Ransomware in December 2022
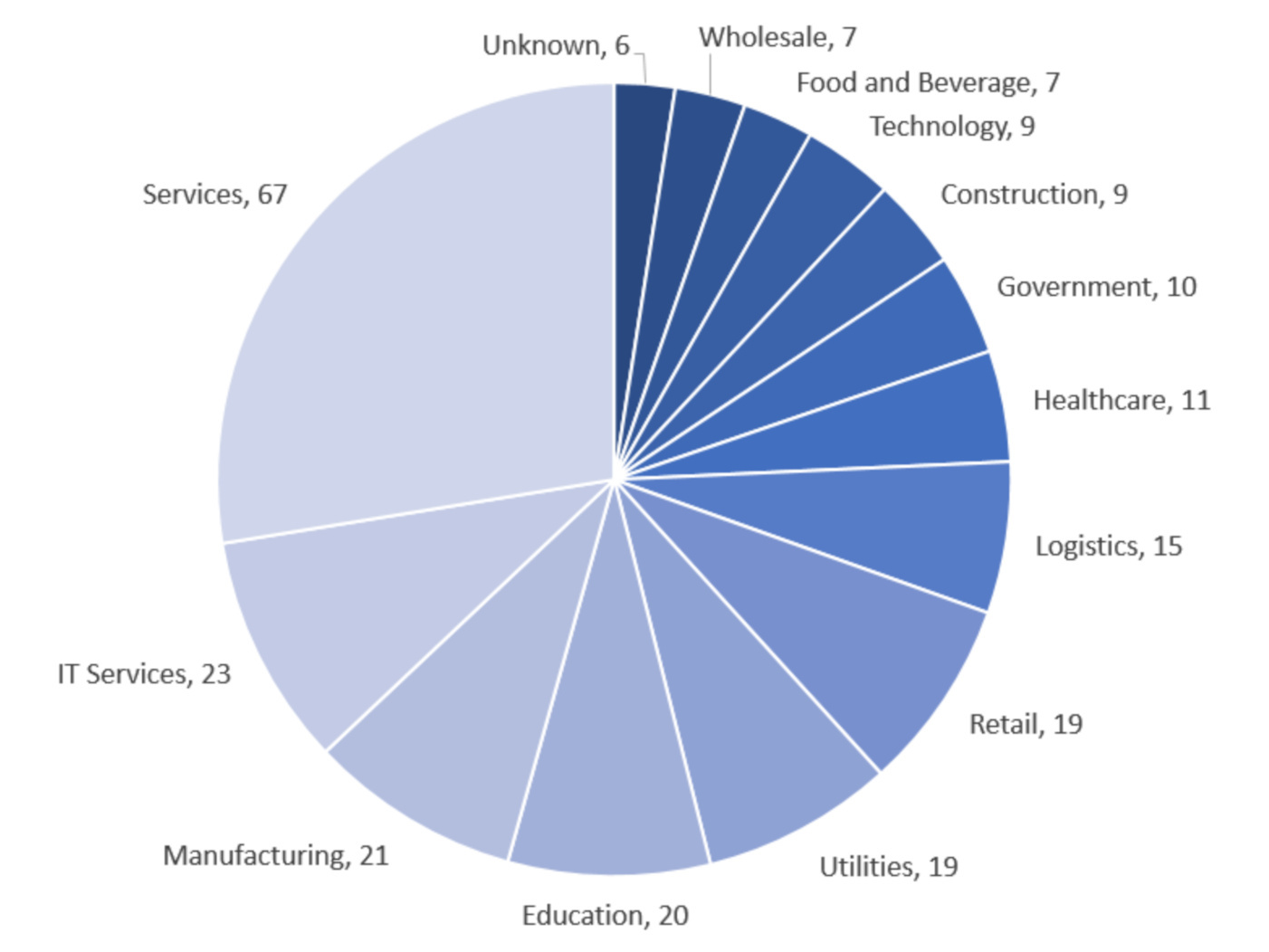
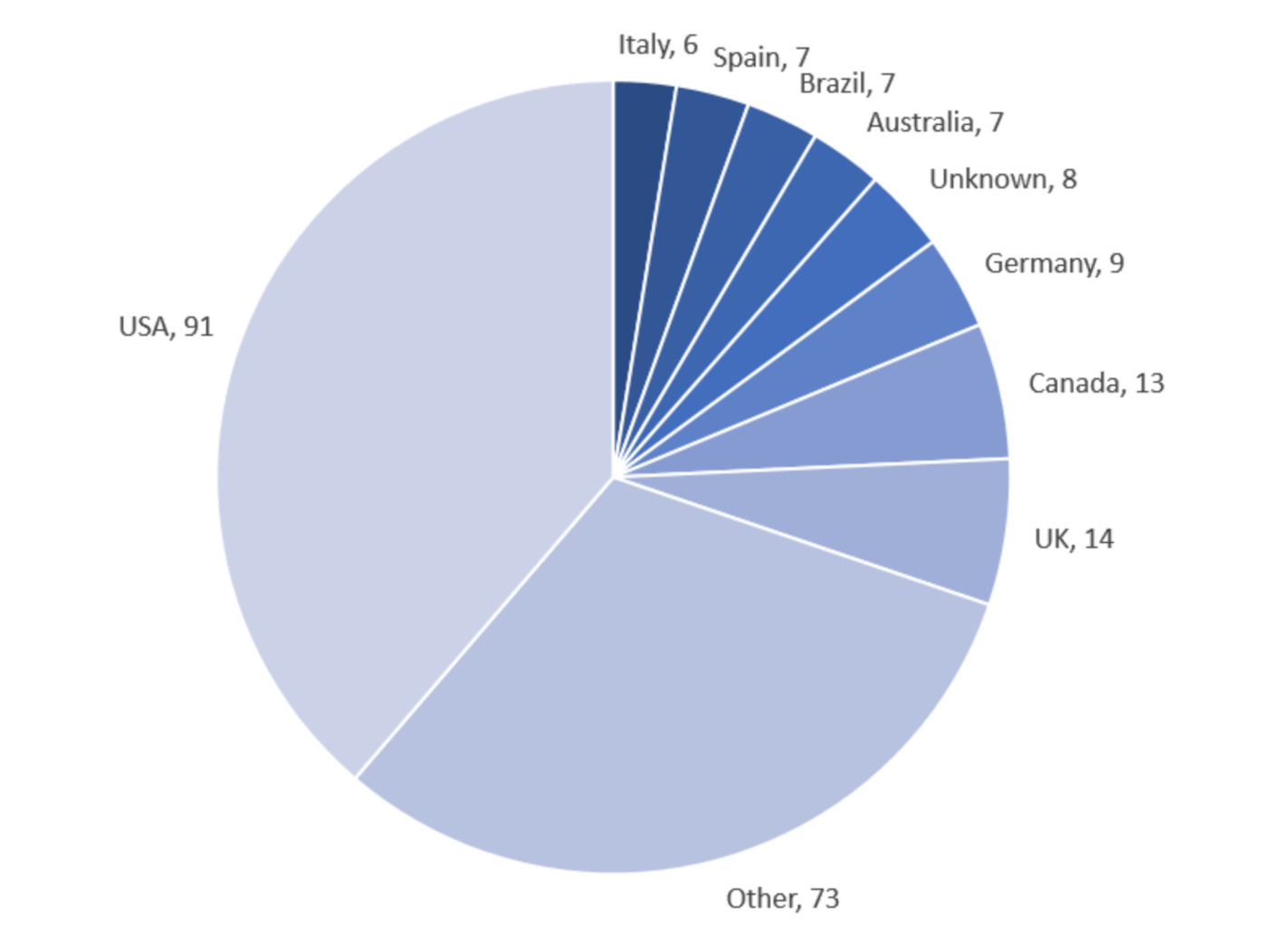
Malwarebytes Threat Intelligence builds a monthly picture of ransomware activity by monitoring the information published by ransomware gangs on their dark web leak sites. This information represents victims who were successfully attacked but opted not to pay a ransom.
Lockbit has rebounded from its unusual fall from grace in November, snatching the title of the month’s worst ransomware, back from Royal. Royal has meanwhile still shown itself as a force to be reckoned with, ranking third in number of attacks for December.
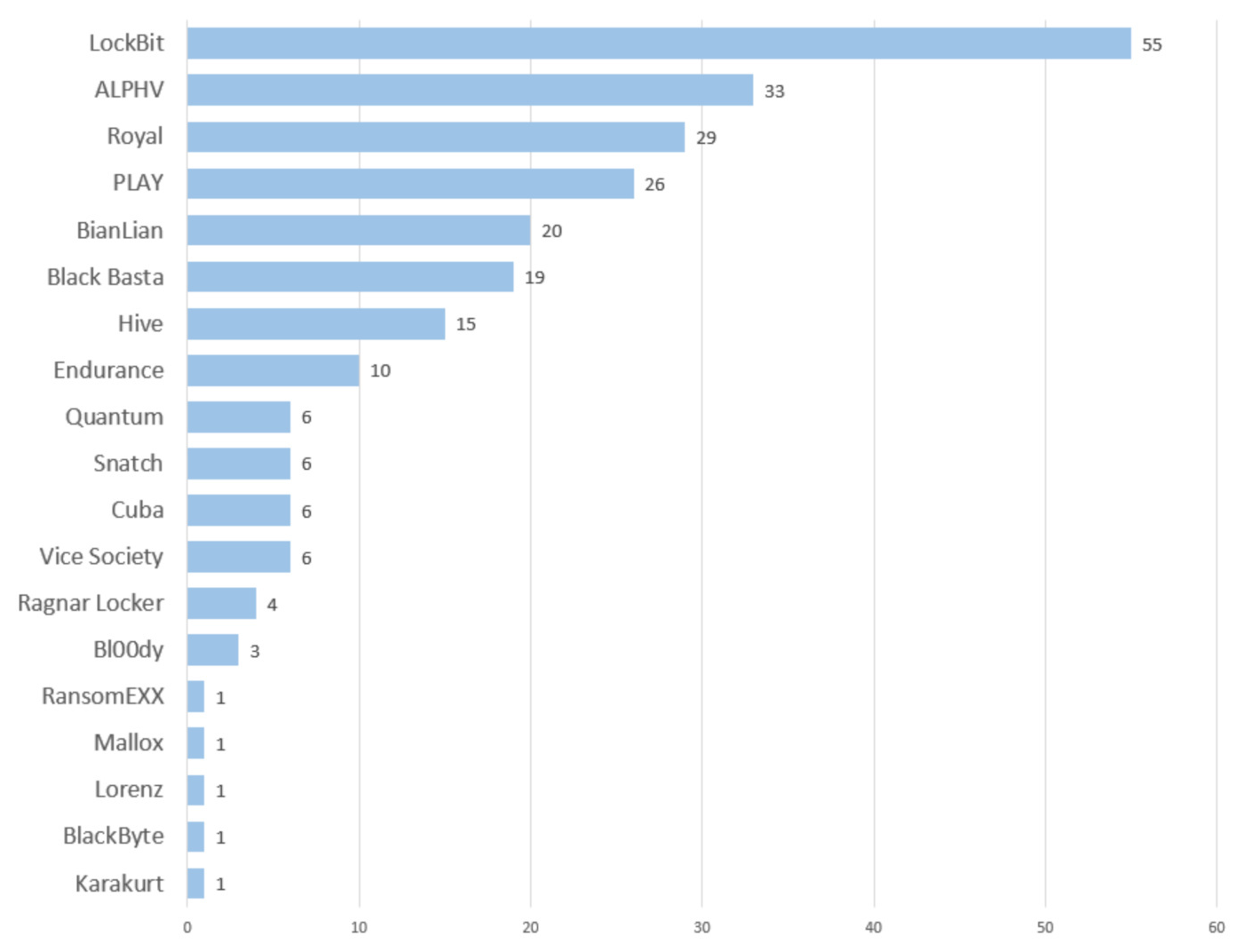
Attacks by Royal may be down 35 percent from their high of 49 in November, but at the same time, there’s good reason to suspect that their attacks are becoming more targeted.
On December 07, 2022, the Health Sector Cybersecurity Coordination Center (HC3)—an arm of the US Department of Health and Human Services (HHS)—released a threat brief about Royal after observing the group disproportionately targeting the healthcare industry. Their crowning attack for December came late in the month when they breached telecommunications company Intrado.
In terms of progress, the two newcomers that we introduced last month, Play and Project Relic, have vastly different stories to tell.
Project Relic has fallen off the map while Play has turned up the jets—we recorded a whopping 136 percent increase in attacks from the gang compared to November. Since our last update Play has been seen leveraging a never-before-seen exploit chain, which might be responsible for their sharp uptick in attacks. The new Microsoft Exchange attack, dubbed ‘OWASSRF’, chains exploits for CVE-2022-41082 and CVE-2022-41080 to gain initial access to corporate networks. This was the technique behind a ransomware attack on cloud computing service provider Rackspace in early December, which Play later claimed responsibility for.
Play’s surge in activity, however, was hardly an anomaly for December. Month-on-month we saw hefty percentage-point increases in attacks across the board.
ALPHV (aka BlackCat), for example, is a ransomware gang that has consistently topped the charts in our ransomware reviews; the number of their attacks in December (33), however, is not only a 70 percent increase from November but also the highest it’s been all 2022. We also saw 25 percent and 116 percent increases from BianLian and BlackBasta, respectively. These upticks are perhaps to be expected, given that attackers famously love the holiday seasons due to the reduction in security staff on deck. Only time will tell if ransomware gangs will sustain their heightened levels of activity into the New Year—or if the increase is indeed simply a gift-wrapped aberration.
Lockbit… apologizes?
Lockbit in December regained the throne as the biggest ransomware gang by attack volume, reversing a three-month downward trend in number of victims.
The prolific ransomware group claimed on December 12 to have stolen up to 75GB of confidential data from California’s Department of Finance, or over 246,000 files in more than 114,000 folders. Not even SickKids (a hospital for sick children) was spared from LockBit’s avarice in December. A ransomware attack using LockBit impacted the hospital’s internal and corporate systems, hospital phone lines, and website.
While we’re not surprised to see a gang stoop to such lows, we don’t find many issuing apologies after the fact. Two days later LockBit apologized for the attack, which it blamed on a rogue affiliate, and released a decryptor for free.
LockBit’s operation’s policy states “It is forbidden to encrypt institutions where damage to the files could lead to death, such as cardiology centers, neurosurgical departments, maternity hospitals and the like, that is, those institutions where surgical procedures on high-tech equipment using computers may be performed.”
Of course the apology doesn’t turn LockBit in to some kind of Robin Hood. Its business model is to inflict so much harm that people are willing to pay a fortune to make it stop.
New ransomware gangs
Unsafe
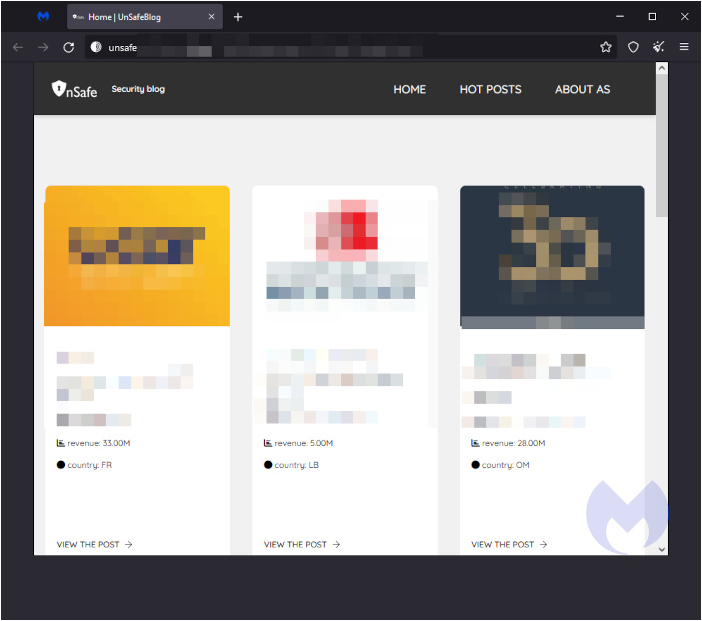
In December, we saw a group emerge that makes its cash by riding on the coattails of real ransomware gangs.
The new player, Unsafe, seems to recycle leaks from other ransomware groups. Unsafe provides security blogs for cybercriminals to post victims and leaked data as well as consultation services for a fee. It currently lists eight victims.
Endurance
We call them ransomware gangs for a reason: These are groups of cybercriminals working together in a hierarchical organization. Rarely do we ever see lone wolf attacks, and if we do it’s even more unusual for them to make as big of a splash in so short of a time as Endurance has.
This cybercriminal, known on dark web forums as IntelBroker, tends to make individual posts about data on sale.
In less than 30 days since its inception, Endurance appears to have successfully infiltrated some big corporations and breached several US government entities. After posting some high-value victims, Endurance has removed them from its dark web site, which is “undergoing development”.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on Patreon using the button below

To keep up to date follow us on the below channels.






