Well thanks anna-senpai for the Mirai source code release
Yeah, thanks a lot…. in-case you can’t tell its my sarcasm kicking in.
After doing heavy damage to KrebsOnSecurity and other web servers the creator of the Mirai DDoS botnet, a program designed to harness insecure IoT devices to run massive Distributed denial of service attacks, has apparently released the source code on Github. It tries various hardcoded root passwords, infects the device, and then sends out traffic to a preset target. You can see the code containing the hardcoded passwords in this file called scanner.c.
When Amazon, Twitter, PayPal, Spotify and other major websites were rendered inaccessible on Friday, thousands learned firsthand what a DDoS attack feels like.
Hackers used the botnet to send a 620 Gbps DDoS to KrebsOnSecurity, a popular security blog by Brian Krebs. The system, while powerful, is easily thwarted by rebooting the offending IoT device and it seems that updates are slowly reducing the number of potential targets in the wild. “With Mirai, I usually pull max 380k bots from telnet alone,” write Anna-senpai, the hacker who released the code on Hackforums. “However, after the Kreb [sic] DDoS, ISPs been slowly shutting down and cleaning up their act. Today, max pull is about 300k bots, and dropping.”
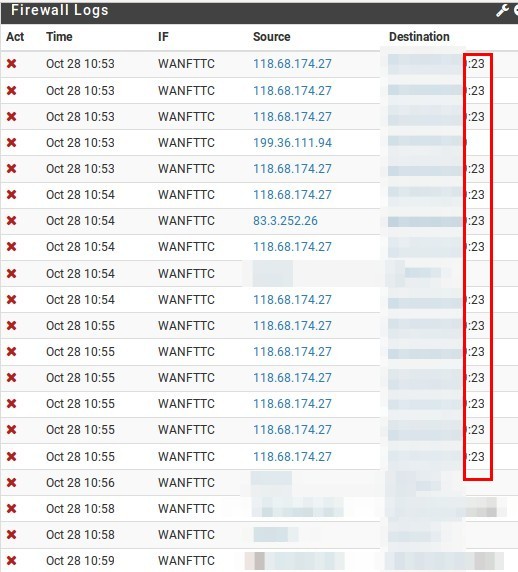
Thanks to this , i am now getting a daily battering on my firewall for people trying to find open telnet ports


