Global ransomware attacks at an all-time high, shows latest 2023 State of Ransomware report
Ransomware attacks have shown no signs of slowing down in 2023.
A new report from the Malwarebytes Threat Intelligence team shows 1,900 total ransomware attacks within just four countries—the US, Germany, France, and the UK—in one year.
The findings, compiled together in the 2023 State of Ransomware Report, show alarming trends in the global ransomware surge from July 2022 to June 2023. For example, the report shows that the US shouldered a hefty 43 percent of all global attacks and that ransomware attacks in France nearly doubled in the last five months.
To say ransomware gangs have been unkind to the US in the past year is an understatement.
Malwarebytes found that a total of 48 separate ransomware groups attacked the US in the observed period. To boot, there was a 75 percent increase in the average number of monthly attacks in the US between the first and second half of the last 12 months.
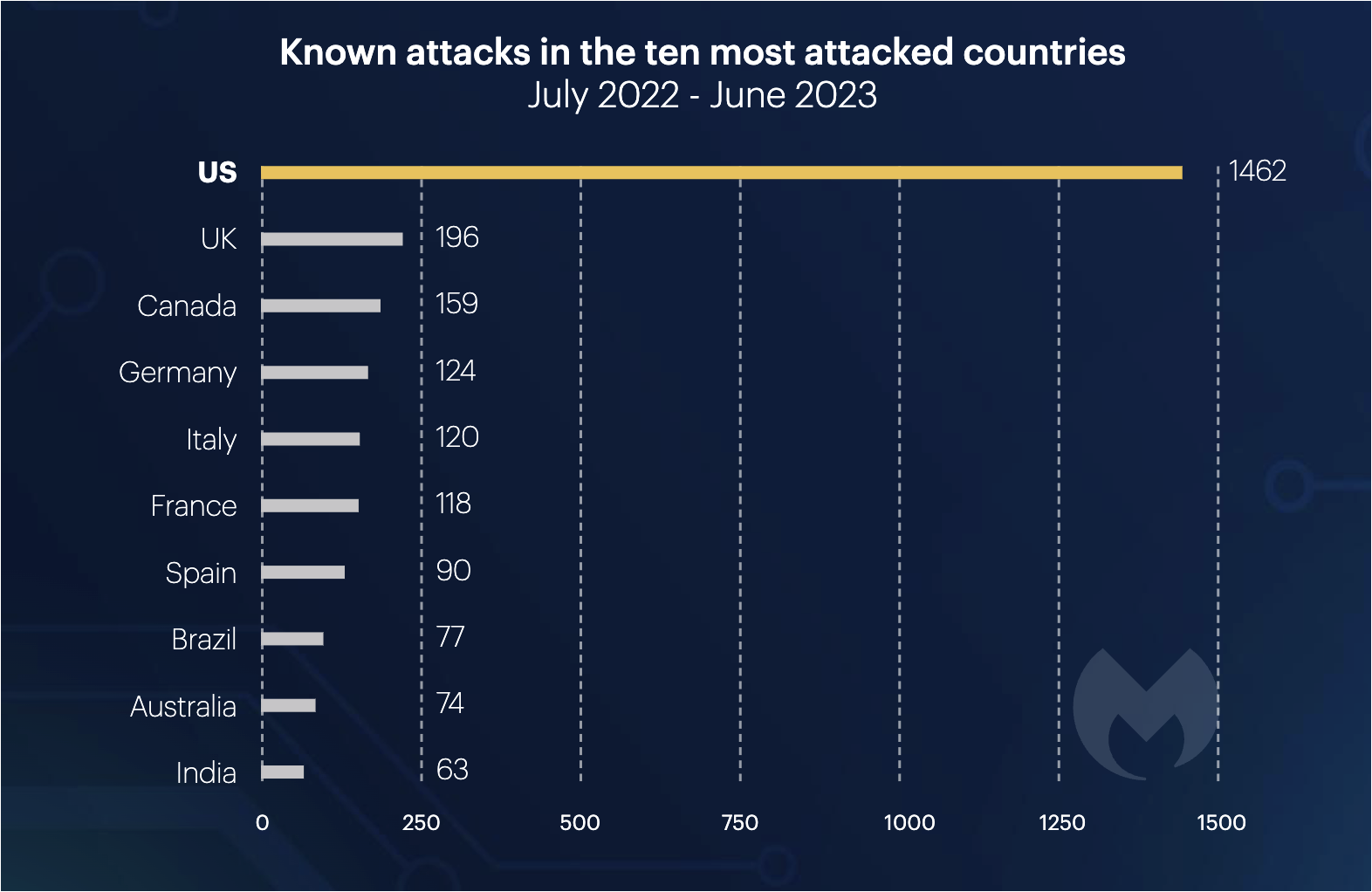
The UK, on the other hand, emerged as the second-largest ransomware target, enduring close to 200 ransomware attacks.
Malwarebytes tracked 32 separate ransomware groups attacking the UK, seven of which recorded more than ten known attacks. In addition, more ransomware gangs are attacking targets multiple times a month: the number of groups carrying out more than one known attack per month in the UK has climbed steadily for a year, from just one in July 2022 to eight in June 2023.
Neither France or Germany have been spared by the growing menace of ransomware, either.
Germany retained its place as the fourth most attacked country in the world, and the most attacked country outside of the anglosphere. France meanwhile experienced a disproportionately high rate of attacks on its government sector (9 percent of attacks).
Perhaps the biggest takeaway from the report, however, is that the ascension of the CL0P group—which has effectively harnessed zero-day vulnerabilities to amplify its attacks—could signal a change in the game.
A New Threat on the Horizon: CL0P
For a year and a half, LockBit, which claims to have 100 affiliates, has been the most dominant form of “Ransomware-as-a-Service” (RaaS) in the US, averaging about 24 attacks per month.
However, twice this year, in March and June, LockBit’s considerable rate of attacks was vastly exceeded by CL0P, which was otherwise dormant.
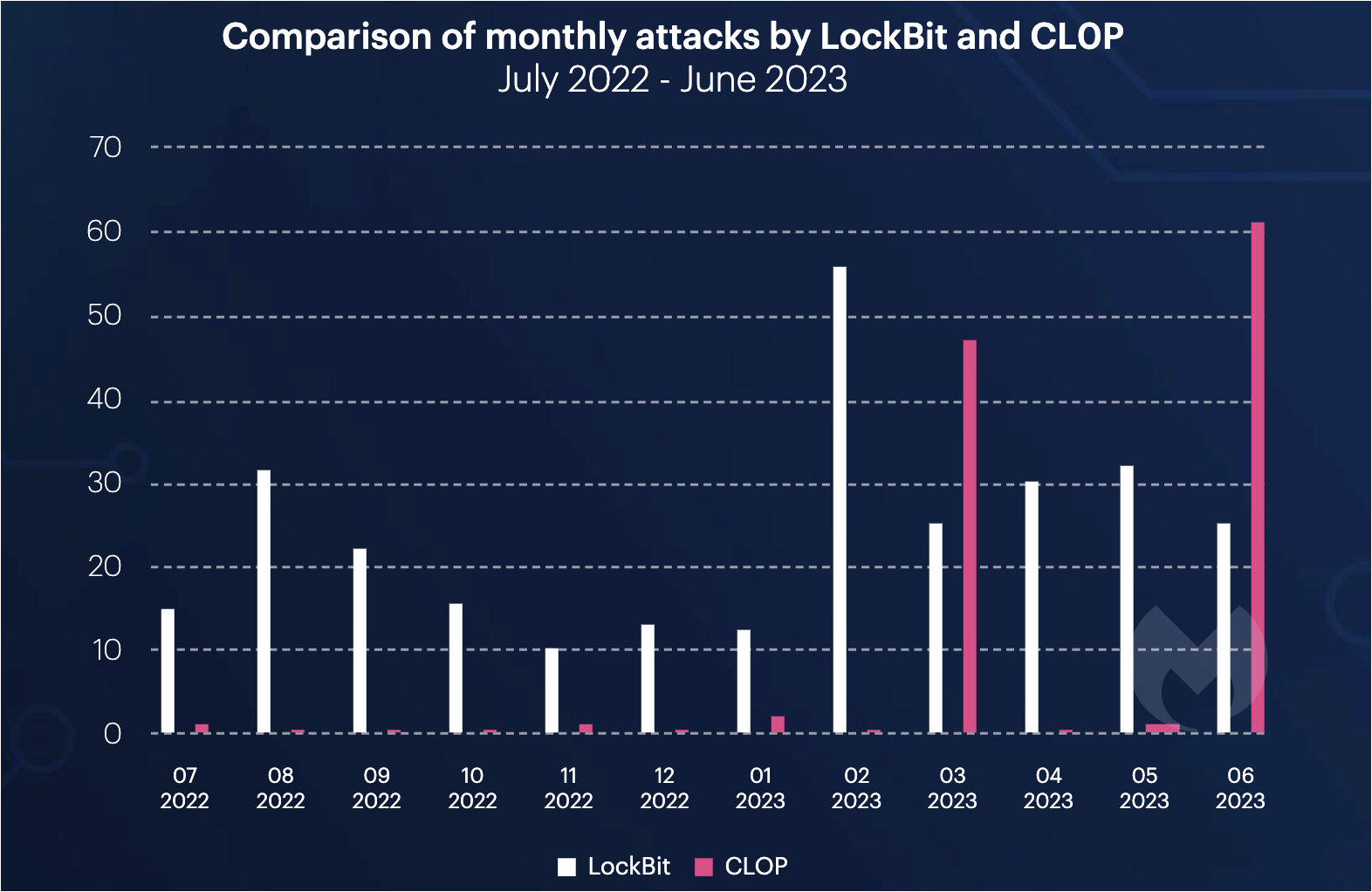
The drive behind the sudden change? CL0P used separate zero-days in GoAnywhere MFT and MOVEit Transfer to gain an edge. This gave them the ability to launch an unprecedented number of attacks within a short time frame and across a massive scale.
The use of zero-day vulnerabilities by ransomware groups like CL0P may trigger a significant shift in ransomware strategies, mirroring the adoption of the “double extortion” tactic in 2019.
If more groups start adopting CL0P’s zero-day exploitation techniques, the ransomware landscape could tilt from service-oriented attacks to a more aggressive, vulnerability-focused model—a move that could skyrocket the number of victims.
Want to learn more?
Read our 2023 State of Ransomware Report
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.


