Recon Simplified with Spyse
One of the major struggles in bug bounty hunting is to collect and analyze data during reconnaissance, especially when there are a lot of tools around but very few that offer actually useful results. The job of eliminating false positives and unrelated data from your recon becomes harder as the size of your target increases.
Most popular tools used by bug bounty hunters like Knockpy, Sublist3r, and Subfinder are command line based and often difficult to use when the size of the target becomes bigger. With a lot of results provided, it becomes harder and longer to filter out the most important ones, remove unnecessary results, and pick the right investigation vector. However, some companies are still trying to simplify the recon process by rethinking old approaches and implementing UI/UX, and technical features.
Spyse is that reconnaissance automation framework that every bug bounty hunter should test at least once.
Reconnaissance process
At the core of reconnaissance is OSINT and data analysis, one needs to analyze a target and map out its infrastructure efficiently.
To become familiar with your target’s attack surface, you need to perform recon in a proper manner and gather information about its assets. For that, it’s crucial to enumerate all the assets belonging to the investigated target (domains, sub-domains, IP address, etc) and related assets, basically everything that is closely connected to the main target.
By doing it precisely, anyone can easily spot the low hanging fruits such as sub-domain takeovers that can have a huge impact.
Spyse is the tool that simplifies this process and makes your routine work easier by storing all needed information in one place and pointing where to look first.
Faster Reconnaissance
Be the fastest in reaching your target’s assets. Bug Bounty Hunting is a rat race – the faster you are able to fully analyze your target’s attack surface, the more the chances of scoring a bounty. There is competition in every field, but with close to a million bug bounty hunters working across platforms – at any given time there may be hundreds of thousands of bug bounty hunters working on a specific target of a bug bounty program, which leads us to the biggest hurdle – time.
If you are not able to optimize your reconnaissance workflow and reduce the time you spend on your targets, you will lag behind the others. If you are at par with the others, and stick to the usual tools, you still stay average – but with an industry-leading solution like Spyse, you not just become fast but faster than the others.
With Spyse, it’s just a plug-and-play operation. It has all the necessary data about your targets already collected, even before you begin to hunt on a target, and the advanced search filter mechanism is way better than most command-line based open source tools..
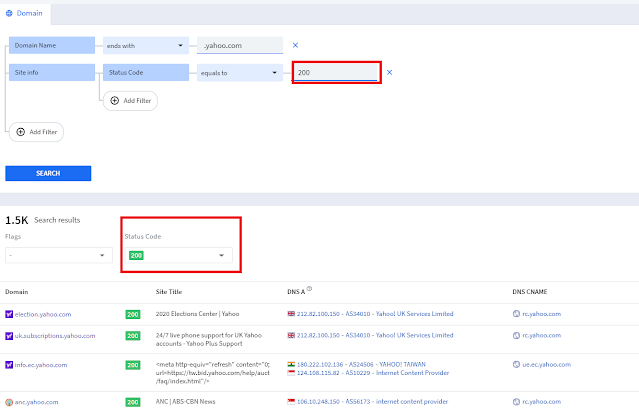
Doing Recon on New Targets has never been easier
If you run the traditional tools just after you get access to a new target, it might take days to just collect the data on larger targets and, yet more time to analyze and make sense of it. Spyse’s advanced search feature can get you to the same results in less than a fraction of a second.
You can search for information about your target domain name (say, Target.com), from Spyse’s collection of over 4.5B domain name records, all indexed.
 |
| Search your target in over 25TB database. |
Not just another Cybersecurity Search Engine
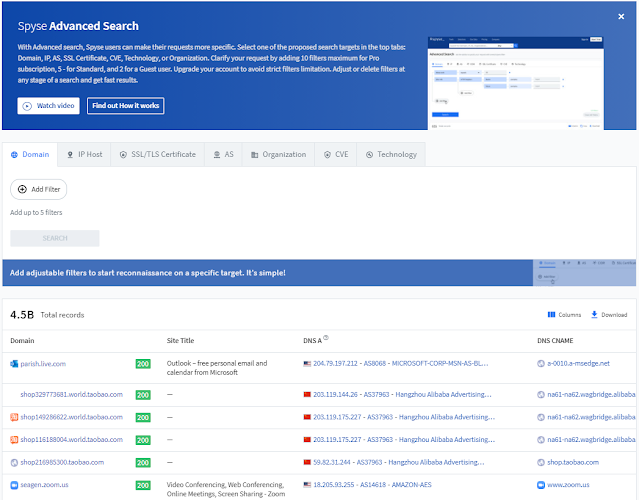
Spyse is not just another cybersecurity search engine, it’s an advanced yet simple Reconnaissance framework of sorts. Unlike Censys and Shodan, Spyse offers a user friendly filter which doesn’t make use of advanced query syntax, dorks, etc.
Spyse’s advanced search feature is aimed to be simple to use, user friendly yet efficient and precise. The advanced search lets you hit your goal by tuning the search parameters to exactly the targets you are after – minimizing false positives and inaccurate results.
 |
| Advanced Search Filter to find Apache servers belonging to a target |
For example, if you are looking for Apache servers in a particular target’s infrastructure, you can set the search filters to match your target’s Organization name (domain name or, AS or, IP ranges) and add another filter, Site info > HTTP Header > Name and Value to Server and Apache respectively, and let the backend handle the rest for you.
The Database
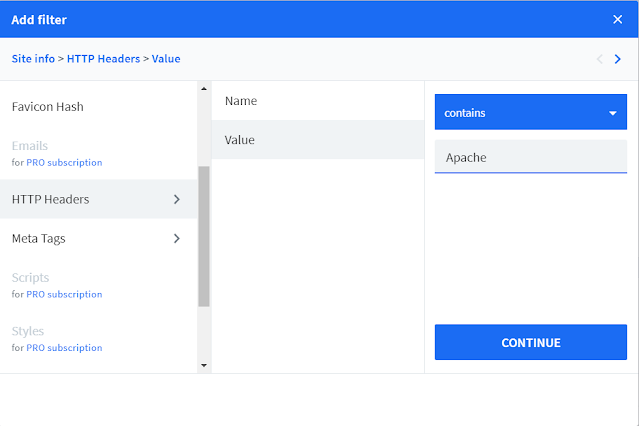
 |
| Spyse has collected and indexed over 4.5B domains |
Spyse has gathered data of over 217.1M hosts with open ports, indexed 4.5B domains, 66M SSL/TLS certificates, 371M email-related data, 143.7K vulnerabilities, 1.2M organizations and more. Learn more about their data statistics here.
Having to deal with so much data on large scope bug bounty targets during recon makes it incredibly difficult and tedious to scan these assets, and perform reconnaissance at scale. However, Spyse collects and updates this data on a regular basis, and indexes it, making it easier to filter out small bits of information that are important for your recon.
The whole database updates once a week except for some types of data that do not change too often, like domains.
Managing Recon Data
Spyse has taken care of it. It is difficult to manage vast amounts of gathered information. Some hunters who have advanced development knowledge prefer to make their own automation with a proper backend and database of targets, yet they tend to miss out on lots of data and find it hard to manage, & correlate it.
However, with Spyse you don’t need advanced development skills, because it crawls, collects and connects all the data about your targets.
Developing a web application to manage the whole process might be beneficial but it will cost you lots of work. Nevertheless, you have Spyse that can be implemented with other tools simply through the API connection. This should save the time you would have otherwise spent running only manual command line tools.
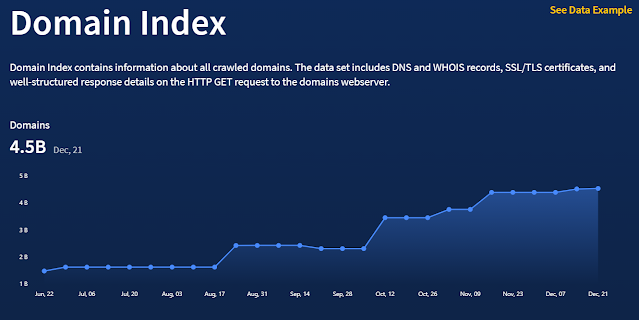
Filtering subdomains by Response Code
You can also filter your target’s assets by response code (for example – 200 status code, for valid request), which helps you quickly find interesting assets from a large number of target subdomains and domains. This is a very handy feature while doing recon on any target, as it gives you a quick overview of the publicly accessible assets of your target.
 |
| Browsing targets by status code (for example, 200 status code) |
Export Recon Data in JSON/CSV Format
Spyse has a very handy data export feature that lets you quickly export your scan data in JSON and CSV format. Whether you like to see your data in Excel or, implement it in your own application or, visualize it using ElasticSearch, Spyse has got you covered. It also makes it easier for you to use the exported data with other custom tools (most tools support JSON/CSV data, as its a common format).
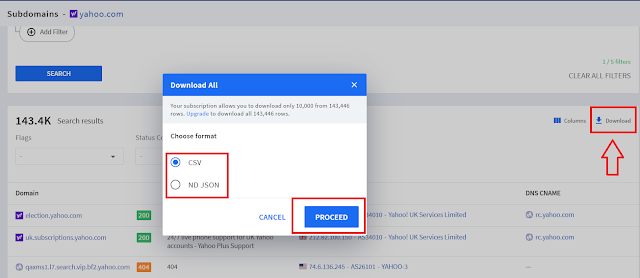 |
| Export reconnaissance data in multiple formats – JSON or, CSV |
Large Scope
Spyse can easily handle a lot of information. With conventional tools, you can miss a lot of information while working on large targets but with Spyse – it’s no longer a problem!
Spyse not just gathered an incredibly large dataset of assets, It structured all of them in an understandable and intuitive way with loads of conclusions that indicate vulnerable or just interesting parts of the target.
Find out how everything is connected:
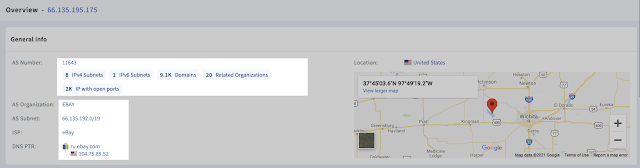 |
| Spyse IP data output |
Easily locate related data:
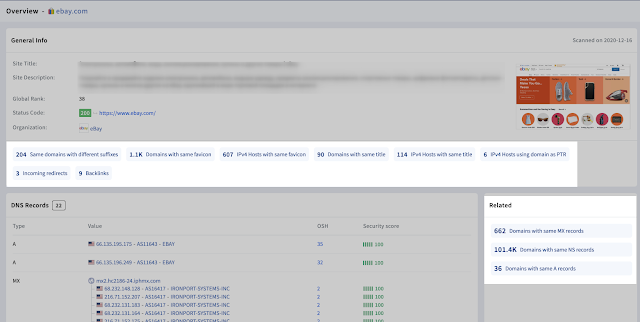 |
| Spyse related data |
Understand vulnerability level of the target and explore found vulnerabilities:
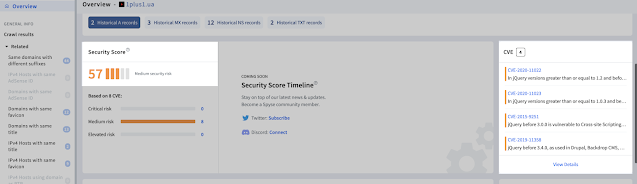 |
| Instant Vulnerability assessment of the target |
Benefit from ready made conclusion based on data analysis:
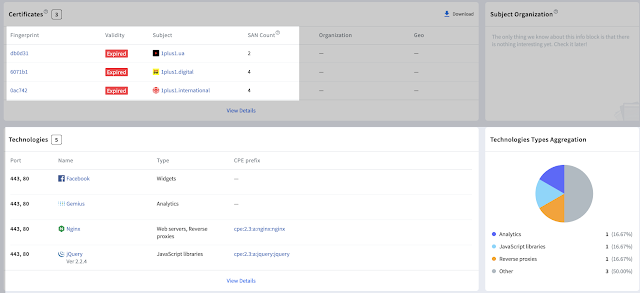 |
| Ready-made conclusions made by Spyse |
Data Visualization
The web interface lets you visualize your target’s data more efficiently and in a better manner than other tools. This helps you take decisions easily, and find vulnerable assets more easily than using conventional tools. With bigger targets like Yahoo having as many as 143.4k sub-domains, using conventional tools like subfinder becomes harder, but with Spyse you can visualize the relationships between different assets, and decide where to spend your time while hunting on the target’s assets.
Spyse’s advanced data gathering solution gives you an extremely intuitive interface to search through loads of data and offers you a visual approach to dealing with large amounts of recon information.
All Around Solution for OSINT Data Analysis (Conclusion)
Instead of moving back and forth between different tools that give inaccurate data, using the stunning UI makes it easier to wade through a sea of OSINT data. Use it for quick target overview alone or in combination with other tools and remove all unnecessary amnual work.
In conclusion, explore a wide variety of Spyse’s tools that will help you to find exact piece of information.
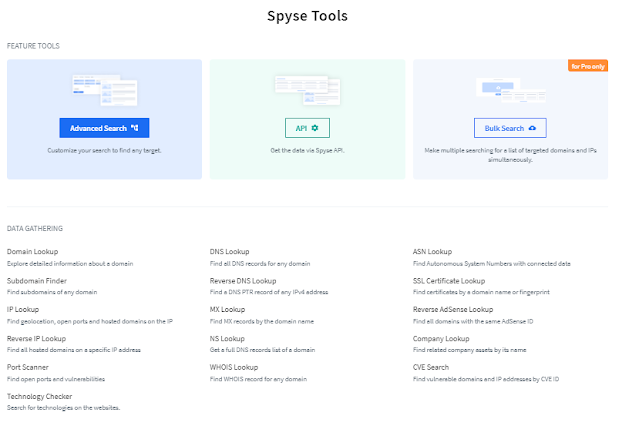
Most necessary tools:
- Subdomain Finder – Finding sub-domains on large targets is now way easier with their advanced sub-domain finder tool.
- Reverse IP Lookup – Add more assets to your target’s scope with the advanced Reverse IP look up tool, and find vulnerable hosts using Reverse IP Lookups.
- Port Scanner – Look for open ports on your targets with the advanced port scanner tool, and filter through IP addresses of targets based on open ports.
- ASN Lookup – To look up ASNs of your bug bounty targets.
- Company Lookup – Makes it easy to collect data about the acquisitions of your target company, and gives you access to more scope while hunting.
If you like the site, please consider joining the telegram channel or supporting us on Patreon using the button below.



