23andMe hit with lawsuits after hacker leaks stolen genetics data

Genetic testing provider 23andMe faces multiple class action lawsuits in the U.S. following a large-scale data breach that is believed to have impacted millions of its customers.
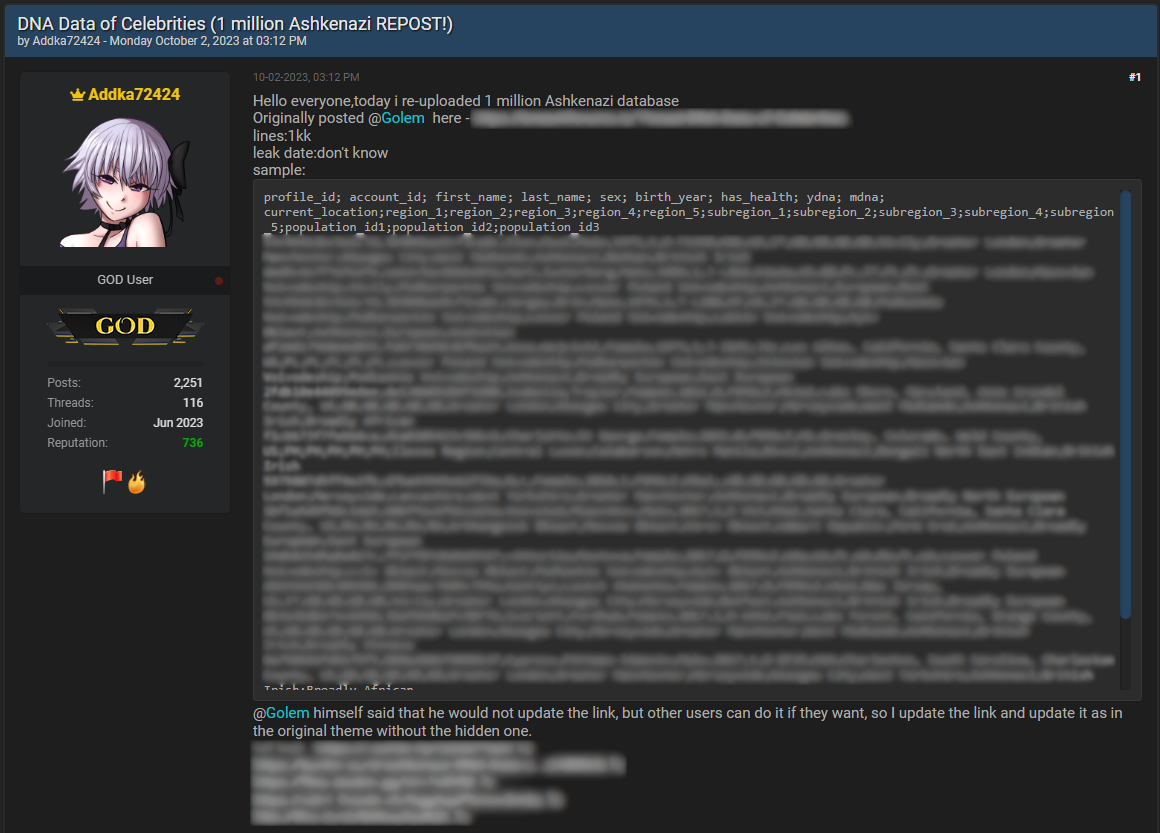
Late last month, a threat actor leaked 23andMe customer data in a CSV file named ‘Ashkenazi DNA Data of Celebrities.csv’ on hacker forums.
The file allegedly contained the data of nearly 1 million Ashkenazi Jews who used 23andMe services to find their ancestry info, genetic predispositions, and more.
Source: BleepingComputer
The data in the CSV file contained information on 23andMe users’ account IDs, full names, sex, date of birth, DNA profiles, location, and region details.
Last week, the original hacker decided to retract the post and instead began selling data profiles of stolen 23andMe data. However, other threat actors continued to share the original 23andMe leak throughout cybercrime communities and forums.
In response to an inquiry, 23andMe told BleepingComputer that the hackers accessed its platform through credential-stuffing attacks on weakly secured accounts. However, they refuted claims of a direct security breach of their systems.
A 23andMe spokesperson explained that the attackers initially gained unauthorized access to a small number of accounts but eventually exfiltrated the data of a larger yet undefined number of clients due to them activating an optional feature named ‘DNA Relatives,’ which connects genetic relatives.
After the publication of our report, 23andMe posted an announcement on its site promising to inform impacted customers individually and keep them updated about the results of the ongoing investigation carried out with the help of third-party experts and law enforcement authorities.
Numerous lawsuits filed
Although platform members voluntarily activated the opt-in feature, not all of them accept that the involved risk of internal data-sharing should exempt the firm from its responsibility to place protection layers.
In this case, many people following proper security practices by enabling 2FA on their accounts and using a strong and unique password still found themselves exposed, and their sensitive data leaked on cybercrime forums.
At least four class action complaints have been submitted in California (Santana, Eden, Andrizzi, Lamons) seeking relief for the damage done by 23andMe’s failure to protect their data.
The lawsuits highlight a lack of information in the company’s official announcement regarding the security event, the current status of customer data safety, the network breach’s duration, and the cyberattack’s exact mechanism.
Also, they criticize 23andMe for failing to implement adequate security measures that would help monitor its network for abnormal activity and potentially take action to stop the intrusion much sooner.
The legal actions emphasize that 23andMe, a company managing sensitive medical data, should have been well aware of the elevated cybersecurity threats given the numerous high-profile breaches in the industry, underscoring the high value of such data.
The plaintiffs ask for various financial reliefs against 23andMe, including restitution, lifetime credit monitoring, actual, compensatory, and statutory damages and penalties, punitive damages, and coverage of attorney’s fees.
One of the complaints defines the nominal damages to $1,000 and punitive damages to $3,000 per class action lawsuit member, in addition to various other relief requests.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.


