Patch Tuesday – November 2020

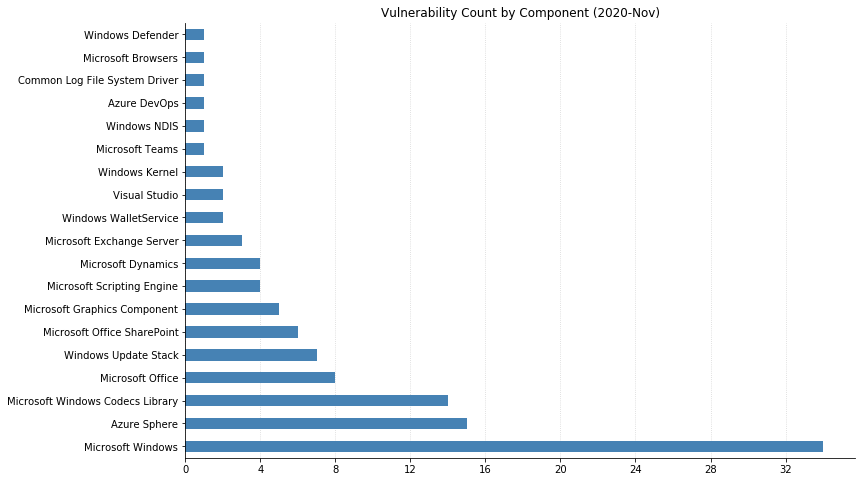
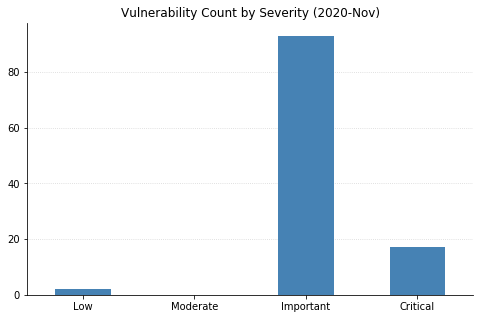
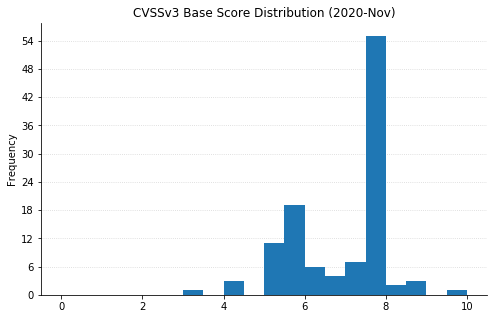
Jumping right back to a triple digit volume of vulnerabilities resolved, Microsoft covers 112 CVEs this November affecting products ranging from our standard Windows Operating Systems and Microsoft Office products to some new entries such as Azure Sphere.
Microsoft CVE-2020-17087: Windows Kernel Local Elevation of Privilege Vulnerability
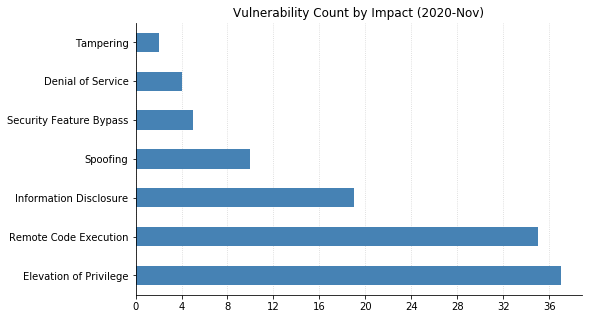
Coming as no surprise to anyone, the previously disclosed CVE-2020-17087 zero-day affecting all supported versions of Windows has a patch this month. It is with this same patch that over half of the additional vulnerabilities detailed this month can be remediated, so definitely have your patching cycles ready. CVE-2020-17087 is a buffer overflow vulnerability behind the Windows Kernel Cryptography Driver that gave local attackers the ability to escalate privileges. Luckily, as seen via Rapid7’s AttackerKB analysis “exploitability is at least somewhat more limited than it might appear at first glance.” This does not diminish the need to prioritize Operating System patching because of the next vulnerability up for discussion: CVE-2020-17051.
Microsoft CVE-2020-17051: Windows Network File System Remote Code Execution
CVE-2020-17051 is this month’s highest severity vulnerability sitting at CVSS 9.8. Microsoft describes CVE-2020-17051 as a Remote Code Execution vulnerability affecting Windows Network File System. At the time of writing, information regarding this vulnerability is light but Microsoft has noted that it has low attack complexity and does not require user interaction to exploit. This is aptly represented by the high CVSS score. At this point, this vulnerability is not known to be exploited in the wild.
Browser Vulnerabilities Come Back After An October Break
While it feels like it’s been a while, browser vulnerabilities are still a thing, and this month brought along five vulnerabilities affecting Internet Explorer and Edge browsers (EdgeHTML-based). CVE-2020-17048, CVE-2020-17052, CVE-2020-17053, CVE-2020-17054, and CVE-2020-17058 are all Remote Code Execution vulnerabilities potentially affecting Internet Explorer and/or Microsoft Edge (again, non-Chromium).
As a gentle reminder, Security-Only patches for operating systems that provide a Monthly Rollup or Security-Only update streams do not include browser remediations. Organizations opting for Security-Only patches should be aware that there are separate Cumulative Security Updates for Internet Explorer.
Azure Sphere
Something new and refreshing this month: A keen eye may have noticed 15 vulnerabilities pertaining to a new product category named Azure Sphere. So the question becomes…what needs to be done about them? The quick answer is, luckily, “not much”. Azure Sphere, an IoT Device offering, is updated automatically on a daily cadence when connected to a network. By the time you’re reading this, if you have Azure Sphere IoT devices in your environment (and they are connected to the Internet), these vulnerabilities would have already been resolved.
Note: Graph data is reflective of data presented by Microsoft’s CVRF at the time of writing.
If you like the site, please consider joining the telegram channel or supporting us on Patreon using the button below.



