Microsoft to kill off VBScript in Windows to block malware delivery

Microsoft is planning to phase out VBScript in future Windows releases after 30 years of use, making it an on-demand feature until it is removed.
VBScript (also known as Visual Basic Script or Microsoft Visual Basic Scripting Edition) is a programming language similar to Visual Basic or Visual Basic for Applications (VBA) and was introduced almost 30 years ago, in August 1996.
It comes bundled with Internet Explorer (which was killed off by Redmond across some Windows 10 platforms in February), integrates active scripting into Windows environments, and communicates with host applications through Windows Script.
“VBScript is being deprecated. In future releases of Windows, VBScript will be available as a feature on demand before its removal from the operating system,” the company said this week.
“Initially, the VBScript feature on demand will be preinstalled to allow for uninterrupted use while you prepare for the retirement of VBScript.”
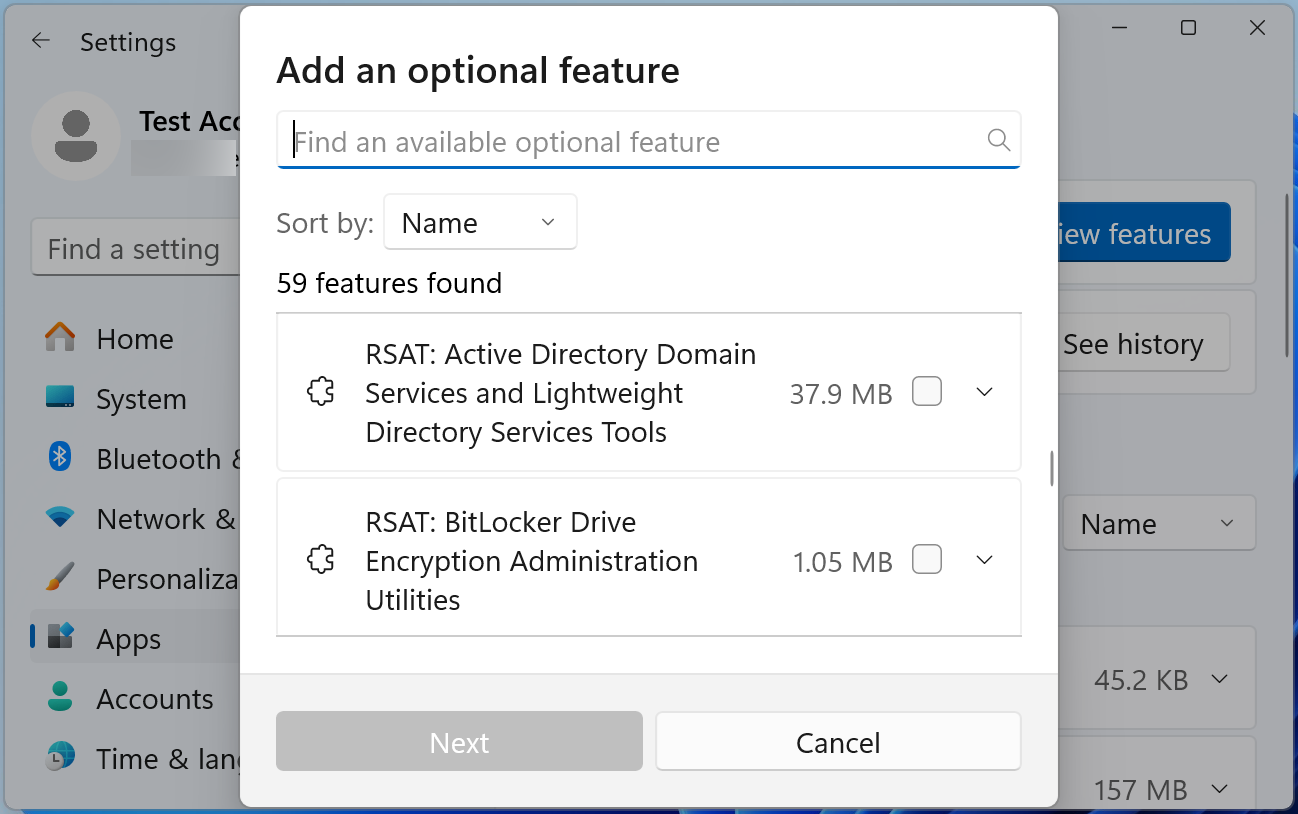
Features on Demand (FODs) are optional features within the Windows operating system like the .NET Framework (.NetFx3), Hyper-V, and the Windows Subsystem for Linux that aren’t installed by default but can be added whenever necessary.
With the July 2019 Patch Tuesday cumulative updates, Microsoft also disabled VBScript by default in Internet Explorer 11 on Windows 10.
One less malware infection vector
Although not officially explained, Microsoft’s decision to deprecate VBScript is likely tied to the earlier discontinuation of Internet Explorer this year. Fortunately, as a consequence, a prevalent infection vector employed by threat actors to infect Windows systems with malicious payloads has also been eliminated.
This move is part of a broader strategy to mitigate the increasing prevalence of malware campaigns exploiting various Windows and Office features for infections.
Malicious actors have used VBScript to distribute malware, including notorious strains like Lokibot, Emotet, Qbot, and, more recently, DarkGate malware, among others, onto victims’ computers.
The effort traces back to 2018 when Microsoft extended support for AMSI to Office 365 applications, curbing attacks that utilized VBA macros.
Subsequently, Microsoft disabled Excel 4.0 (XLM) macros, introduced XLM macro protection, mandated default blocking of VBA Office macros, and began blocking untrusted XLL add-ins by default in Microsoft 365 tenants worldwide.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.


