Pre-installed auto installer threat found on Android mobile devices in Germany
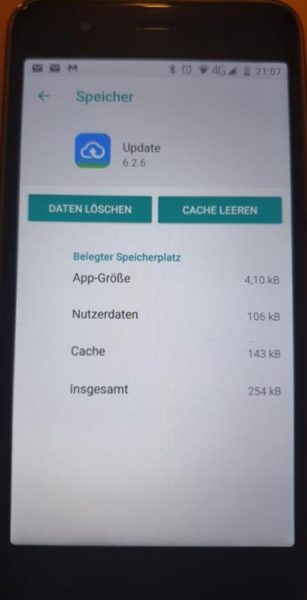
Users primarily located in Germany are experiencing malware that downloads and installs on their Gigaset mobile devices—right out of the box! The culprit installing these malware apps is the Update app, package name com.redstone.ota.ui, which is a pre-installed system app. This app is not only the mobile device’s system updater, but also an Auto Installer known as Android/PUP.Riskware.Autoins.Redstone.
Infected devices and other important notes
Although this issue seems to be primarily found on Gigaset mobile devices, we have also found other manufacturers involved. Here is a list of make/model/OS version of mobile devices found with Android/PUP.Riskware.Autoins.Redstone:
- Gigaset GS270; Android OS 8.1.0
- Gigaset GS160; Android OS 8.1.0
- Siemens GS270; Android OS 8.1.0
- Siemens GS160; Android OS 8.1.0
- Alps P40pro; Android OS 9.0
- Alps S20pro+; Android OS 10.0
We should note that the names Gigaset and Siemens have considerable overlap—Gigaset was formerly known as Siemens Home and Office Communications Devices. We listed both to erase any confusion.
It important to realize that every mobile device has some type of system update app. Unless you are experiencing the exact behaviors in the next section, you are most likely not infected. Another key point is that this pre-installed update app is the not the same as what is described in Android “System Update” malware steals photos, videos, GPS location. In that case, the malware is simply hiding as an update app, but is not a pre-installed system app.
Malware behavior
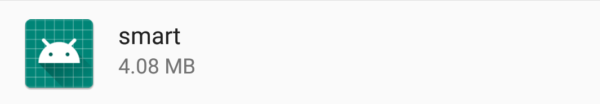
For most Gigaset users experiencing this infection, com.redstone.ota.ui installs three versions of Android/Trojan.Downloader.Agent.WAGD. The package name of this malware always starts with “com.wagd.” and is followed by the name of the app. Here are some examples:
- Package name: com.wagd.gem
- App name: gem

- Package name: com.wagd.smarter
- App name: smart

- Package name: com.wagd.xiaoan
- App name: xiaoan
According to forum users and analysis, Android/Trojan.Downloader.Agent.WAGD is capable of sending malicious messages via WhatsApp, opening new tabs in the default web browser to game websites, downloading more malicious apps, and possibly other malicious behaviors. The malicious WhatsApp messages are most likely in order to further spread the infection to other mobile devices.
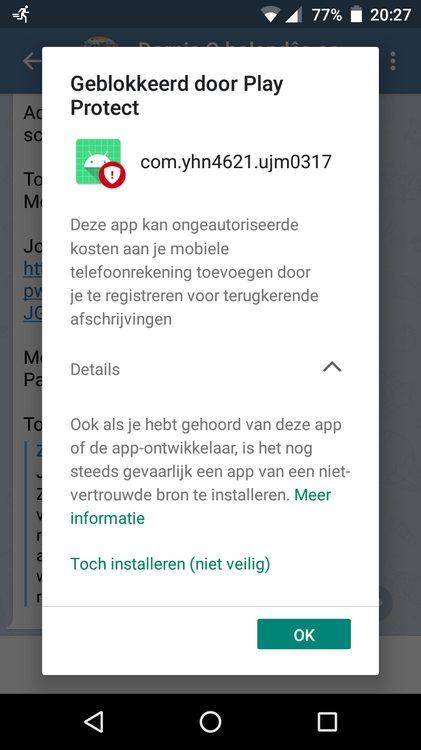
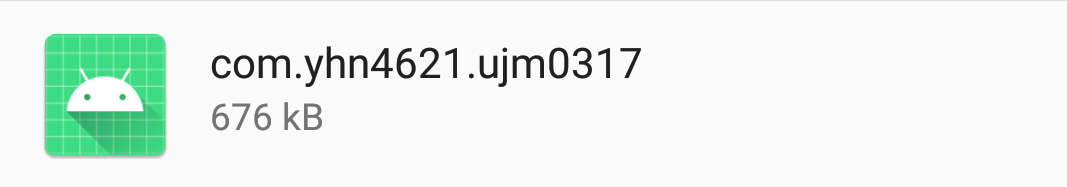
In addition, some users also experience Android/Trojan.SMS.Agent.YHN4 on their mobile devices. The downloading and installation of this SMS Agent is due to Android/Trojan.Downloader.Agent.WAGD visiting gaming websites containing malicious apps. Thereupon, the mobile device contains malware capable of sending malicious SMS messages. Like with the malicious WhatsApp messages, it can in addition send malicious SMS messages to further spread the infection.
Awaiting resolution
Because com.redstone.ota.ui is a system app, you cannot remove it using traditional methods. Further, past evidence from Adups and other variants shows that disabling pre-installed update apps is either impossible or it re-enables shortly after disabling. Therefore, just as the case with UMX back in January 2020, it is up to the device manufacturer to push an update to truly fix this issue. Keep in mind that even after the manufacturer fixes the issue, they can push out yet another update in the future to re-infect. There is some evidence that this has been the case with UMX as of recent, but that is another blog for another day.
In the case of Gigaset, German blogger Günter Born on his blog Borncity has already gotten the ball rolling by contacting Gigaset to resolve. In the meantime, according to an Attention pinned at the bottom of Mr. Born’s blog he suggests the following (translating from German to English using Google Translator):
Attention: I recommend all Gigaset Android device owners to heed the information in the blog post Malware attack: What Gigaset Android device owners should do now and to lay the device dead. At least until Gigaset has responded and the process has been completely clarified.
A safe workaround
The aforementioned recommendation to quote, lay the device dead, may not be an option for some users if this is their only mobile device. Allow me to suggest another option that still gives users the ability to use their Gigaset mobile device safely.
Yes, it is true you cannot remove it using traditional methods, but we have a workaround!
We can use the method below to uninstall Update (com.redstone.ota.ui) for current users (details in link below):
https://forums.malwarebytes.com/topic/216616-removal-instructions-for-adups/
From the tutorial above, use this command during step 7 under Uninstalling Adups via ADB command line to remove:
adb shell pm uninstall -k –user 0 com.redstone.ota.ui
At this point, run a Malwarebytes for Android scan to remove any remaining malware apps.
Checking for updates
Here is the kicker. Remember that the Update app is also the mobile device’s only way to update the system. Thus, if and when Gigaset comes up with a resolution, you will need to check for system updates by re-installing Update.
You can re-install using this command:
adb shell pm install -r –user 0 <full path of the apk>
The two full path of the apk’s we have seen so far are as follows:
/system/priv-app/ThirdPartyRSOTA/ThirdPartyRSOTA.apk
/system/app/Rsota/Rsota.apk
If neither of these paths work, you can find the correct path, even after uninstalling for current user, by running this command:
adb shell pm list packages -f -u
Copy/paste the output into a text editor (like Notpad) and search for com.redstone.ota.ui to find the correct path.
If there are no updates to install or if the update that does install does not resolve the issue, remember to once again uninstall Update for the current user.
Never ending battle
Assisting customers with resolving pre-installed malware is a reoccurring action by me and our mobile support staff. Fortunately, in the case of Gigaset users, there is a workable resolution. If you are experiencing similar or other mobile malware issues you can reach us on our Malwarebytes Forum or for more thorough support submit a support ticket. As always, stay safe out there!
The post Pre-installed auto installer threat found on Android mobile devices in Germany appeared first on Malwarebytes Labs.
If you like the site, please consider joining the telegram channel or supporting us on Patreon using the button below.



![[QILIN] - Ransomware Victim: www[.]nuphoton[.]com 9 image](https://www.redpacketsecurity.com/wp-content/uploads/2024/09/image-300x300.png)