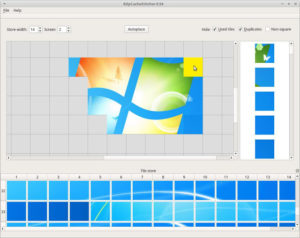
RdpCacheStitcher – RdpCacheStitcher Is A Tool That Supports Forensic Analysts In Reconstructing Useful Images Out Of RDP Cache Bitmaps
RdpCacheStitcher is a tool that supports forensic analysts in reconstructing useful images out of RDP cache bitmaps. Using raw RDP...


![[TRYHACKME] - Void Execution Challenge 1 void_execution](https://www.redpacketsecurity.com/wp-content/uploads/2025/09/void_execution.png)
![[TRYHACKME] - LondonBridge Full Walkthrough. 2 london-bridge](https://www.redpacketsecurity.com/wp-content/uploads/2025/09/london-bridge.png)



![[TRYHACKME] - Void Execution Challenge 8 void_execution](https://www.redpacketsecurity.com/wp-content/uploads/2025/09/void_execution-150x150.png)