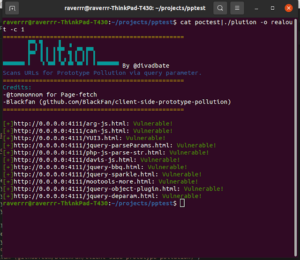
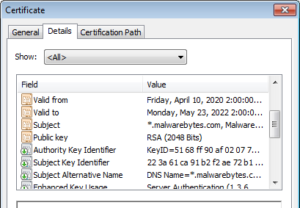
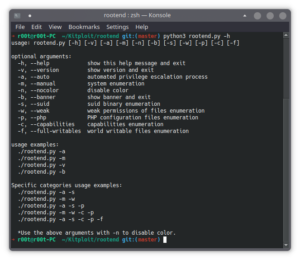
CVE-2021-40444 PoC – Malicious docx generator to exploit CVE-2021-40444 (Microsoft Office Word Remote Code Execution)
Malicious docx generator to exploit CVE-2021-40444 (Microsoft Office Word Remote Code Execution)Creation of this Script is based on some reverse...