New Russian-linked CosmicEnergy malware targets industrial systems

Mandiant security researchers have discovered a new malware called CosmicEnergy designed to disrupt industrial systems and linked to Russian cybersecurity outfit Rostelecom-Solar (formerly Solar Security).
The malware specifically targets IEC-104-compliant remote terminal units (RTUs) commonly used in electric transmission and distribution operations across Europe, the Middle East, and Asia.
CosmicEnergy was discovered after a sample was uploaded to the VirusTotal malware analysis platform in December 2021 by someone with a Russian IP address.
Analysis of the leaked malware sample has revealed several noteworthy aspects regarding CosmicEnergy and its functionality.
First, the malware shares similarities with previous OT malware like Industroyer and Industroyer.V2, both used in attacks targeting Ukrainian energy providers in December 2016 and April 2022.
Additionally, it’s Python-based and uses open-source libraries for OT protocol implementation, just like other malware strains targeting industrial control systems, including IronGate, Triton, and Incontroller.
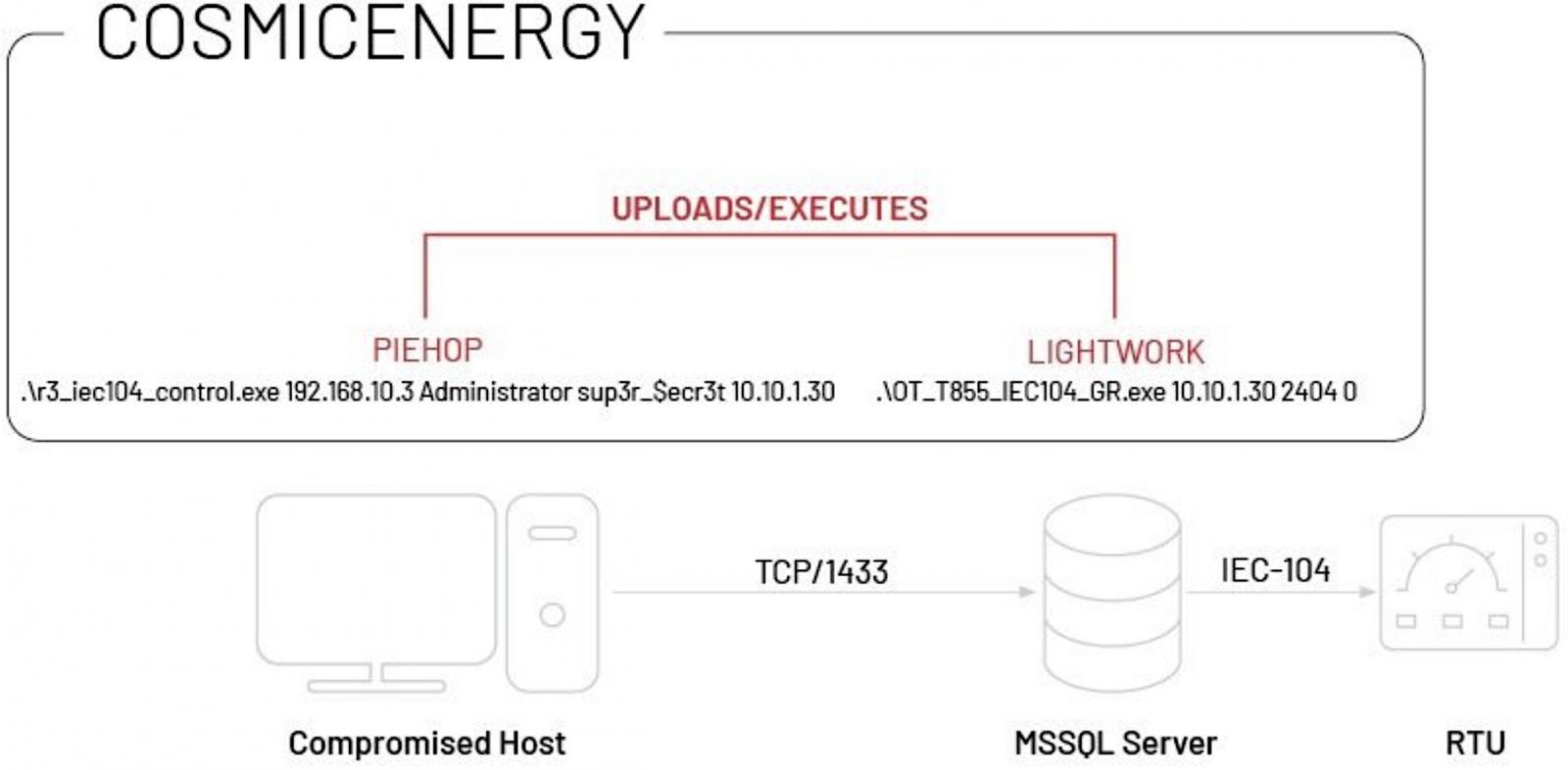
Just like Industroyer, CosmicEnergy likely gains access to the target’s OT systems via compromised MSSQL servers using the Piehop disruption tool.
Once inside the victims’ network, the attackers can control RTUs remotely by issuing IEC-104 “ON” or “OFF” commands via the Lightwork malicious tool.
Mandiant believes this newly discovered malware may have been developed as a red teaming tool designed to simulate disruption exercises by Russian cybersecurity company Rostelecom-Solar.
Based on public information showing that Rostelecom-Solar received funding from the Russian government for cybersecurity training and simulating electric power disruption, Mandiant suspects CosmicEnergy could also be used by Russian threat actors in disruptive cyberattacks targeting critical infrastructure like other red team tools.
“During our analysis of COSMICENERGY, we identified a comment in the code that indicated the sample uses a module associated with a project named ‘Solar Polygon.’ We searched for the unique string and identified a single match to a cyber range (aka polygon) developed by Rostelecom-Solar,” Mandiant said.
“Although we have not identified sufficient evidence to determine the origin or purpose of COSMICENERGY, we believe that the malware was possibly developed by either Rostelecom-Solar or an associated party to recreate real attack scenarios against energy grid assets,” Mandiant said.
“Given that threat actors use red team tools and public exploitation frameworks for targeted threat activity in the wild, we believe COSMICENERGY poses a plausible threat to affected electric grid assets.”
As Microsoft reported in April 2022, after Russia invaded Ukraine, Russian hacking groups have deployed many malware families (some of them never before seen in the wild) in destructive attacks against Ukrainian targets, including critical infrastructure.
The list includes but is not limited to WhisperGate/WhisperKill, FoxBlade (aka HermeticWiper), SonicVote (aka HermeticRansom), CaddyWiper, DesertBlade, Industroyer2, Lasainraw (aka IsaacWiper), and FiberLake (aka DoubleZero).
The Sandworm Russian military hackers used the Industroyer2 malware to target the ICS network of a prominent Ukrainian energy provider but failed to take down its high-voltage electrical substations and disrupt energy delivery across the country.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below


To keep up to date follow us on the below channels.





![[INCRANSOM] - Ransomware Victim: C B King Memorial School(branch) 9 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)



