300,000+ Fortinet firewalls vulnerable to critical FortiOS RCE bug

Hundreds of thousands of FortiGate firewalls are vulnerable to a critical security issue identified as CVE-2023-27997, almost a month after Fortinet released an update that addresses the problem.
The vulnerability is a remote code execution with a severity score of 9.8 out of 10 resulting from a heap-based buffer overflow problem in FortiOS, the operating system that connects all Fortinet networking components to integrate them in the vendor’s Security Fabric platform.
CVE-2023-27997 is exploitable and allows an unauthenticated attacker to execute code remotely on vulnerable devices with the SSL VPN interface exposed on the web. In an advisory in mid-June, the vendor warned that the issue may have been exploited in attacks.
Fortinet addressed the vulnerability on June 11 before disclosing it publicly, by releasing FortiOS firmware versions 6.0.17, 6.2.15, 6.4.13, 7.0.12, and 7.2.5.
Offensive security solutions company Bishop Fox reported on Friday that despite the calls to patch, more than 300,000 FortiGate firewall appliances are still vulnerable to attacks and reachable over the public internet.
Bishop Fox researchers used the Shodan search engine to find devices that responded in a way that indicated an exposed SSL VPN interface. They achieved this by searching for appliances that returned a specific HTTP response header.
They filtered the results to those that redirected to ‘/remote/login,’ a clear indication of an exposed SSL VPN interface.
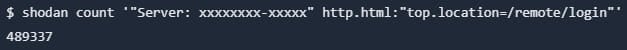
The query above showed 489,337 devices but not all of them were vulnerable to CVE-2023-27997, also referred to as Xortigate. Investigating further, the researchers discovered that 153,414 of the discovered appliances had been updated to a safe FortiOS version.
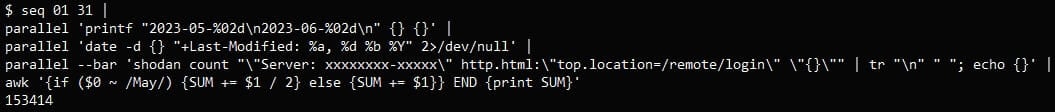
This means that roughly 335,900 of the FortiGate firewalls reachable over the web are vulnerable to attacks, a number that is significantly higher than the 250,000 recent estimation based on other, less accurate queries, Bishop Fox researchers say.
Another discovery Bishop Fox researchers made was that many of the exposed FortiGate devices did not receive an update for the past eight years, some of them running FortiOS 6, which reached end of support last year on September 29.
These devices are vulnerable to several critical-severity flaws that have proof-of-concept exploit code publicly available.
To demonstrate that CVE-2023-27997 can be used to execute code remotely on vulnerable devices, Bishop Fox created an exploit that allows “smashes the heap, connects back to an attacker-controlled server, downloads a BusyBox binary, and opens an interactive shell.”

source: Bishop Fox
“This exploit very closely follows the steps detailed in the original blog post by Lexfo […] and runs in approximately one second, which is significantly faster than the demo video on a 64-bit device shown by Lexfo,” Bishop Fox notes in their report.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.


