New Mirai Botnet Variant ‘V3G4’ Exploiting 13 Flaws to Target Linux and IoT Devices
A new variant of the notorious Mirai botnet has been found leveraging several security vulnerabilities to propagate itself to Linux and IoT devices.
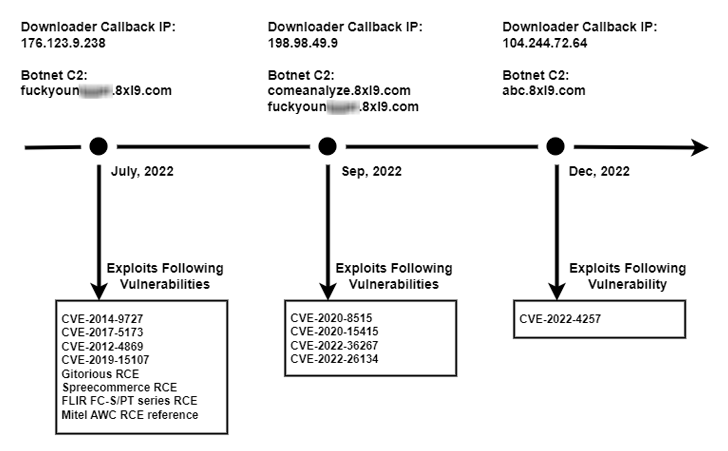
Observed during the second half of 2022, the new version has been dubbed V3G4 by Palo Alto Networks Unit 42, which identified three different campaigns likely conducted by the same threat actor.
“Once the vulnerable devices are compromised, they will be fully controlled by attackers and become a part of the botnet,” Unit 42 researchers said. “The threat actor has the capability to utilize those devices to conduct further attacks, such as distributed denial-of-service (DDoS) attacks.”
The attacks primarily single out exposed servers and networking devices running Linux, with the adversary weaponizing as many as 13 flaws that could lead to remote code execution (RCE).
Some of the notable flaws relate to critical flaws in Atlassian Confluence Server and Data Center, DrayTek Vigor routers, Airspan AirSpot, and Geutebruck IP cameras, among others. The oldest flaw in the list is CVE-2012-4869, an RCE bug in FreePBX.
Following a successful compromise, the botnet payload is retrieved from a remote server using the wget and cURL utilities.
The botnet, in addition to checking if it’s already running on the infected machine, also takes steps to terminate other competing botnets such as Mozi, Okami, and Yakuza.
V3G4 further packs a set of default or weak login credentials that it uses to carry out brute-force attacks through Telnet/SSH and proliferate to other machines.
It also establishes contact with a command-and-control server to await commands for launching DDoS attacks against targets via UDP, TCP, and HTTP protocols.
“The vulnerabilities mentioned above have less attack complexity than previously observed variants, but they maintain a critical security impact that can lead to remote code execution,” the researchers said.
To stave off such attacks, it’s recommended that users apply necessary patches and updates as and when they become applicable, and secure the devices with strong passwords.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on Patreon using the button below

To keep up to date follow us on the below channels.





![[FLOCKER] - Ransomware Victim: G*********************y[.]org 6 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)

