Microsoft announced that a botnet dubbed MCCrash is launching distributed denial-of-service (DDoS) attacks against private Minecraft servers.
Microsoft announced that a botnet dubbed MCCrash is launching distributed denial-of-service (DDoS) attacks against private Minecraft servers.
Microsoft spotted a cross-platform botnet, tracked as MCCrash, which has been designed to launch distributed denial-of-service (DDoS) attacks against private Minecraft servers. The IT giant tracks this cluster of activity as DEV-1028.
The experts report that the botnet originates from malicious software downloads on Windows devices, but it supports a propagating mechanism to infect multiple Linux-based devices.
MCCrash enumerates default credentials on Internet-exposed Secure Shell (SSH)-enabled devices.
“The botnet’s spreading mechanism makes it a unique threat because while the malware can be removed from the infected source PC, it could persist on unmanaged IoT devices in the network and continue to operate as part of the botnet.” reads the post published by Microsoft. “The DEV-1028 botnet is known to launch distributed denial of service (DDoS) attacks against private Minecraft servers.”
The DDoS botnet was designed to target private Minecraft Java servers using crafted packets, experts believe it is behind a DDoS-for-hire service offered on forums or darknet sites.
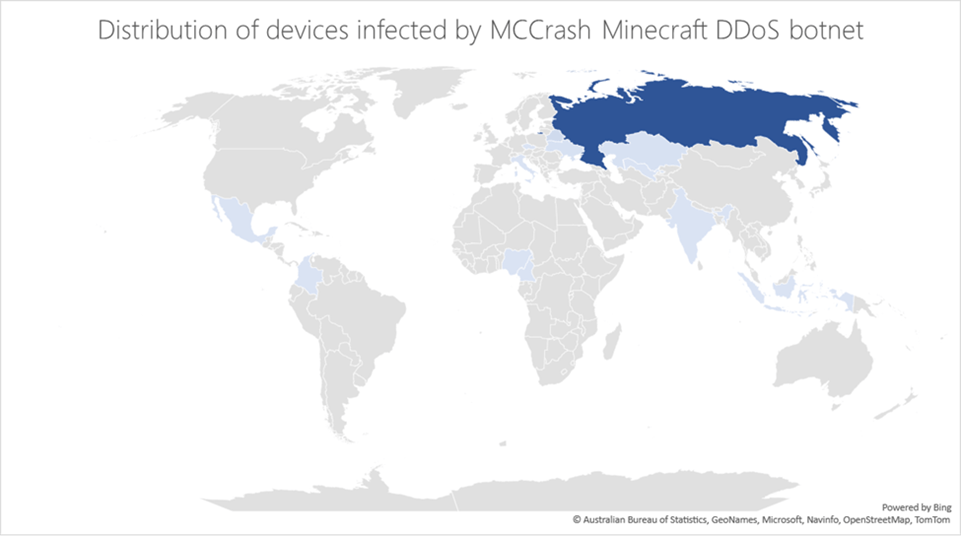
Most of the infections have been reported in Russia, other countries where experts observed infections are Kazakhstan, Uzbekistan, Ukraine, Belarus, Czechia, Italy, India, and Indonesia.
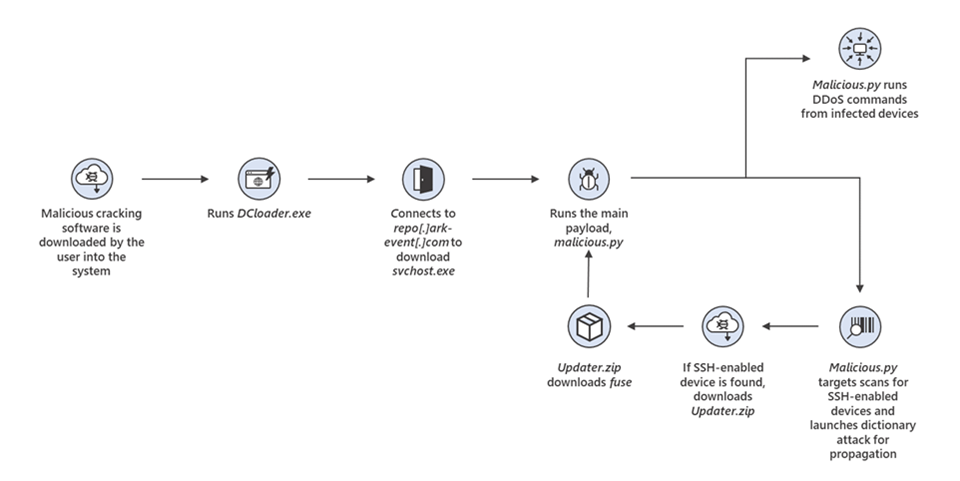
According to Microsoft, the initial infections were caused by the installation of malicious cracking tools that purport to acquire illegal Windows licenses.
Once the “cracking tool” is launched, it executes a PowerShell command to download and launch a fake version of svchost.exe.
The cracking tools contain additional code that downloads and launches a fake version of svchost.exe through a PowerShell command. In some cases, the downloaded file is named svchosts.exe.
Next, svchost.exe launches malicious.py, which is the main Python script that contains all the botnet logic. The malicious code scans the web for systems running Debian, Ubuntu, CentOS, and IoT workloads such as Raspbian, then launches a dictionary attack to propagate.
Once a device is found, the bot downloads the file Updater.zip from repo[.]ark—event[.]net onto the device to create the file fuse. Then, the fuse file downloads a copy of malicious.py onto the device.
“Based on our analysis, the botnet is primarily used to launch DDoS attacks against private Minecraft servers using known server DDoS commands and unique Minecraft commands.” continues the report. Below are some supported commands specifically designed to target Minecraft servers.
| ATTACK_RAKNET | Attack on RakNet protocol (used by Minecraft servers) |
| ATTACK_NETTY | Minecraft – Login handshake Packet |
| ATTACK_[MCBOT|MINE] | Minecraft – Login Start Packet |
| ATTACK_[MCPING|PING] | Minecraft – Login Success Packet |
| ATTACK_MCDATA | Minecraft – Login Handshake, Login Start and Close Window Packets |
| ATTACK_MCCRASH | Minecraft – Login Handshake and Login Start packets, using Username with env variable |
The ATTACK_MCCRASH command sends ${env:random payload of specific size:-a} as the username in order to saturate the resources of the server and make it crash.
The analysis of the malware revealed that it was designed to target Minecraft server 1.12.2 version, however, the experts speculate all versions between 1.7.2 and 1.18.2 can be affected by this attack.
“The wide range of at-risk Minecraft servers highlights the impact this malware could have had if it was specifically coded to affect versions beyond 1.12.2. The unique ability of this threat to utilize IoT devices that are often not monitored as part of the botnet substantially increases its impact and reduces its chances of being detected.” concludes the post.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on Patreon using the button below

To keep up to date follow us on the below channels.