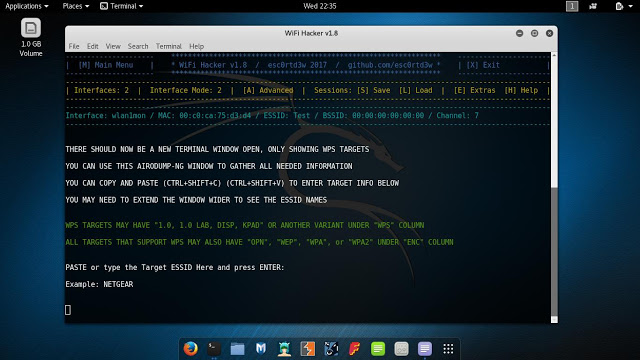
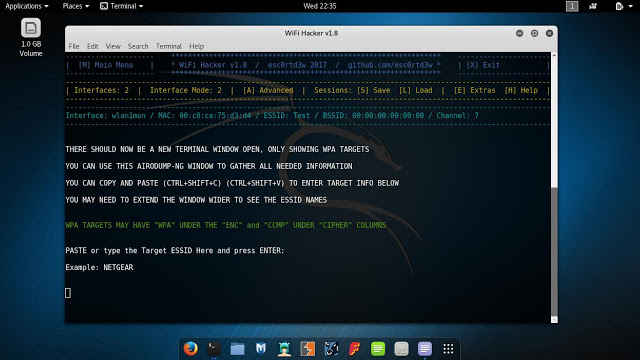
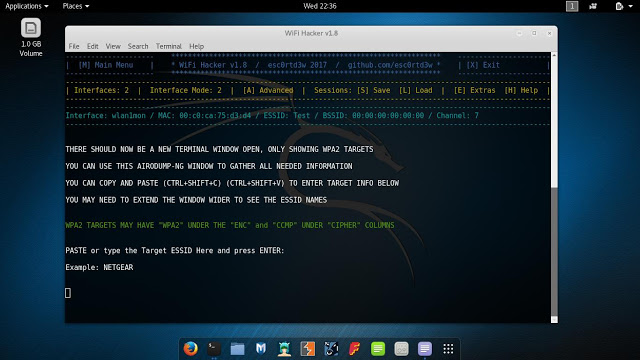
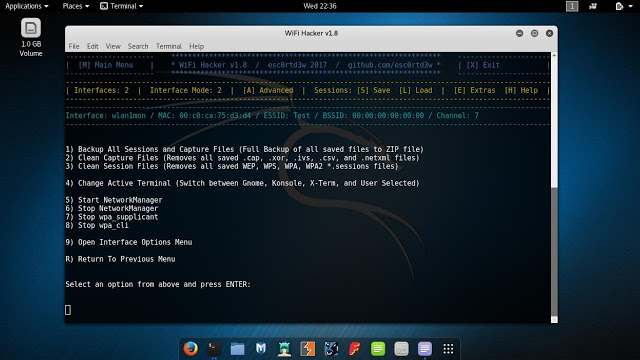
Shell Script For Attacking Wireless Connections Using Built-In Kali Tools. Supports All Securities (WEP, WPS, WPA, WPA2)
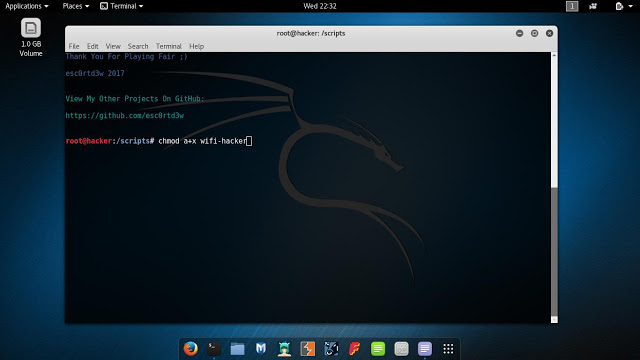














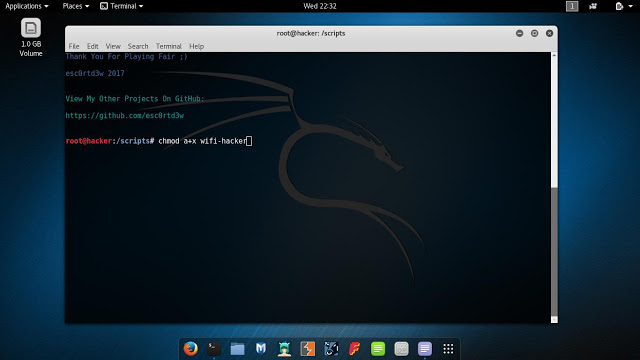
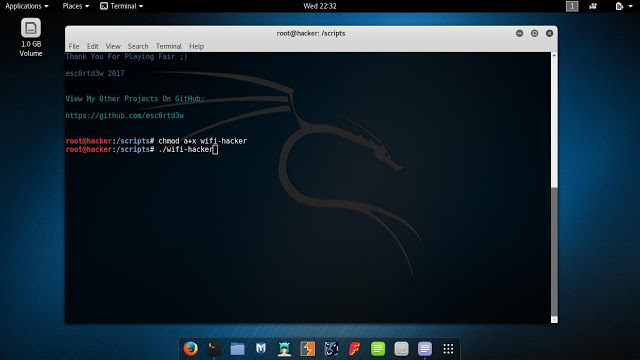
Download Wifi-Hacker

![[HANDALA] - Ransomware Victim: Commemoration of Commander Martyr Reza Awada 16 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)
![Cobalt Strike Beacon Detected - 20[.]74[.]209[.]192:8081 20 Cobalt-Strike](https://www.redpacketsecurity.com/wp-content/uploads/2021/11/Cobalt-Strike-300x201.jpg)
