Malware Analysis – persistence – 172a3ab963d3e150845bd3b7d7047034
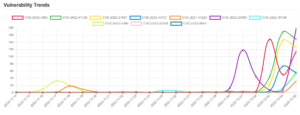
Score: 10 MALWARE FAMILY: persistenceTAGS:persistence, ransomwareMD5: 172a3ab963d3e150845bd3b7d7047034SHA1: c28b888ed5754ef5fa7876f1be66dd7675f54b76ANALYSIS DATE: 2022-12-03T11:40:51ZTTPS: T1060, T1112, T1004, T1491 ScoreMeaningExample10Known badA malware family was detected.8-9Likely...



![[TRYHACKME] - Void Execution Challenge 5 void_execution](https://www.redpacketsecurity.com/wp-content/uploads/2025/09/void_execution.png)


![[TRYHACKME] - Void Execution Challenge 8 void_execution](https://www.redpacketsecurity.com/wp-content/uploads/2025/09/void_execution-150x150.png)













![Cobalt Strike Beacon Detected - 20[.]74[.]209[.]192:8081 42 Cobalt-Strike](https://www.redpacketsecurity.com/wp-content/uploads/2021/11/Cobalt-Strike-300x201.jpg)
