China-linked cyberspies backdoor semiconductor firms with Cobalt Strike
Hackers engaging in cyber espionage have targeted Chinese-speaking semiconductor companies with TSMC-themed lures that infect them with Cobalt Strike beacons.
Taiwan Semiconductor Manufacturing Company (TSMC) is the world’s largest semiconductor contract manufacturing and design firm, with an annual revenue of $73.5 billion and over 73,000 employees worldwide.
The campaign spotted by EclecticIQ focuses on firms based in Taiwan, Hong Kong, and Singapore, with the observed TTPs (tactics, techniques, and procedures) bearing similarities to previous activities linked to Chinese state-backed threat groups.
Deploying Cobalt Strike
Eclectic’s report does not specify the initial compromise channel, but it is presumed to be spear-phishing emails, a typical approach used in cyber espionage operations.
In this campaign, the threat actors distribute the HyperBro loader to install a Cobalt Strike beacon on the compromised device, providing remote access to the threat actors.
When HyperBro is launched, it will also display a PDF pretending to be from TSMC to divert attention, achieve a stealthier compromise, and avoid raising suspicions.
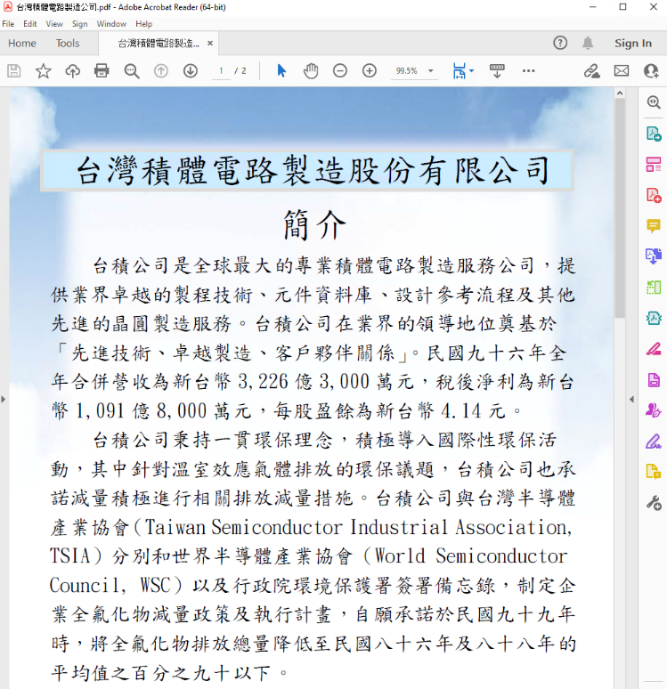
The loader uses DLL side-loading to launch a Cobalt Strike beacon in memory, leveraging a digitally signed binary from CyberArk’s vfhost.exe.
A file named ‘bin.config’ that contains XOR encrypted Cobalt Strike shellcode is decrypted and loaded into the legitimate ‘vfhost.exe’ process, evading AV detection.
The command and control (C2) server address hardcoded into the Cobalt Strike implant used in this attack is disguised as a legitimate jQuery CDN, allowing it to bypass firewall defenses.
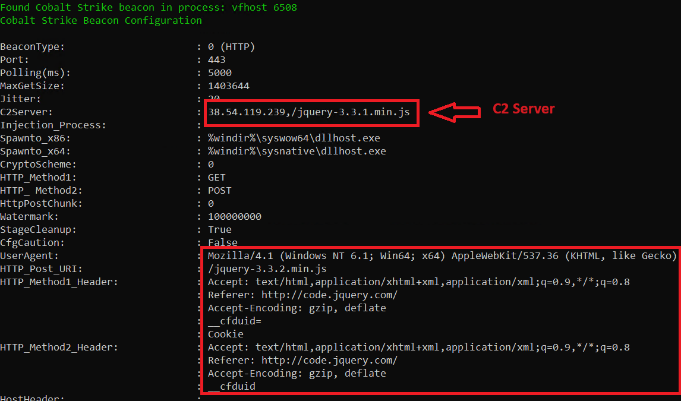
On a second variant of the attack, the hackers use a compromised Cobra DocGuard web server to drop an additional McAfee binary (‘mcods.exe’) and load more Cobalt Strike shellcode using DLL side-loading again via ‘mcvsocfg.dll.’
In this case, the hackers deployed a previously undocumented Go-based backdoor named ‘ChargeWeapon,’ designed to gather and transmit host data to the C2 in base64-encoded form.
ChargeWeapon employs simple malware evasion methods provided through the “garble” open-source tool, while its capabilities include the following:
- Communicate with a remote device using the default Windows command line interface
- Execute commands through Windows Management Instrumentation (WMI)
- Utilize TCP over HTTP for its C2 communications
- Use base64 encoding to obfuscate data during C2 connection
- Reads and writes files on the infected host
Attributed to China
Eclectic says the observed TTPs show extensive similarities with Chinese threat group’s operations, like RedHotel and APT27 (aka Budworm, LuckyMouse).
“EclecticIQ analysts assess with high confidence that the analyzed Hyperbro Loader, the malware downloader and the GO backdoor are very likely operated and developed by a PRC backed nation-state threat actor, due to victimology, infrastructure observed, malware code and resemblance with previously reported activity clusters,” explains EclecticIQ.
Symantec and ESET have both previously reported about China-sponsored APTs leveraging Cobra DocGuard servers for malware delivery, further strengthening the attribution hypothesis to Chinese hackers.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.

![[INCRANSOM] - Ransomware Victim: C B King Memorial School(branch) 5 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)



