WebNavigator Chromium browser published by search hijackers
A mystery Chromium browser recently made a sudden appearance, and is certainly proving popular. But what is it, and where did it come from?
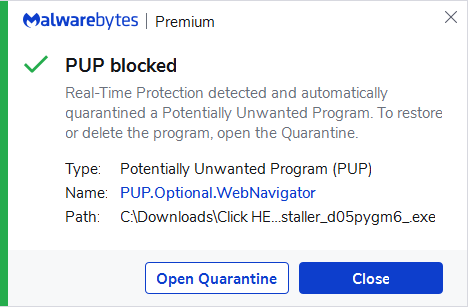
Malwarebytes detects the browser as PUP.Optional.WebNavigator, and we found several clues that this browser was brought to you by a notorious family of search hijackers.
That family isn’t new to us—we reported about them before when they changed a Chrome policy to remote administration, and lied about the permissions they asked of their users.
Search hijackers in general
We have written before about the interests of shady developers in the billion-dollar search industry and reported on the different tactics these developers resort to in order to get users to install their extensions or use their search sites.
Every time someone clicks on a sponsored advertisement, the requisite search engine earns money on a pay-per-click basis. They are paid by advertisers, who shell out for beneficial placement in the search results for keyword phrases of their choice.
As a result of the popularity of these search engines—Google in particular—US companies spend an estimated $80 billion on search engine optimization (SEO) alone. And the leading search engines are owned by some of the most valuable technology companies around.
What is WebNavigator?
The WebNavigator Browser is a Chromium-based web-browser that promises to simplify your browsing experience.
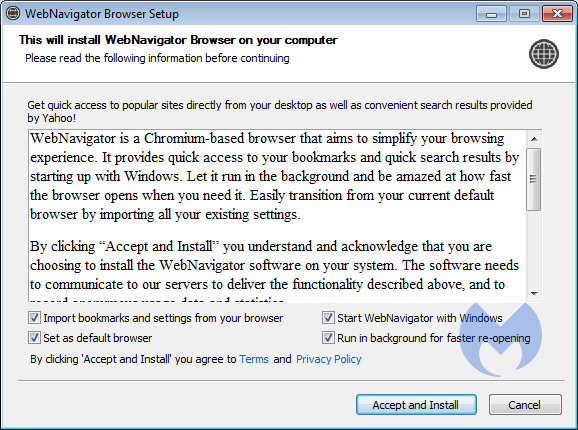
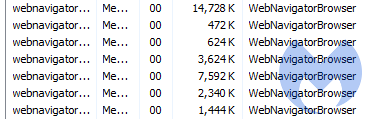
The simplification is done by keeping the browser running in the background. I fail to see the advantage of that method over minimizing your normal browser, but at least the authors made an effort to explain why the process remains running even after you closed the browser.
Another checkbox that is ticked by default is the “Set as default browser” which is pretty cheeky.
Where do people find WebNavigator?
The websites that promote the WebNavigator browser show up in advertisements and get visitors from redirectors. I found them when I was searching for new variants of the family of search hijackers that have become my “special friends” over the past years. That was my first clue that they might be related.
But using the same advertising networks is no definite proof whatsoever. As many shady website owners, they switch domains a lot so they don’t end up on every blocklist. Another detail they have in common.
What was your second clue?
The second clue was the layout and makeup of their website.
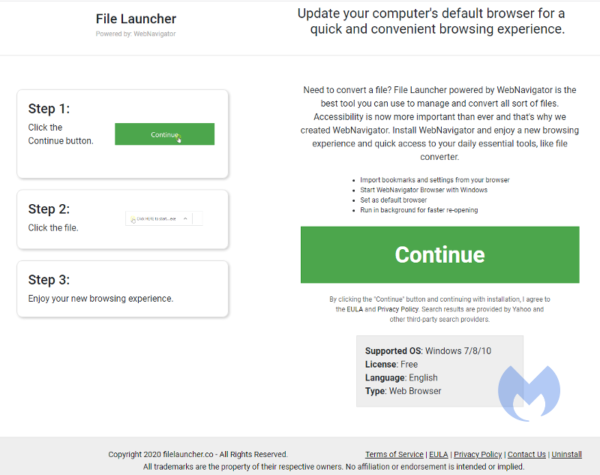
This type of layout is typically used to tell users how to install a Chrome extension, and the hijackers just changed the text in the boxes to make it fit them. Also note the line about Yahoo and other third-party search providers, that reminded me of a few search hijack extensions that were removed from the Webstore a while ago.
So, how is WebNavigator a search hijacker?
That was actually my third and most definitive clue. The WebNavigator Browser adds graphic search recommendations to the user’s search results, labelled “Search Recommendations”.
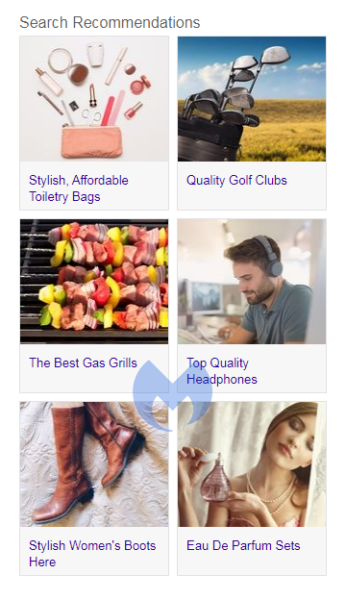
This ties them to the family of search hijackers which we have written about in detail before. For example, I found this set of search recommendations when I installed an extension called “IStreamingSearch”:
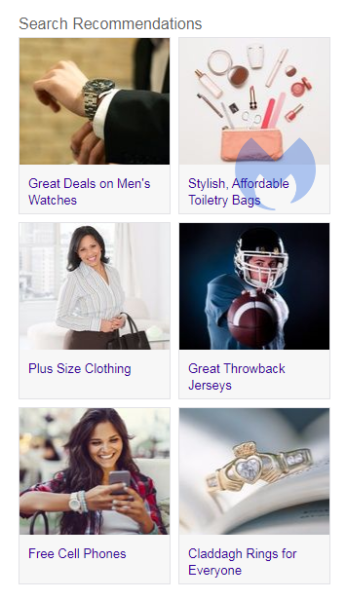
The difference in results could be caused by my use of a fresh Virtual Machine and a rotation of the VPN servers I use in Malwarebytes Privacy. But they sure look similar.
How can I stop and remove WebNavigator Browser?
Malwarebytes Premium users are protected against this PUP, and Malwarebytes will warn them when they try to install the WebNavigator Browser.
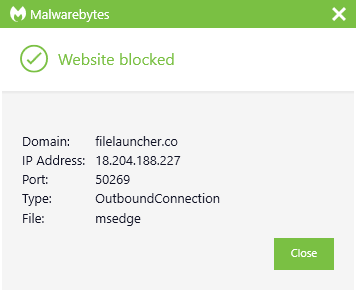
Malwarebytes Browser Guard, Premium, and EDR will block the domains promoting WebNavigator Browser.
If you’ve already installed the browser but now want to remove it, I have posted full removal instructions for the WebNavigator Browser on our forums.
IOCs
Domains:
- webnavigator.co
- fileleauncher.co
- tvlauncher.co
- digitalfileconverter.com
- fastmaps.net
- gamelauncher.co
- officelauncher.com
- streaminglauncher.com
Filenames:
- webnavigatorbrowser.exe
- CLICK HERE TO START THE WEBNAVIGATOR BROWSER INSTALLER_********_.EXE (where ******** are random letters and numbers)
Stay safe, everyone!
The post WebNavigator Chromium browser published by search hijackers appeared first on Malwarebytes Labs.
If you like the site, please consider joining the telegram channel or supporting us on Patreon using the button below.



