Angrgdb – Use Angr Inside GDB – Create An Angr State From The Current Debugger State
Use angr inside GDB. Create an angr state from the current debugger state.
Install
pip install angrgdb
echo "python import angrgdb.commands" >> ~/.gdbinitUsage
angrgdb implements the angrdbg API in GDB.
You can use it in scripts like this:
from angrgdb import *
gdb.execute("b *0x004005f9")
gdb.execute("r aaaaaaaa")
sm = StateManager()
sm.sim(sm["rax"], 100)
m = sm.simulation_manager()
m.explore(find=0x00400607, avoid=0x00400613)
sm.to_dbg(m.found[0]) #write input to GDB
gdb.execute("x/s $rax")
#0x7fffffffe768: "ais3{I_tak3_g00d_n0t3s}"
gdb.execute("c")
#Correct! that is the secret key!You can also use angrgdb commands directly in GDB for simple stuffs:
angrgdb sim <register name> [size]Symbolize a registerangrgdb sim <address> [size]Symbolize a memory areaangrgdb listList all items that you setted as symbolicangrgdb find <address0> <address1> ... <addressN>Set the list of find targetsangrgdb avoid <address0> <address1> ... <addressN>Set the list of avoid targetsangrgdb resetReset the context (symbolic values and targets)angrgdb runGenerate a state from the debugger state and run the explorationangrgdb shellOpen an shell with a StateManager instance created from the current GDB stateangrgdb interactiveGenerate a state from the debugger state and explore by hand using a modified version of angr-cli
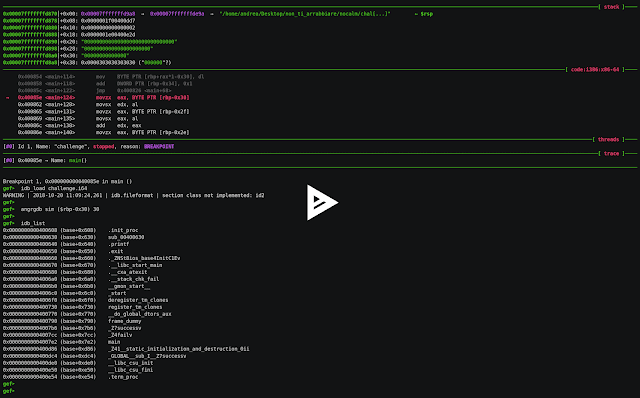
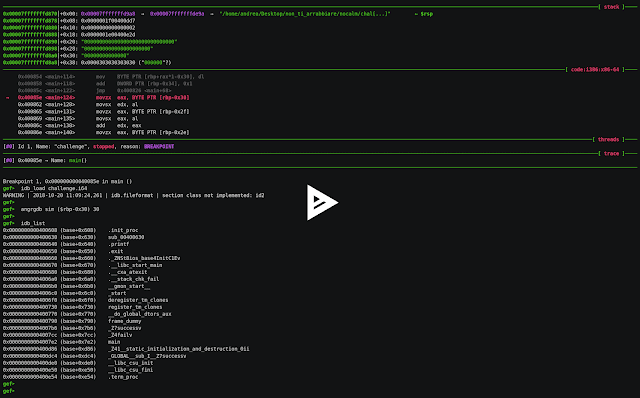
An example crackme solve using angrgdb+GEF+idb2gdb:
Loading scripts in GDB
This is a tip if you don’t want to use angrgdb from the cli but you want to use a python script. To load a script in GDB use source script.py.
TODO
- add remote angrdbg like in IDAngr
Download Angrgdb


