Andriller – Software Utility With A Collection Of Forensic Tools For Smartphones
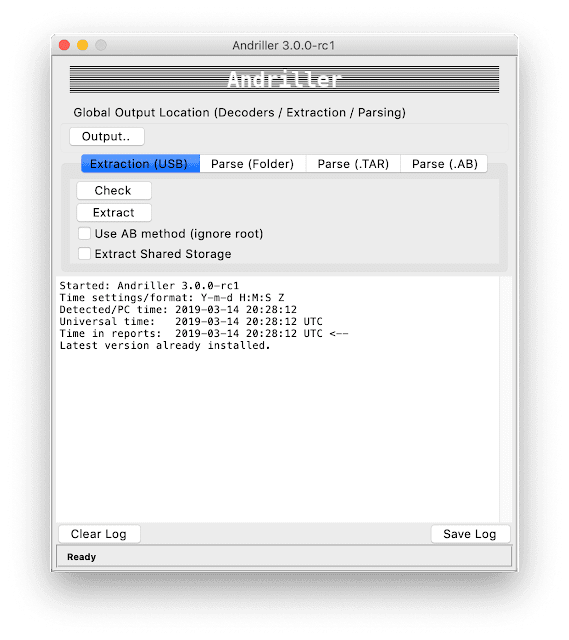
Andriller – is software utility with a collection of forensic tools for smartphones. It performs read-only, forensically sound, non-destructive acquisition from Android devices. It has features, such as powerful Lockscreen cracking for Pattern, PIN code, or Password; custom decoders for Apps data from Android (some Apple iOS & Windows) databases for decoding communications. Extraction and decoders produce reports in HTML and Excel formats.
Features
- Automated data extraction and decoding
- Data extraction of non-rooted without devices by Android Backup (Android versions 4.x, varied/limited support)
- Data extraction with root permissions: root ADB daemon, CWM recovery mode, or SU binary (Superuser/SuperSU)
- Data parsing and decoding for Folder structure, Tarball files (from nanddroid backups), and Android Backup (backup.ab files)
- Selection of individual database decoders for Android apps
- Decryption of encrypted WhatsApp archived databases (.crypt to .crypt12, must have the right key file)
- Lockscreen cracking for Pattern, PIN, Password (not gatekeeper)
- Unpacking the Android backup files
- Screen capture of a device’s display screen
Python Requirements
- 3.6+ (64-bit version recommended)
It is highly advised to setup a virtual environment to install Andriller and its dependencies in it. However, it is not essential, and the global environment can also be used. Depending on how Python was setup, it may be needed to substitute
pythonandpiptopython3andpip3retrospectively for the instructions below.
Windows only: when installing Python from https://www.python.org, make sure Add Python to PATH is ticked.
System Dependencies
adbpython3-tk
[Ubuntu/Debian] Install from Terminal:
$ sudo apt-get install android-tools-adb python3-tk[Mac] Install from brew cask:
$ brew cask install android-platform-tools[Windows] : Included.
Installation (from PYPI, recommended)
$ pip install andriller -UInstallation (from source, editable)
$ pip install -e .Quick Start (run GUI)
$ python -m andriller
![[QILIN] - Ransomware Victim: vresystems[.]com 2 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)

