New Boldmove Linux malware used to backdoor Fortinet devices

Suspected Chinese hackers exploited a recently disclosed FortiOS SSL-VPN vulnerability as a zero-day in December, targeting a European government and an African MSP with a new custom ‘BOLDMOVE’ Linux and Windows malware.
The vulnerability is tracked as CVE-2022-42475 and was quietly fixed by Fortinet in November. Fortinet publicly disclosed the vulnerability in December, urging customers to patch their devices as threat actors were actively exploiting the flaw.
The flaw allows remote unauthenticated attackers to crash targeted devices remotely or gain remote code execution.
However, it was not until this month that Fortinet shared more details about how hackers exploited it, explaining that threat actors had targeted government entities with custom malware specifically designed to run on FortiOS devices.
The attackers were focused on maintaining persistence on exploited devices by using the custom malware to patch the FortiOS logging processes so that specific log entries could be removed or to disable the logging process altogether.
Yesterday, Mandiant published a report about a suspected Chinese espionage campaign leveraging the FortiOS flaw since October 2022 using a new ‘BOLDMOVE’ malware explicitly designed for attacks on FortiOS devices.
The new BOLDMOVE malware
BOLDMOVE is a full-featured backdoor written in C that enables Chinese hackers to gain higher-level control over the device, with the Linux version specifically created to run on FortiOS devices.
Mandiant identified several versions of BOLDMOVE with varying capabilities, but the core set of features observed across all samples include:
- Performing system surveying.
- Receiving commands from the C2 (command and control) server.
- Spawning a remote shell on the host.
- Relaying traffic through the breached device.
The commands supported by BOLDMOVE allow threat actors to remotely manage files, execute commands, interactive shell creation, and backdoor control.
The Windows and Linux variants are largely the same but utilize different libraries, and Mandiant believes the Windows version was compiled in 2021, almost a year before the Linux variant.
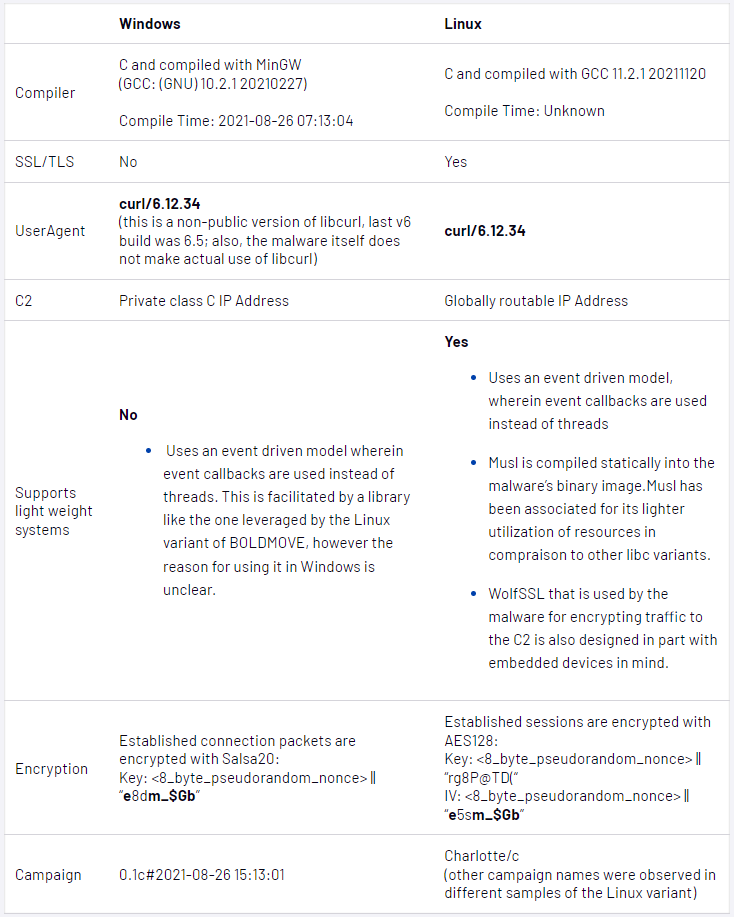
However, the most significant difference between the Linux and Windows versions is that one of the Linux variants contains functionality that specifically targets FortiOS devices.
For example, a Linux BOLDMOVE version allows attackers to modify Fortinet logs on the compromised system or disable logging daemons (miglogd and syslogd) altogether, thus making it harder for the defenders to track the intrusion.
Moreover, this version of BOLDMOVE can send requests to internal Fortinet services, allowing attackers to send network requests to the entire internal network and spread laterally to other devices.
Chinese cyber-espionage group will continue to target unpatched internet-facing devices like firewalls and IPS/ISD appliances as they offer easy network access without requiring interaction.
Unfortunately, it’s not simple for defenders to scrutinize what processes run in these devices, and Mandiant says native security mechanisms do not work very well to protect them.
“There is no mechanism to detect malicious processes running on such devices, nor telemetry to proactively hunt for malicious images deployed on them following an exploitation of a vulnerability,” explains Mandiant in the report.
“This makes network devices a blind spot for security practitioners and allows attackers to hide in them and maintain stealth for long periods, while also using them to gain foothold in a targeted network.”
The appearance of a custom-made backdoor for one of those devices proves the threat actors’ deep understanding of how perimeter network devices operate and the initial access opportunity they represent.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on Patreon using the button below

To keep up to date follow us on the below channels.





![[QILIN] - Ransomware Victim: Culver's Lawn & Landscape, Inc[.] 8 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)

