CyberNews researchers reported that Ecco a global shoe manufacturer and retailer exposed millions of documents
CyberNews researchers reported that Ecco, a global shoe manufacturer and retailer, exposed millions of documents.
Original post @ https://cybernews.com/security/ecco-leaks-sensitive-data-for-months/
Ecco, a global shoe manufacturer and retailer, exposed millions of documents. Not only could anyone have modified the data, but the server misconfiguration’s severity likely left the company open to an attack that could have affected customers all over the world.
It’s no use carrying an umbrella if your shoes are leaking, an old Irish proverb says. Words that sum up the recent predicament of Ecco, a Danish shoe manufacturer and retailer with thousands of stores and sales points all over the planet.
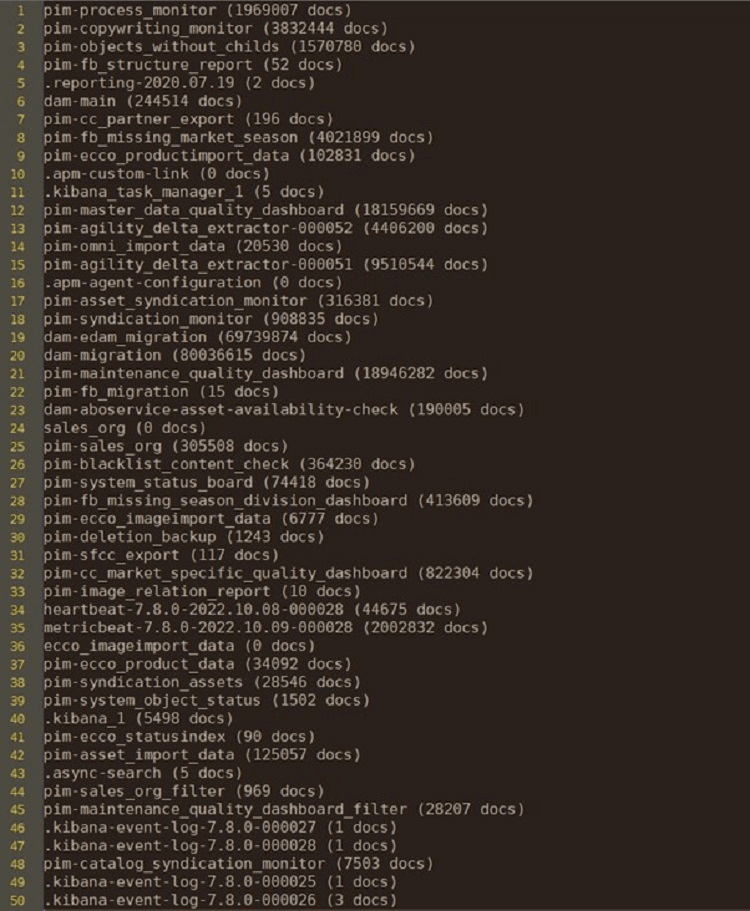
Our research team discovered an exposed instance hosting a trove of data for Ecco. The team has identified that Ecco left 50 indices exposed to the public, with over 60GB of data accessible since June 2021.
Millions of sensitive documents, from sales to system information, were accessible. Anyone with access could have viewed, edited, copied and stolen, or deleted the data.
We reached out to Ecco but received no reply before going to press. However, at the time of publishing, the company appears to have fixed the problem.
What happened?
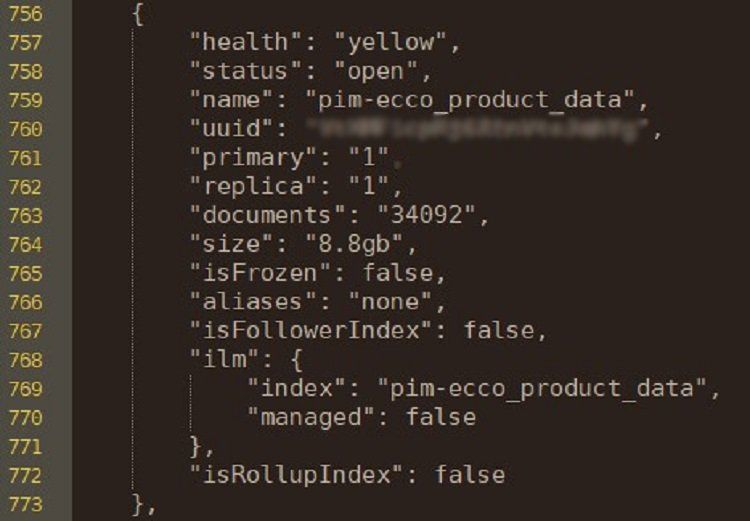
Our research team recently discovered an exposed instance that hosts Kibana, an ElasticSearch visualization dashboard, for Ecco. Kibana allows processing of information on ElasticSearch, a storage facility favored by enterprises dealing with large volumes of data.
Even though the instance hosting the dashboard was protected with a basic Hypertext Transfer Protocol (HTTP) authentication, the server was misconfigured and allowed all Application Programming Interface (API) requests through. Under an umbrella with leaky shoes, indeed.
The misconfigured authentication allowed us to look up the index names on Ecco’s ElasticSearch, revealing 50 exposed indices with over 60GB of data. The exposed servers contain documents ranging from sales and marketing to logging and system information.
According to the team, historical data indicates that the exposed database was left accessible for at least 506 days, since June 4, 2021. Over 35GB of data was added to the exposed database after the server misconfiguration opened a security hole in Ecco’s infrastructure.
“A threat actor could change the visible code, naming, and URLs to phish or potentially make victims or employees install unwanted files, such as ransomware loaders or remote access tools on their browsers and devices, causing immense damage.”Cybernews researchers said.
“Immense damage”
The names of indices on the open server show that millions of documents were revealed. For example, a directory named sales_org contained over 300,000 documents. Another directory, titled market_specific_quality_dashboard, had over 820,000 records.
As the table with exposed indices shows, millions of documents covering various aspects of Ecco’s corporate life were accessible, from performance monitoring to information about system status.
Worryingly, the database appears to be linked with the ecco.com website, likely used by international Ecco websites, thus providing a skilled threat actor with the means to target the company globally.
According to the researchers, the capability to modify the data inside ElasticSearch would be a dangerous tool in the hands of persistent threat actors, allowing them to launch a campaign against Ecco stores, employees, and even clients.
“A threat actor could change the visible code, naming, and URLs to phish or potentially make victims or employees install unwanted files, such as ransomware loaders or remote access tools on their browsers and devices, causing immense damage,” Cybernews researchers said.
Why the misconfiguration discovered by CyberNews is dangerous?
Give a look at the original post published by CyberNews at https://cybernews.com/security/ecco-leaks-sensitive-data-for-months/
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on Patreon using the button below

To keep up to date follow us on the below channels.