Shadow PC warns of data breach as hacker tries to sell gamers’ info

Shadow PC, a provider of high-end cloud computing services, is warning customers of a data breach that exposed customers’ private information, as a threat actor claims to be selling the stolen data for over 500,000 customers.
Shadow (Shadow) is a cloud gaming service providing users with high-end Windows PCs streamed to their local devices (PCs, laptops, smartphones, tablets, smart TVs), allowing them to run demanding AAA games on a virtual computer.
According to multiple tips sent to BleepingComputer yesterday from Shadow customers, the company has begun sending data breach notifications following a successful social engineering attack targeting its employees.
“At the end of September, we were the victim of a social engineering attack targeting one of our employees,” reads the notice.
“This highly sophisticated attack began on the Discord platform with the downloading of malware under cover of a game on the Steam platform, proposed by an acquaintance of our employee, himself a victim of the same attack.”
Based on the description of the attack, the downloaded malware was an info-stealer that successfully stole an authentication cookie that allowed the hackers to log in to the management interface of one of the company’s SaaS (software-as-a-service) providers.
Leveraging this access, the attacker abused the API to extract customers’ full names, email addresses, dates of birth, billing addresses, and credit card expiration dates.
Shadow’s notice clarifies that the incident has not resulted in the exposure of account passwords or other sensitive payment/banking data.
Shadow says that it has revoked the stolen authentication cookie and that the hacker’s access to its systems has been blocked. Moreover, Shadow has implemented additional defenses to prevent similar incidents from occurring in the future.
The firm assures the impacted customers that the compromised service provider did not hold any other user data beyond what is highlighted in the notice.
However, impacted individuals are urged to remain vigilant for phishing and scamming attempts and activate multi-factor authentication (MFA) on all their accounts.
Limited additional information on the incident can be found on this Reddit discussion joined by an employee of the firm. However, no official statements on the incident have been posted on the official website or social media channels.
BleepingComputer contacted Shadow with questions regarding the incident, and we will update this post with their statement.
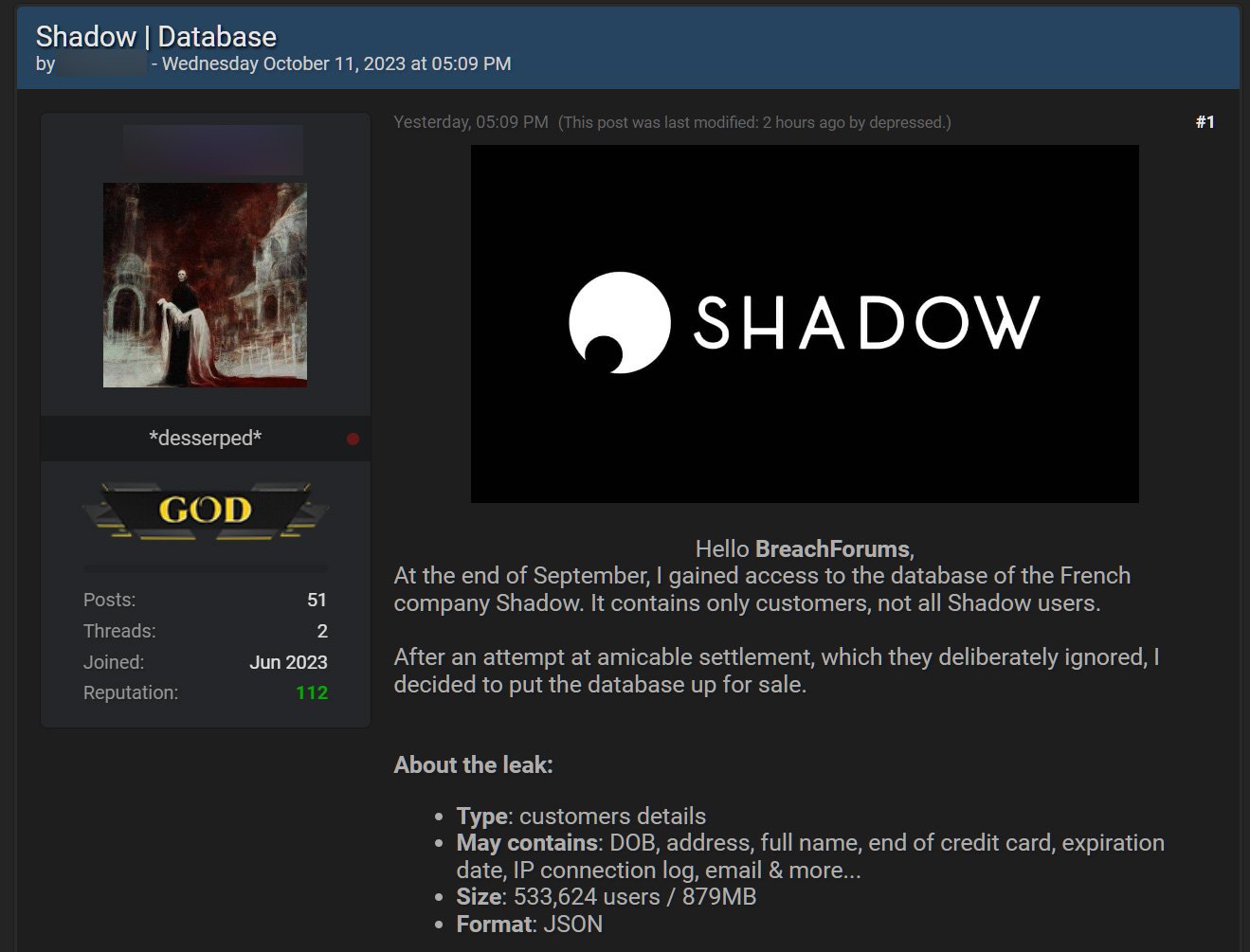
Shadow database sold on a hacker forum
Last night, a threat actor claimed to be responsible for the attack and is selling the stolen database on a well-known hacking forum.
The threat actor claims that they breached Shadow at the end of September and were able to steal the data for 533,624 users.
“At the end of September, I gained access to the database of the French company Shadow. It contains only customers, not all Shadow users,” reads the for sale post.
“After an attempt at amicable settlement, which they deliberately ignored, I decided to put the database up for sale.”
Source: BleepingComputer
The threat actor also says IP connection logs were stolen in the breach in addition to the other data already confirmed by Shadow.
BleepingComputer has not independently confirmed if the sold data belongs to Shadow customers.
A considerable amount of time and effort goes into maintaining this website, creating backend automation and creating new features and content for you to make actionable intelligence decisions. Everyone that supports the site helps enable new functionality.
If you like the site, please support us on “Patreon” or “Buy Me A Coffee” using the buttons below
To keep up to date follow us on the below channels.

![GoPhish Login Page Detected - 213[.]157[.]205[.]230:443 5 gophish](https://www.redpacketsecurity.com/wp-content/uploads/2024/04/gophish-300x90.png)
