5 Must-Know Facts about 5G Network Security and Its Cloud Benefits
5G is a game changer for mobile connectivity, including mobile connectivity to the cloud. The technology provides high speed and low latency when connecting smartphones and IoT devices to cloud infrastructure. 5G networks are a critical part of all infrastructure layers between the end user and the end service; these networks transmit sensitive data that can be vital for governments and businesses, not to mention individuals. As a result, 5G networks are a prime target for attackers. For this reason, cybersecurity has been a key consideration in developing the 5G standard.
5G encompasses robust security features that guarantee confidentiality, integrity, and availability of network services and user data. In this article, Seva Vayner, Product Owner of Gcore’s Edge Cloud service, gives a deep dive into five of 5 G’s cutting-edge security measures. He also delves into the pivotal performance capabilities of 5G, accompanied by use cases that demonstrate how contemporary, cloud-native enterprises can leverage this transformative technology to their advantage.
What Is 5G#
5G is the new standard of wireless networks that supersedes 4G (LTE). It is designed to connect people and devices at fast speeds with low latency.
The throughput of 5G far exceeds the throughput of 4G. In theory, 5G offers up to 20 Gbps in the downlink. In comparison, 4G only offers up to 100 Mbps, 200 times less than 5G. According to the 2023 CELLSMART survey, in practice, outdoor tests show that 5G operators in the US and EU provide close to 1 Gbps for the downlink channel.
As for 5G latency, it can be up to 10 ms (vs. 30 ms in 4G)—but only in a test environment. In reality, latency depends on many factors. For example, Ericsson’s tests in the US showed that 5G latency is typically around 20 ms but no more than 50 ms, which is virtually unnoticeable to humans. This is good news for gaming, where latency higher than 50 ms is critical.
5 Must-Know Security Features of 5G#
Essential 5G security methods and technologies include encryption, privacy protection, authentication and authorization, network slicing, and network equipment security assurance. Let’s look at them in more detail.
1. Encryption#
Encryption protects user data and network traffic from eavesdropping, interception, and tampering. 5G uses strong encryption algorithms such as AES, ZUC, SNOW 3G, and HMAC-SHA-256. The encryption features include a separation of the security keys between the core network segments. Also offered is fast synchronization of the security contexts in the access network (base stations) and the core network.
2. Privacy Protection #
In 5G networks, privacy protection is ensured through the use of encryption and various other techniques. These strategies effectively guard against significant threats like IMSI/TMSI-catchers, which attackers commonly use to identify and track network subscribers. Mobile operators can implement the Elliptic Curve Integrated Encryption Scheme mechanism to conceal and regularly update a subscriber’s temporary identifier (TMSI). In addition, operators can detect false base stations, which are often the source of IMSI/TMSI-catchers.
3. Authentication and Authorization#
Authentication and authorization in 5G is based on the Authentication and Key Agreement method (5G AKA). It includes a robust authentication mechanism to verify the identity of users, devices, and network elements. Unlike 4G, 5G doesn’t require physical SIM cards for credentials, but also supports pre-shared keys, certificates, and tokens. Mobile operators can choose the authentication credentials and authentication methods best suited to their customers and IoT devices. For example, traditional SIM cards are suitable for mobile phones, while digital credentials are more appropriate for simple IoT devices equipped with eSIM.
4. Network Slicing#
Network slicing allows the creation of virtual networks for different services and applications. For instance, a subscribing company can use one network slice for high-priority employees with access to corporate services, and another slice for low-priority IoT warehouse sensors that transmit data to storage in a public cloud. Each network slice can be assigned specific security policies and protocols, helping to isolate and protect data and services.
5. NESAS#
NESAS, or the Network Equipment Security Assurance Scheme, ensures the secure implementation of telecom equipment that mobile operators use in their networks, including 5G. Developed by 3GPP and GSMA, NESAS establishes security requirements and rules for successful infrastructure audits. NESAS takes into account both local and global cybersecurity regulations, for example, the EU cybersecurity certification framework. It is mandatory for vendors and mobile operators to comply with NESAS requirements.
How 5G Benefits Cloud-Native Companies#
With its low latency, higher bandwidth, and extensive security measures, 5G strengthens the security of cloud connectivity. This upgrade enables secure and reliable transmission of sensitive information as well as real-time data processing. 5G allows organizations to confidently use cloud services to store and manage their data, reducing the risk of data breaches.
5G offers superior fault tolerance when compared to cable connections, primarily due to the inherent resilience of wireless channels in mitigating communication failures. With a cable connecting an office or factory to a provider, it might be necessary to build a backup connection through an optical fiber or radio. But 5G has a reserved channel from the outset. If one base station fails, others will take over automatically, making downtime unlikely.
In addition, 5G network slicing capabilities provide companies with dedicated virtual networks within their IT system. This enables better isolation and segregation of data, applications, and services, improving overall security. Enterprises can create customized network slices for specific tasks or particular departments. This feature ensures that critical data and applications remain separate and protected.
Where 5G Can Be Useful in Conjunction with the Cloud#
Healthcare. Doctors can use tools like a cloud AI platform to remotely monitor patient health data in real time while remaining mobile via 5G. After the medical examination, high-resolution medical device images can be uploaded to the Cloud AI platform, processed, and returned to a doctor for further use. 5G also helps with ML diagnostics: a cloud ML application can receive images or other medical data over 5G for disease prediction, detection, and classification.
Secure access to corporate tools. With 5G data protection, access control management is enabled for each SIM card. Authorized employees can securely access corporate digital assets, data, and applications while working remotely without the need for a VPN or firewall is required.
Streaming. With 5G and cloud services like CDN, streamers, bloggers, and podcasters can enjoy uninterrupted, high-quality, live video and audio streaming. 5G facilitates the fusion of interactive elements within live video streams while instant video analytics generate real-time metrics that enrich the overall live event experience.
Smart factories. Manufacturers can predict maintenance needs and detect potential problems or failures by monitoring equipment data with IoT devices. They can use ML cloud services for analytics, while 5G provides a secure and fast connection to their cloud infrastructure.
Automotive IoT. Because of their performance capabilities, 5G networks are a superior means of data transmission in industries. In the self-driving vehicle industry, data from the vehicle’s sensors and cameras can be easily sent to the cloud at high speeds, and then processed by cloud AI tools.
Gcore’s 5G eSIM Platform#
The 5G eSIM platform from the global cloud and CDN provider Gcore provides a powerful example of a collaborative 5G and cloud solution. The 5G eSIM platform offers access to IaaS, PaaS, AI infrastructure, a streaming platform, and other Gcore services over 5G. Gcore’s customers can securely connect to their cloud infrastructure via a direct private channel from more than 150 countries worldwide. 5G eSIM ensures secure data transmission through advanced encryption algorithms and security protocols.
Here is the architecture of the platform:
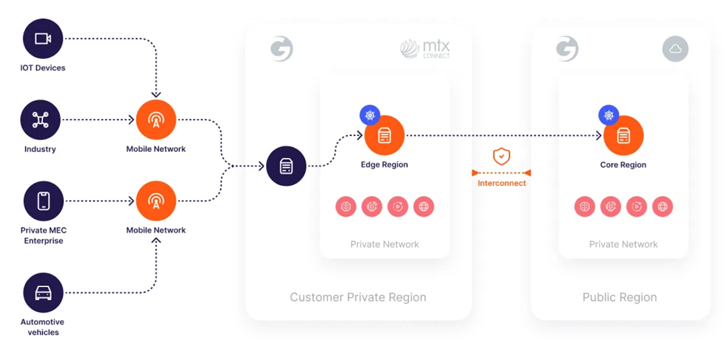 |
| Figure 1. Gcore’s 5G eSIM Platform architecture |
Besides the 5G security features that are built-in in the standard, the 5G eSIM platform provides:
- Control of traffic consumption for configuring a white list and a black list. These allow or deny specific protocols, URLs, and IPs.
- Workgroup management for assigning employees’ names to eSIMs and grouping them by function, seniority, or department.
- Detailed reporting system to view the report by group, period, eSIM, country, and more.
- Personal eSIMs for each employee to assign them a corporate mobile number. Employees can access the internet and internal resources from a remote location without the need for a corporate VPN and without roaming charges.
- Secured individual routing and traffic filtering to ensure protection against cyberattacks and data leakage.
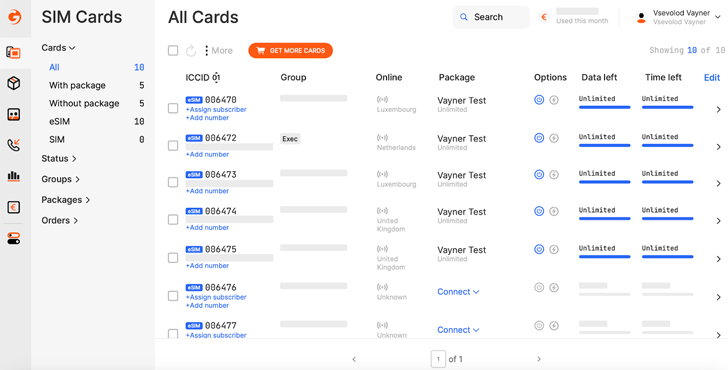 |
| Figure 2. Gcore’s 5G eSIM control panel |
In addition, Gcore provides functionality within its Cloud to secure all customer services:
- Identity and access management
- Firewall with flexible security group configuration
- Secrets management
- IaaS protection
Customers can combine these cloud features with the benefits and features offered by the 5G eSIM platform.
Conclusion#
5G has excellent performance capabilities and advanced security features such as encryption, network slicing, and 5G AKA. 5G networks are more resilient and flexible than LAN and WLAN networks; this makes 5G more effective in terms of technological advancements, business interests, and compliance with security requirements. As a result, 5G networks help businesses evolve faster without reducing the level of infrastructure protection.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below


To keep up to date follow us on the below channels.






![[QILIN] - Ransomware Victim: Mainetti 10 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)

