CASPER attack steals data using air-gapped computer’s internal speaker
Researchers at the School of Cyber Security at Korea University, Seoul, have presented a new covert channel attack named CASPER can leak data from air-gapped computers to a nearby smartphone at a rate of 20bits/sec.
The CASPER attack leverages the internal speakers inside the target computer as the data transmission channel to transmit high-frequency audio that the human ear cannot hear and convey binary or Morse code to a microphone up to 1.5m away.
The receiving microphone can be in a smartphone recording sound inside the attacker’s pocket or a laptop in the same room.
Researchers have previously developed similar attacks leveraging external speakers. However, air-gapped, network-isolated systems used in critical environments, such as government networks, energy infrastructure, and weapon control systems, are unlikely to have external speakers.
On the other hand, internal speakers that provide audio feedback, such as boot-up beeps, are still considered necessary, so they’re commonly present, making them better candidates.
Infecting the target
As is the case with almost all secret channel attacks targeting network-isolated computers, a rogue employee or a stealthy intruder with physical access to the target must first infect it with malware.
Although this scenario may seem impractical or even far-fetched, there have been multiple instances of such attacks being successfully carried out in the past, with notable examples including the Stuxnet worm, which targeted Iran’s uranium enrichment facility at Natanz, the Agent.BTZ malware that infected a U.S. military base, and the Remsec modular backdoor, which secretly collected information from air-gapped government networks for over five years.
The malware can autonomously enumerate the target’s filesystem, locate files or file types that match a hardcoded list and attempt to exfiltrate them.
More realistically, it can perform keylogging, which is more suitable for such a slow data transmission rate.
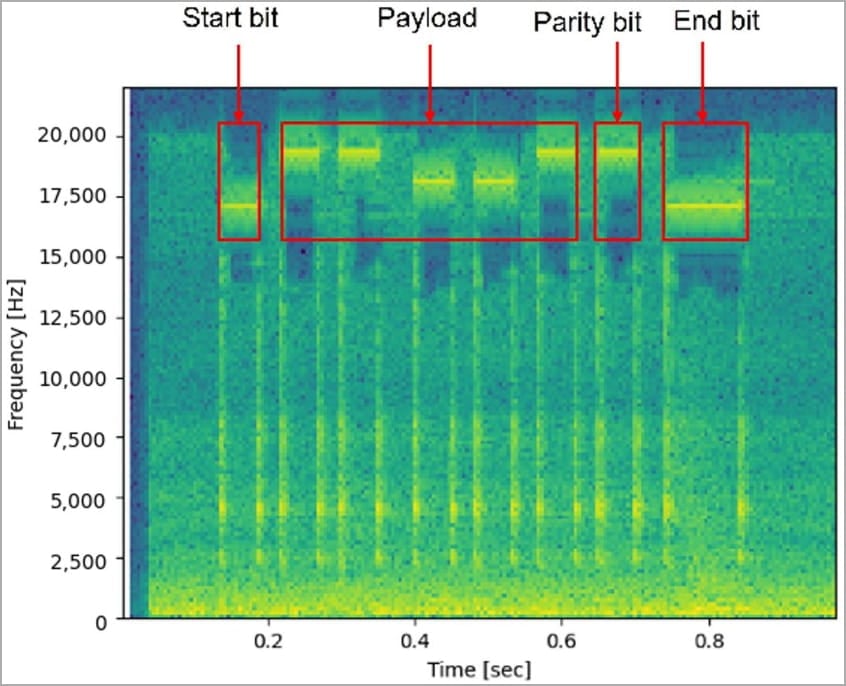
The malware will encode the data to be exfiltrated from the target in binary or Morse code and transmit it through the internal speaker using frequency modulation, achieving an imperceptible ultrasound in a range between 17 kHz and 20 kHz.

The results
The researchers experimented with the described model using a Linux-based (Ubuntu 20.04) computer as the target, and a Samsung Galaxy Z Flip 3 as the receiver, running a basic recorder application with a sampling frequency of up to 20 kHz.
In the Morse code experiment, the researchers set the length per bit to 100 ms and used 18 kHz for dots and 19 kHz for the dash. The smartphone was located 50cm away and was able to decode the sent word “covert.”
In the binary data experiment, the length per bit was set to 50 ms, transferring zeros at a frequency of 18 kHz and 1s at 19 kHz. A 50 ms start/end bit was also used at 17 kHz to indicate the beginning of a new message.
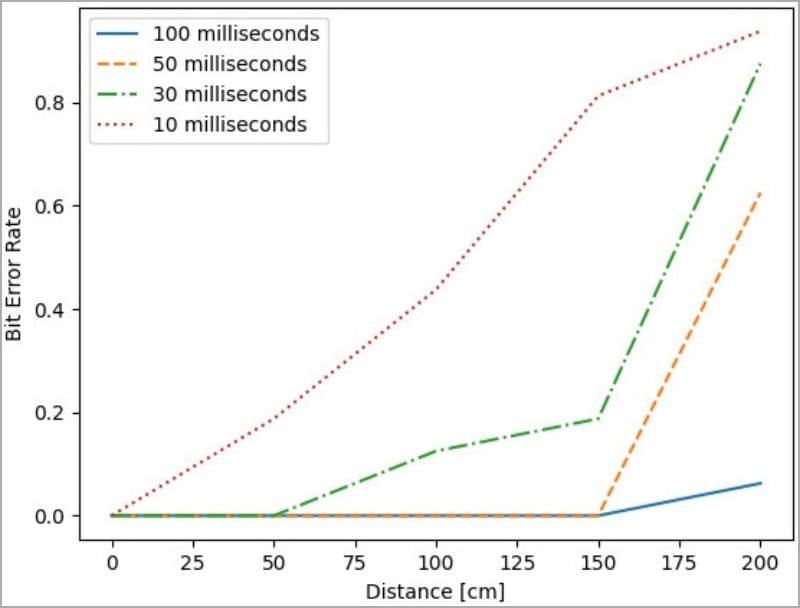
Based on the conducted tests, the maximum distance of the receiver is 1.5 meters (4.9 ft), using a length per bit of 100 ms.
The overall results of the experiment, however, show that the length per bit affects the bit error rate, and a maximum reliable transmitting bit rate of 20 bits/s is achievable when the length per bit is 50 ms.
At this data transfer rate, the malware could transmit a typical 8-character length password in about 3 seconds and a 2048-bit RSA key in 100 seconds.
Anything above that, like a small 10 KB file, for example, would need over an hour to exfiltrate from the air-gapped system, even if the conditions are ideal and no interruptions occur during the transmission.
A solution to the slow data rate would be to vary the frequency band for multiple simultaneous transmissions; however, internal speakers can only produce sound in a single frequency band, so the attack is practically limited.
The researchers shared ways to defend against the CASPER attack, with the simplest being to remove the internal speaker from mission-critical computers.
If that’s impossible, defenders could implement a high-pass filter to keep all generated frequencies within the audible sound spectrum, blocking ultrasound transmissions.
If you’re interested in other covert channel attacks against air-gapped systems, check out COVID-bit, which uses the PSU to generate electromagnetic waves that carry data.
Other examples of similar attacks are ETHERLED, which relies on the LED lights of the target’s network card to transmit Morse code signals, and one named SATAn, which uses SATA cables as wireless antennas.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below


To keep up to date follow us on the below channels.







