Play ransomware attacks target Exchange servers with a new exploit that bypasses Microsofts ProxyNotShell mitigations
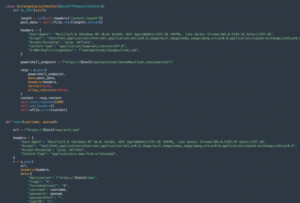
Play ransomware attacks target Exchange servers with a new exploit that bypasses Microsoft’s ProxyNotShell mitigations.Play ransomware operators target Exchange servers...




































![Cobalt Strike Beacon Detected - 39[.]106[.]152[.]200:443 43 Cobalt-Strike](https://www.redpacketsecurity.com/wp-content/uploads/2021/11/Cobalt-Strike-300x201.jpg)
