New iLeakage attack steals emails, passwords from Apple Safari

Academic researchers created a new speculative side-channel attack they named iLeakage that works on all recent Apple devices and can extract sensitive information from the Safari web browser.
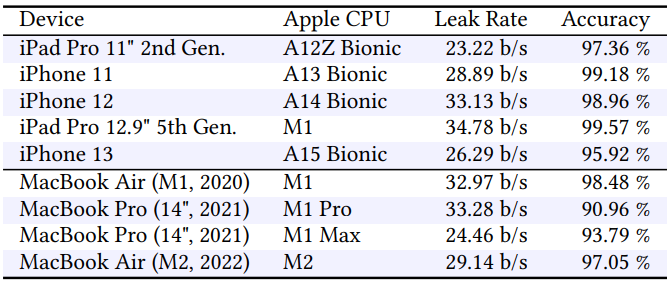
iLeakage is the first demonstration of a speculative execution attack against Apple Silicon CPUs and the Safari browser. It can be used to retrieve with “near perfect accuracy” data from Safari, as well as Firefox, Tor, and Edge on iOS.
At core, it is a timerless Spectre attack that bypasses standard side-channel protections implemented by all browser vendors.
Stealing secrets from Safari
iLeakage was developed by a team of academics from Georgia Tech, University of Michigan, and Ruhr University Bochum who examined Safari’s side-channel resilience and managed to bypass existing countermeasures by implementing a timerless and architecture-agnostic method based on race conditions.
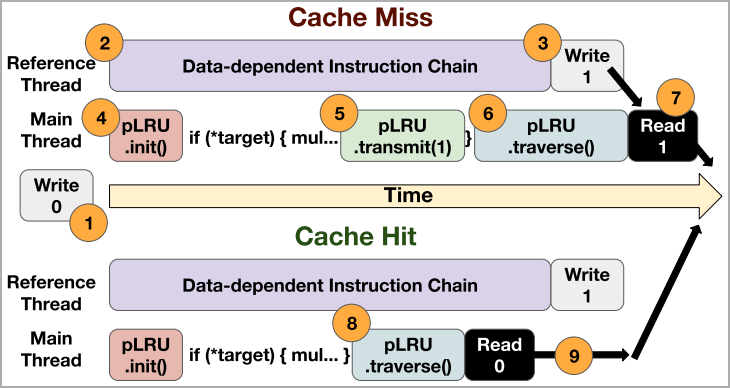
The researchers focused on reading sensitive information from Safari and were able to steal data by creating a primitive that can speculatively read and leak any 64-bit pointer in the address space Apple’s browser uses for the rendering process.
They achieved this by defeating the side-channel protections Apple implemented in its browser, e.g. low-resolution timer, compressed 35-bit addressing, and value poisoning.
The researchers also bypassed the site isolation policy in Safari, which separates websites into different address spaces based on their effective top-level domain (eTLD) plus one subdomain.
They used a new technique that uses the JavaScript window.open API allows an attacker page to share the same address space as arbitrary victim pages.
By using using speculative type confusion to bypass Apple’s compressed 35-bit addressing and value poisoning countermeasures, the researchers could leak sensitive data from the target page, such as passwords and emails.
The proof-of-concept code for the attack is in JavaScript and WebAssembly, the two programming languages for delivering dynamic web content.
The video below shows how Gmail messages in Safari running an iPad were retrieved using the iLeakage attack. The basic requirement for the attack to work is that the victim user interacts with the attacker’s page.
The researchers used the same method to retrieve a password for an Instagram test account that was auto-filled in the Safari web browser using the LastPass password management service.
In another experiment, the researchers demonstrated how the iLeakage attacks also works on Chrome for iOS and were able to retrieve the YouTube watch history.
They explain that Apple’s policy forces all third-party iOS browsers to be overlays on top of Safari and use Apple browser’s JavaScript engine.
iLeakage relies on the exploitation of speculative execution in Apple Silicon chips (M1, M2), where the CPU’s predictive execution performs tasks most likely to be needed but before knowing if they are required or not.
This mechanism, present in all modern CPUs, dramatically improves performance; however, design flaws can cause data leaks, as proven by the Meltdown and Spectre attacks disclosed almost six years ago.
More details on the attack and the individual methods used for bypassing Apple’s mitigations are available in the technical paper the researchers published.
Impact and defense tips
iLeakage impacts all Apple devices released from 2020 that are powered by Apple’s A-series and M-series ARM processors.
The attack is largely undetectable, leaving no traces on the victim’s system in the form of logs, apart from maybe an entry of the attacker’s webpage in the browser cache.
Nevertheless, the researchers underline that the attack is difficult to carry out “and requires advanced knowledge of browser-based side-channel attacks and Safari’s implementation.”
iLeakage was reported privately to Apple on September 12, 2022 and the company developed the following mitigations for macOS:
- Open Terminal and run’ defaults write com.apple.Safari IncludeInternalDebugMenu 1′ to enable Safari’s hidden debug menu.
- Open Safari and head to the newly visible Debug menu.
- Select ‘WebKit Internal Features’
- Scroll and activate ‘Swap Processes on Cross-Site Window Open’
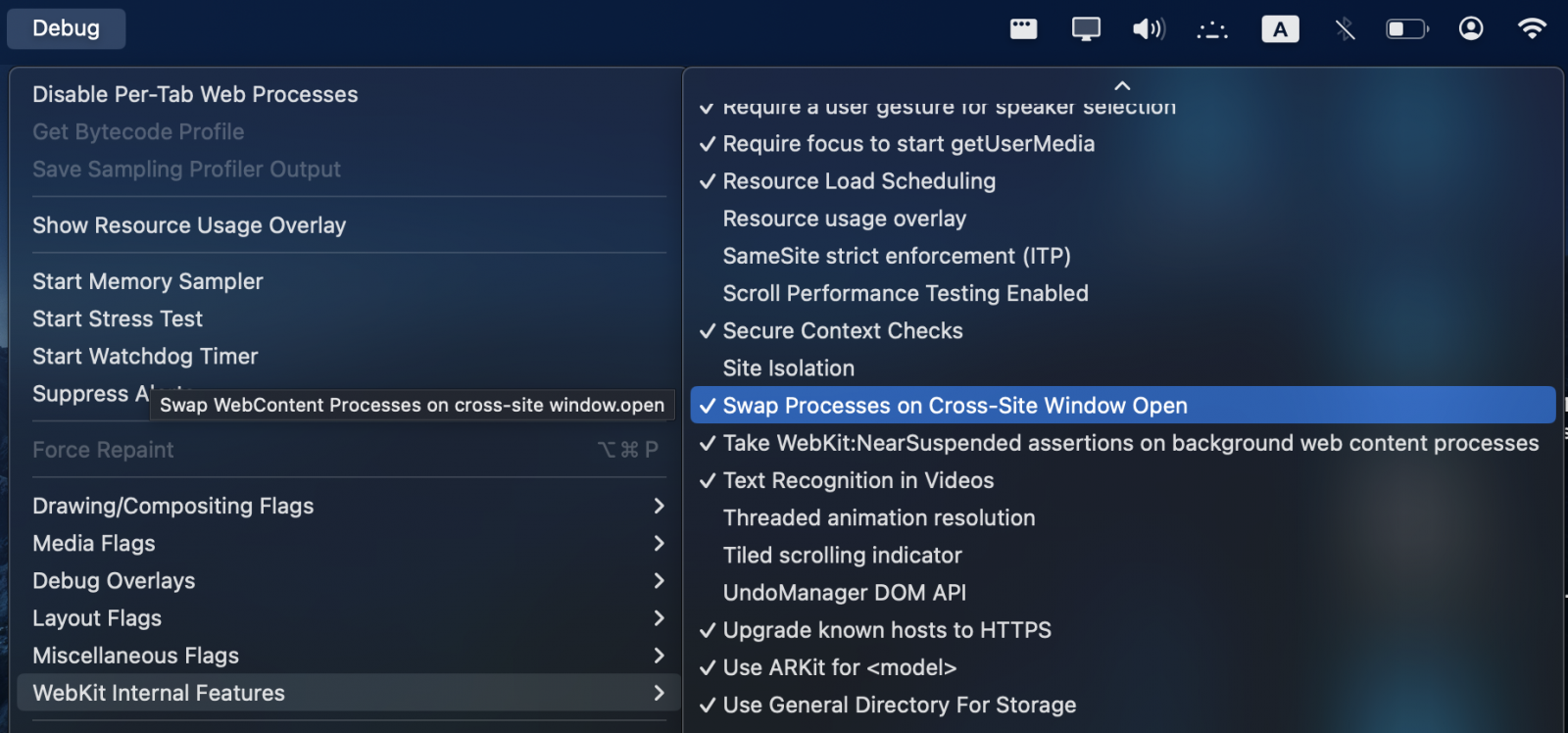
The mitigation comes with the warning that it might introduce some instability. If users want to disable it, they can do it from the debug menu by running in the terminal the command defaults write com.apple.Safari IncludeInternalDebugMenu 0.
Besides the actual implications of iLeakage, this research highlights the potential speculative execution risks in emerging ARM-based platforms that have not been scrutinized as heavily as x86 architectures.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.


