INTERPOL Nabs Hacking Crew OPERA1ER’s Leader Behind $11 Million Cybercrime
A suspected senior member of a French-speaking hacking crew known as OPERA1ER has been arrested as part of an international law enforcement operation codenamed Nervone, Interpol has announced.
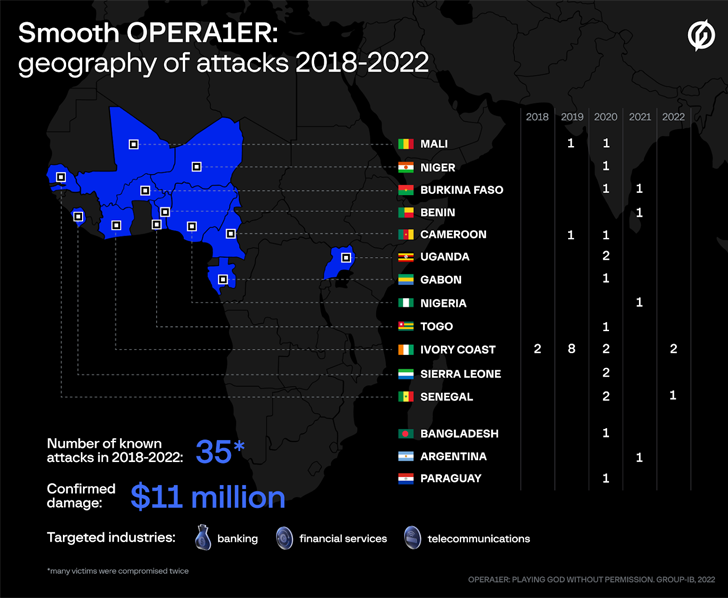
“The group is believed to have stolen an estimated USD 11 million — potentially as much as 30 million — in more than 30 attacks across 15 countries in Africa, Asia, and Latin America,” the agency said.
The arrest was made by authorities in Côte d’Ivoire early last month. Additional insight was provided by the U.S. Secret Service’s Criminal Investigative Division and Booz Allen Hamilton DarkLabs.
The financially motivated collective is also known by the aliases Common Raven, DESKTOP-GROUP, and NX$M$. Its modus operandi was first exposed by Group-IB and Orange CERT Coordination Center (Orange-CERT-CC) in November 2022, detailing its intrusions on banks, financial services, and telecom companies between March 2018 and October 2022.
Discover different approaches to conquer Privileged Account Management (PAM) challenges and level up your privileged access security strategy.
Claim Your SpotEarlier this January, Broadcom’s Symantec said it uncovered a set of targeted attacks against the financial sector in Francophone countries located in Africa from at least July 2022 to September 2022. The company said the activity, which it tracks as Bluebottle, has a degree of crossover with OPERA1ER.
Attack chains mounted by the group have leveraged spear-phishing lures that set off a chain of events that eventually leads to the deployment of post-exploitation tools like Cobalt Strike and Metasploit and off-the-shelf remote access trojans, which accommodate various functionalities to steal sensitive data.
OPERA1ER has also been observed maintaining access to compromised networks for a period ranging anywhere from three to twelve months, occasionally targeting the same company several times.
“Most of the messages were written in French, and mimicked fake tax office notifications or hiring offers,” Group-IB said. “OPERA1ER was able to get access to internal payment systems used by the affected organizations, and leveraged this to withdraw funds.”
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.

![[LYNX] - Ransomware Victim: Greta Group 1 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)
