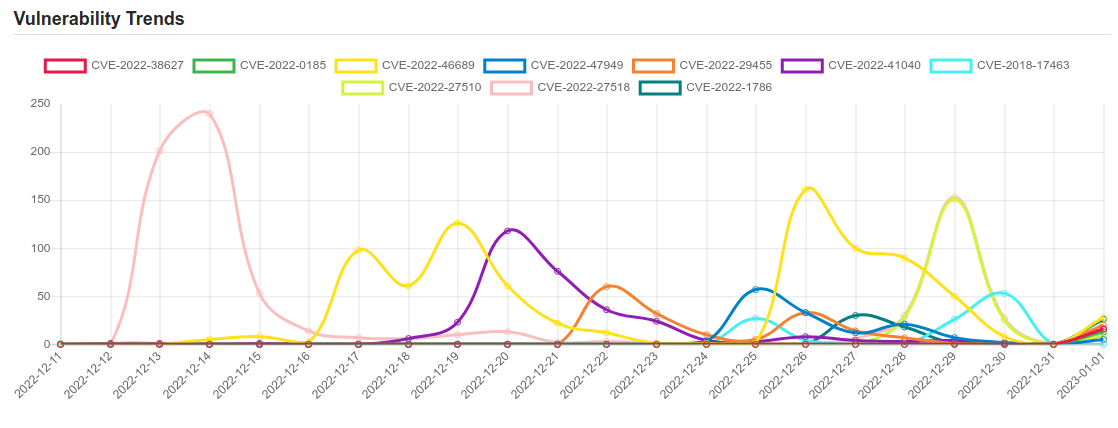
Daily Vulnerability Trends: Mon Jan 02 2023
| CVE NAME | CVE Description |
| CVE-2022-27510 | Unauthorized access to Gateway user capabilities |
| CVE-2022-27518 | Unauthenticated remote arbitrary code execution |
| CVE-2022-1786 | A use-after-free flaw was found in the Linux kernel’s io_uring subsystem in the way a user sets up a ring with IORING_SETUP_IOPOLL with more than one task completing submissions on this ring. This flaw allows a local user to crash or escalate their privileges on the system. |
| CVE-2022-48196 | Certain NETGEAR devices are affected by a buffer overflow by an unauthenticated attacker. This affects RAX40 before 1.0.2.60, RAX35 before 1.0.2.60, R6400v2 before 1.0.4.122, R6700v3 before 1.0.4.122, R6900P before 1.3.3.152, R7000P before 1.3.3.152, R7000 before 1.0.11.136, R7960P before 1.4.4.94, and R8000P before 1.4.4.94. |
| CVE-2021-44228 | Apache Log4j2 2.0-beta9 through 2.15.0 (excluding security releases 2.12.2, 2.12.3, and 2.3.1) JNDI features used in configuration, log messages, and parameters do not protect against attacker controlled LDAP and other JNDI related endpoints. An attacker who can control log messages or log message parameters can execute arbitrary code loaded from LDAP servers when message lookup substitution is enabled. From log4j 2.15.0, this behavior has been disabled by default. From version 2.16.0 (along with 2.12.2, 2.12.3, and 2.3.1), this functionality has been completely removed. Note that this vulnerability is specific to log4j-core and does not affect log4net, log4cxx, or other Apache Logging Services projects. |
| CVE-2023-0028 | Cross-site Scripting (XSS) – Stored in GitHub repository linagora/twake prior to 2023.Q1.1200+. |
| CVE-2014-125030 | A vulnerability, which was classified as critical, has been found in taoeffect Empress. Affected by this issue is some unknown functionality. The manipulation leads to use of hard-coded password. The name of the patch is 557e177d8a309d6f0f26de46efb38d43e000852d. It is recommended to apply a patch to fix this issue. VDB-217154 is the identifier assigned to this vulnerability. |
| CVE-2021-4034 | A local privilege escalation vulnerability was found on polkit’s pkexec utility. The pkexec application is a setuid tool designed to allow unprivileged users to run commands as privileged users according predefined policies. The current version of pkexec doesn’t handle the calling parameters count correctly and ends trying to execute environment variables as commands. An attacker can leverage this by crafting environment variables in such a way it’ll induce pkexec to execute arbitrary code. When successfully executed the attack can cause a local privilege escalation given unprivileged users administrative rights on the target machine. |
| CVE-2022-47940 | An issue was discovered in ksmbd in the Linux kernel 5.15 through 5.18 before 5.18.18. fs/ksmbd/smb2pdu.c lacks length validation in the non-padding case in smb2_write. |
| CVE-2023-00001 | No description provided |
| CVE-2021-34979 | This vulnerability allows network-adjacent attackers to execute arbitrary code on affected installations of NETGEAR R6260 1.1.0.78_1.0.1 routers. Authentication is not required to exploit this vulnerability. The specific flaw exists within the handling of SOAP requests. When parsing the SOAPAction header, the process does not properly validate the length of user-supplied data prior to copying it to a fixed-length buffer. An attacker can leverage this vulnerability to execute code in the context of root. Was ZDI-CAN-13512. |
| CVE-2022-34538 | Digital Watchdog DW MEGApix IP cameras A7.2.2_20211029 was discovered to contain a command injection vulnerability in the component /admin/vca/bia/addacph.cgi. This vulnerability is exploitable via a crafted POST request. |
| CVE-2022-45213 | perfSONAR before 4.4.6 inadvertently supports the parse option for a file:// URL. |
| CVE-2022-38627 | No description provided |
| CVE-2022-0185 | A heap-based buffer overflow flaw was found in the way the legacy_parse_param function in the Filesystem Context functionality of the Linux kernel verified the supplied parameters length. An unprivileged (in case of unprivileged user namespaces enabled, otherwise needs namespaced CAP_SYS_ADMIN privilege) local user able to open a filesystem that does not support the Filesystem Context API (and thus fallbacks to legacy handling) could use this flaw to escalate their privileges on the system. |
|
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.  To keep up to date follow us on the below channels.     
|

![[INCRANSOM] - Ransomware Victim: CF Construction Ltd 7 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)
