Fingerprintx – Standalone Utility For Service Discovery On Open Ports!
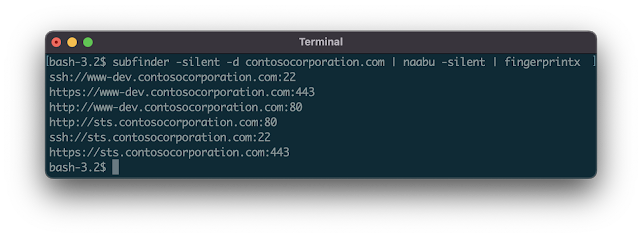
fingerprintx is a utility similar to httpx that also supports fingerprinting services like as RDP, SSH, MySQL, PostgreSQL, Kafka, etc. fingerprintx can be used alongside port scanners like Naabu to fingerprint a set of ports identified during a port scan. For example, an engineer may wish to scan an IP range and then rapidly fingerprint the service running on all the discovered ports.
Features
- Fast fingerprinting of exposed services
- Application layer service discovery
- Plays nicely with other command line tools
- Automatic metadata collection from identified services
Supported Protocols:
| SERVICE | TRANSPORT | SERVICE | TRANSPORT |
|---|---|---|---|
| HTTP | TCP | REDIS | TCP |
| SSH | TCP | MQTT3 | TCP |
| MODBUS | TCP | VNC | TCP |
| TELNET | TCP | MQTT5 | TCP |
| FTP | TCP | RSYNC | TCP |
| SMB | TCP | RPC | TCP |
| DNS | TCP | OracleDB | TCP |
| SMTP | TCP | RTSP | TCP |
| PostgreSQL | TCP | MQTT5 | TCP (TLS) |
| RDP | TCP | HTTPS | TCP (TLS) |
| POP3 | TCP | SMTPS | TCP (TLS) |
| KAFKA | TCP | MQTT3 | TCP (TLS) |
| MySQL | TCP | RDP | TCP (TLS) |
| MSSQL | TCP | POP3S | TCP (TLS) |
| LDAP | TCP | LDAPS | TCP (TLS) |
| IMAP | TCP | IMAPS | TCP (TLS) |
| SNMP | UDP | Kafka | TCP (TLS) |
| OPENVPN | UDP | NETBIOS-NS | UDP |
| IPSEC | UDP | DHCP | UDP |
| STUN | UDP | NTP | UDP |
| DNS | UDP |
Installation
From Github
go install github.com/praetorian-inc/fingerprintx/cmd/fingerprintx@latestFrom source (go version > 1.18)
$ git clone [email protected]:praetorian-inc/fingerprintx.git
$ cd fingerprintx
# build
docker build -t fingerprintx .
# and run it
docker run --rm fingerprintx -h
docker run --rm fingerprintx -t praetorian.com:80 --jsonUsage
fingerprintx -hThe -h option will display all of the supported flags for fingerprintx.
Usage:
fingerprintx [flags]
TARGET SPECIFICATION:
Requires a host and port number or ip and port number. The port is assumed to be open.
HOST:PORT or IP:PORT
EXAMPLES:
fingerprintx -t praetorian.com:80
fingerprintx -l input-file.txt
fingerprintx --json -t praetorian.com:80,127.0.0.1:8000
Flags:
--csv output format in csv
-f, --fast fast mode
-h, --help help for fingerprintx
--json output format in json
-l, --list string input file containing targets
-o, --output string output file
-t, --targets strings target or comma separated target list
-w, --timeout int timeout (milliseconds) (default 500)
-U, --udp run UDP plugins
-v, --verbose verbose modeThe fast mode will only attempt to fingerprint the default service associated with that port for each target. For example, if praetorian.com:8443 is the input, only the https plugin would be run. If https is not running on praetorian.com:8443, there will be NO output. Why do this? It’s a quick way to fingerprint most of the services in a large list of hosts (think the 80/20 rule).
Running Fingerprintx
With one target:
$ fingerprintx -t 127.0.0.1:8000
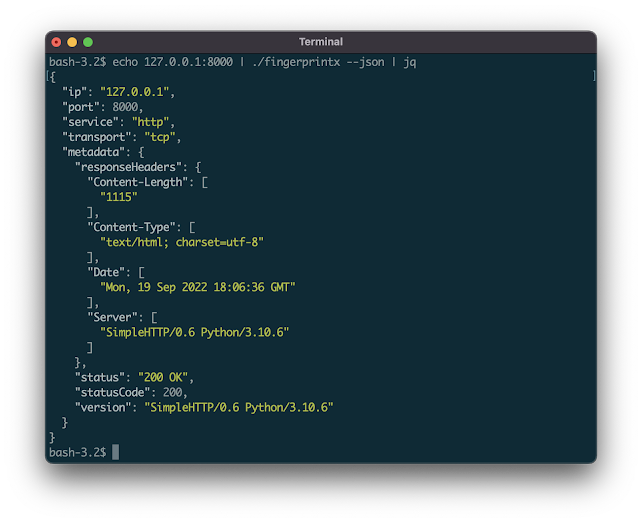
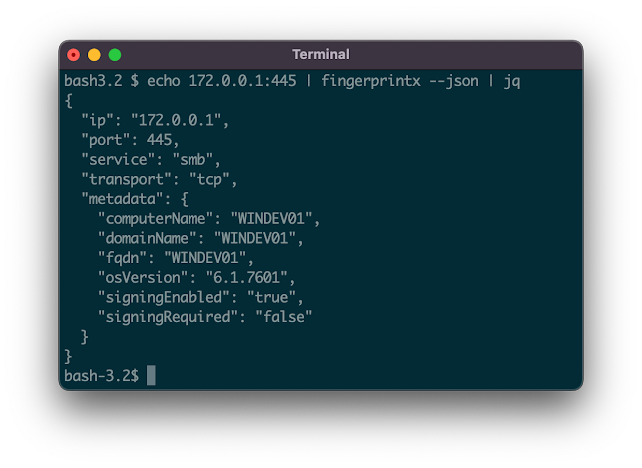
http://127.0.0.1:8000By default, the output is in the form: SERVICE://HOST:PORT. To get more detailed service output specify JSON with the --json flag:
$ fingerprintx -t 127.0.0.1:8000 --json
{"ip":"127.0.0.1","port":8000,"service":"http","transport":"tcp","metadata":{"responseHeaders":{"Content-Length":["1154"],"Content-Type":["text/html; charset=utf-8"],"Date":["Mon, 19 Sep 2022 18:23:18 GMT"],"Server":["SimpleHTTP/0.6 Python/3.10.6"]},"status":"200 OK","statusCode":200,"version":"SimpleHTTP/0.6 Python/3.10.6"}}Pipe in output from another program (like naabu):
$ cat input.txt | fingerprintx
http://praetorian.com:80
telnet://telehack.com:23
# or if you prefer
$ fingerprintx -l input.txt
http://praetorian.com:80
telnet://telehack.com:23
With more metadata output:
Nmap is the standard for network scanning. Why use fingerprintx instead of nmap? The main two reasons are:
fingerprintxworks smarter, not harder: the first plugin run against a server with port 8080 open is the http plugin. The default service approach cuts down scanning time in the best case. Most of the time the services running on port 80, 443, 22 are http, https, and ssh — so that’s whatfingerprintxchecks first.fingerprintxsupports json output with the--jsonflag. Nmap supports numerous output options (normal, xml, grep), but they are often hard to parse and script appropriately.fingerprintxsupports json output which eases integration with other tools in processing pipelines.
Notes
- Why do you have a
third_partyfolder that imports the Go cryptography libraries?- Good question! The
sshfingerprinting module identifies the various cryptographic options supported by the server when collecting metadata during the handshake process. This makes use of a few unexported functions, which is why the Go cryptography libraries are included here with an export.go file.
- Good question! The
- Fingerprintx is not designed to identify open ports on the target systems and assumes that every
target:portinput is open. If none of the ports are open there will be no output as there are no services running on the targets. - How does this compare to zgrab2?
- The
zgrab2command line usage (and use case) is slightly different thanfingerprintx. Forzgrab2, the protocol must be specified ahead of time:echo praetorian.com | zgrab2 http -p 8000, which assumes you already know what is running there. Forfingerprintx, that is not the case:echo praetorian.com:8000 | fingerprintx. The “application layer” protocol scanning approach is very similar.
- The
Acknowledgements
fingerprintx is the work of a lot of people, including our great intern class of 2022. Here is a list of contributors so far:
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below


To keep up to date follow us on the below channels.